A new form of mobile malware designed for multiple malicious activities has appeared, in the form of a camouflaged app that is a copy of the valid BatteryBot Pro app.
The fake app will provide the same mode to the victim with that of the original version of BatteryBot Pro, but at the same time it performs malicious activity in the background.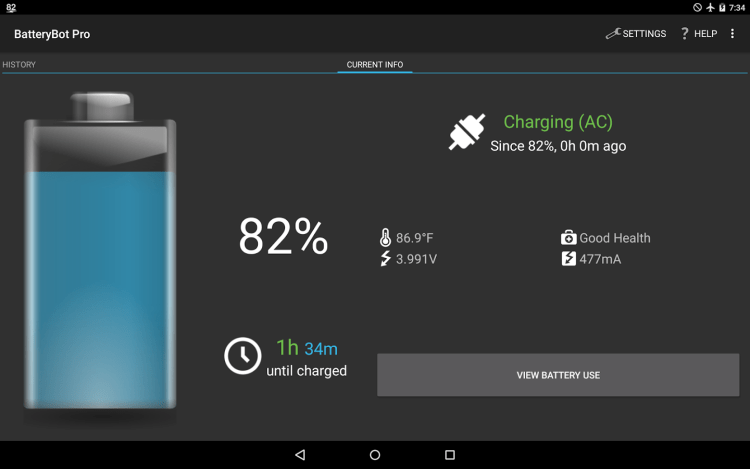
Mainly, although the app seems to work properly, back-end tries to load various ad libraries, eventually delivering a click-fraud campaign.
According to Zscaler, other features include adware fraud, SMS fraud, and installing additional malicious APKs.
The malicious app appears to be working normally. The main activity is the same as that of the genuine app, but when the user clicks on “View Battery Use,” the malware sends requests on command and control server για να ανακτήσει τους short codes για τους premium-rate SMS numbers. Το συνολικό κόστος των μηνυμάτων που στέλνονται θα προστεθούν στον account of the user.
App has been removed from the Play Store as soon as Google has been notified of its malicious activity, but for those who have already installed it is bad.
After installing the malicious app, administrative access is required, which allows the malware developer to have full control over the victim's device.
Running with administrator privileges means that the user and owner of the infected device can not remove it after installation.
The camouflaged fake Android apps are all too common to each other. While the genuine BatteryBot Pro app required the minimum of licenses, the fake app required full admin access in order to gain full control over the victim's device.
For this reason, users must be suspicious and very careful and research a lot about the licenses before deciding to install an application on their mobile device.





