Hackers use a software called Facebook Email Search v1.0 to reveal millions of Facebook user email addresses, even if the addresses are private.
This user data, combined with the 553 million phone numbers that leaked from Facebook a few weeks ago, can help hackers access accounts or create a database with personal information of Facebook users.
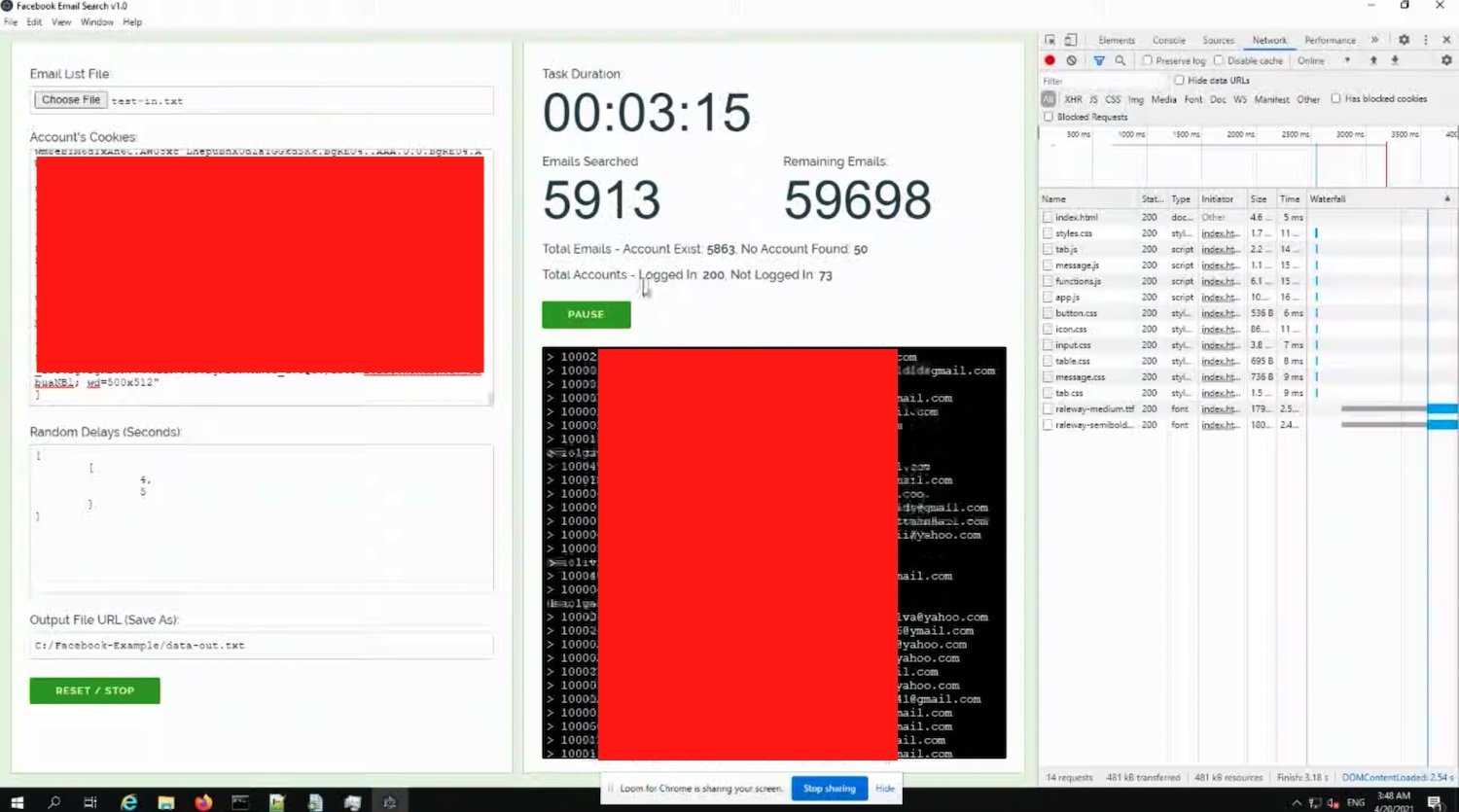
Facebook Email Search v1.0 uses a front-end vulnerability on the Facebook site. It automatically connects user IDs to the relevant email address, allowing a single hacker to secure about 5 million email addresses a day. Facebook says it fixed an almost identical vulnerability earlier this year.
In a conversation with Ars Technica, an anonymous researcher claims to have sent the vulnerability to Facebook, but the larger social network chose to ignore the matter. Facebook told the researcher that it "does not consider [the vulnerability] important enough to fix," despite the fact that it is a clear risk better safetys and infringement of the privacy of its users.
Facebook has not only ignored the vulnerability, but is actively encouraging PR representatives to downgrade and "normalize" data breaches. Read an internal Facebook email which was accidentally sent to a Data News reporter after the April 5 leak.
Hundreds of millions of Facebook users this month saw their data travel across the internet due to two ξεχωριστών κενών ασφαλείας του κοινωνικού δικτύου. Απέναντι σε αυτόν τον σημαντικό όγκο των δεδομένων, το Facebook ελπίζει να “κανονικοποιήσει” το φαινόμενο και υποστηρίζει ότι θα πρέπει να μάθουμε να ζούμε με τις data leaks. For a website obsessed with collecting data from its users, Facebook's negligence is troubling.
Facebook now states that it "accidentally closed this bug report before launching it to the appropriate group" and that it is currently investigating the issue. We do not know when the company will fix this security gap or how many accounts have been affected.





