WinRAR, the popular program compressionς αρχείων, έχει μια ευπάθεια ασφαλείας που επιτρέπει στους επιτιθέμενους να εκτελέσουν απομακρυσμένο κώδικα στον υπολογιστή του χρήστη κατά το άνοιγμα ενός SFX archivey (self-extracting file).
The error discovered by Mohammad Reza Espargham from Vulnerability Lab, as well as by Pieter Arntz from Malwarebytes.
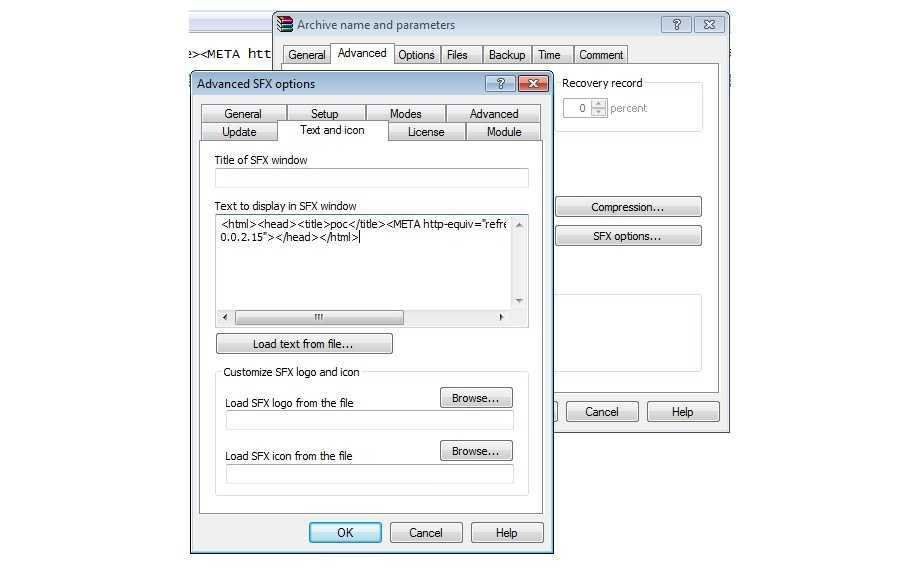
According to reports from both, the bug only affects the latter version of WinRAR, 5.21, and can be used by any attacker who manages to insert malicious HTML code into the "Text to display in SFX window" section when creating a new SFX file.
After sending the file to a victim, malicious code is executed each time the file starts, and depending on the attacker's ability, it could compromise the system, network, or simple device. The attackers do not need special privileges on the target machine to exploit this vulnerability.
Because RAR and SFX files are used on a daily basis by a number of users, hackers have a high chance of using this bug out there.
A video - proof of the vulnerability is the following by Mohammad Reza Espargham.





