The Kaboom is an automation for penetration testing. It performs many tasks for the two πρώτες φάσεις του τεστ: συλλογή πληροφοριών και αξιολόγηση vulnerabilitys. All information collected is stored hierarchically which is very simple to search (same in the case of multiple targets).
Specifications
- Customization (see above)
- Multi-target specification
- You can specify up to 254 hosts (C-class network)
- New CLI interface
- More powerful Nmap scan
- Better directory hierarchy
- Automatic research of Metasploit module associated with CVE code found
- Recognition of services exposed on non-canonical ports (ex: http on 7000)
- Print out and save credentials found
Details
Kaboom performs several tasks:
- Information Gathering
- Port scan (Nmap)
- Web resources enumeration (Dirb)
- Vulnerability assessment
- Web vulnerability assessment (Nobody - Dirb)
- Vulnerability assessment (Nmap - Metasploit)
- Automatic Vulnerabilities research (Searchsploit - Metasploit)
- Dictionary Attacks (Hydra)
- SSH
- POP3
- IMAP
- RDP
Use
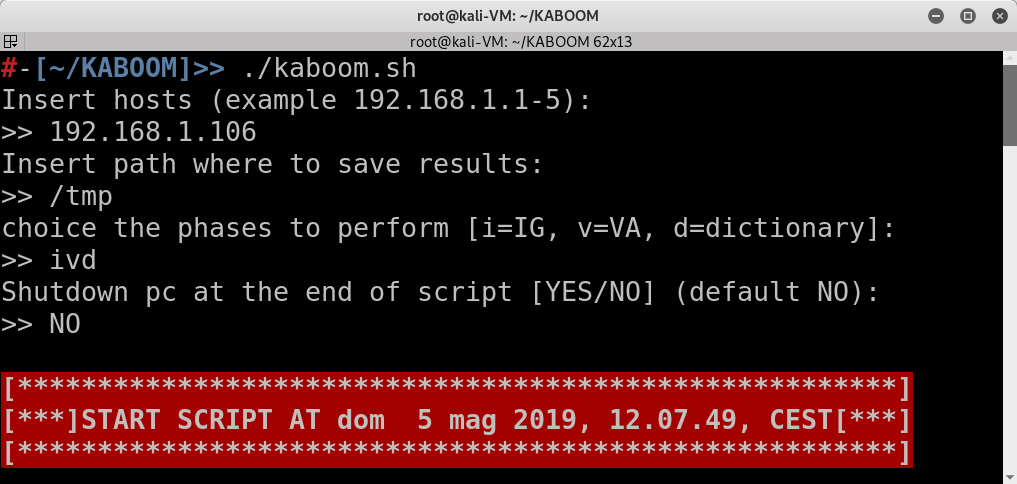
Kaboom can be used in two ways:
- Interactive mode:
kaboom [ENTER], and the script does the rest
- NON-interactive mode:
kaboom -t
If you want to see help:
kaboom -h (or –help)
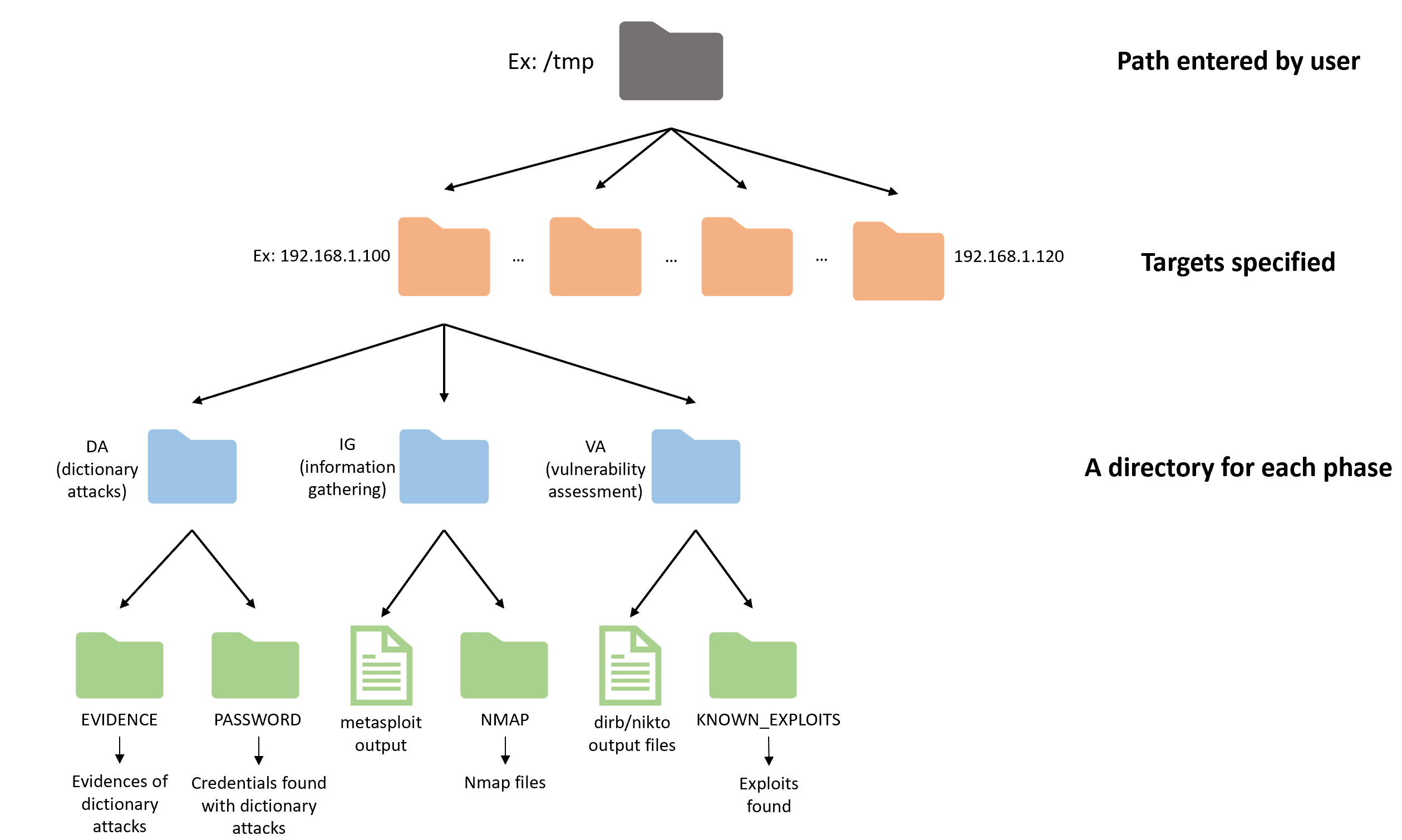
Hierarchy
Download the program from here.





