HTTP Strict Transport Security (HSTS) was designed to help secure websites (those using HTTPS), telling web browsers that they should only communicate over HTTPS with the server to protect connections from downgrade attacks and cookie theft.
Mozilla supports HSTS in Firefox versions from 2014.
Ars Technica meanwhile was among the first to raise concerns about the HSTS feature in web browsers, as it allowed companies to plant supercookies in browsers using the same technology designed to improve end-user security.
For the true reason, you can check your browser on a demo site created by Sam Greenhalgh.
If you visit the site with a browser that supports HSTS, it will show you a unique ID that allows websites to monitor you.
Here we have to mention that problem δεν περιορίζεται μόνο στον περιηγητή ιστού Firefox αλλά και στον Google Chrome and other browsers that use the HSTS feature.
But let's see what Firefox does with HSTS.
The Mozilla Foundation browser stores them information from HSTS mode to SiteSecurityServiceState.txt, a file you will find in the path
C: \ Users \ Configuration \ AppData \ Roaming \ Mozilla \ Firefox \ Profiles \ 5f1kfxah.dev-edition-default
In the path above, instead of the iguru user, choose the user you have on your PC. Also the name of the last folder may change.
If you open the file with a plain text editor, you will see a list of domain names, values associated with them, and an expiration date.
Let's now look at how you can avoid tracking from sites using supercookies.
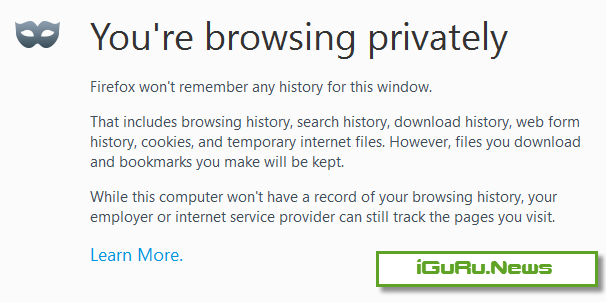
Firefox also has a private browsing experience.
With normal browsing mode: HSTS is stored on your computer, from every page that serves supercookies. Private browsing mode: however deletes any HSTS information after the session.
Protection against HSTS tracking
1. You only use private browsing
Firefox will delete all HSTS information after closing the page. For now this is the best option to prevent watching by supercookie without risking your security.
To start Firefox in private browsing mode, use the three-button Ctrl-Shift-P combination.
2. Delete all data stored on your computer after each web browsing.
The second option is somewhat. Whenever you close your Firefox browser, you should remember to delete the data that the web pages save on your computer. So with all the others, the HSTS data stored in the file SiteSecurityServiceState.txt.
3. Remove the entries from the HSTS file manually
The HSTS file, SiteSecurityServiceState.txt. can be easily deleted using a simple word processor.
Make sure Firefox is closed before you can.
This method gives you complete control over the data stored on SiteSecurityServiceState.txt. but requires manual intervention regularly, which may make it inappropriate.
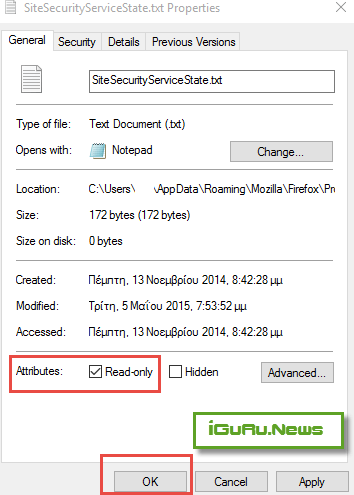
4. Make the SiteSecurityServiceState.txt file read-only
This is the most radical approach as Firefox will not be able to write new HSTS information.
To make the file "read only" right-click on the file and select Properties from the menu. Tick to read only and click OK to apply the change.