ESET researchers discovered a new one backdoor cuts, which was used for a cyberattack on a freight company in South Africa, which they called Vyveva.
The researchers attributed the malware to the famous Lazarus team because of its resemblance to the group's previous operations, as well as to the malware used by that team. Backdoor includes several cyber espionage capabilities, such as transferring files and gathering information from the target computer and its drives. Vyveva communicates with the Command & Control (C&C) server over the Tor network.

H telemetry ESET's analysis of Vyveva indicates that this is a targeted cyberattack, as ESET researchers have identified only two infected machines, both of which are servers owned by the South African company. According to ESET's research, Vyveva has been in use since at least December 2018.
“Vyveva has many code similarities to earlier Lazarus team programs identified by the technology by ESET. However, the similarities do not stop there: the use of a fake TLS protocol in network communication, the way of executing line commands and the use of encryption services and the Tor network indicate that we are talking about the Lazarus group. Therefore, we can very confidently attribute the Vyveva malware to this APT group,” says its researcher ESET, Filip Jurčacko, who analyzed the Lazarus team arsenal.
The backdoor cuts executes commands issued by cybercriminals, such as file operations and bwork and information gathering. There is also a less commonly seen command for “file timestomping”, which allows copying timestamps from a “donor” file to a destination file or using a random date.
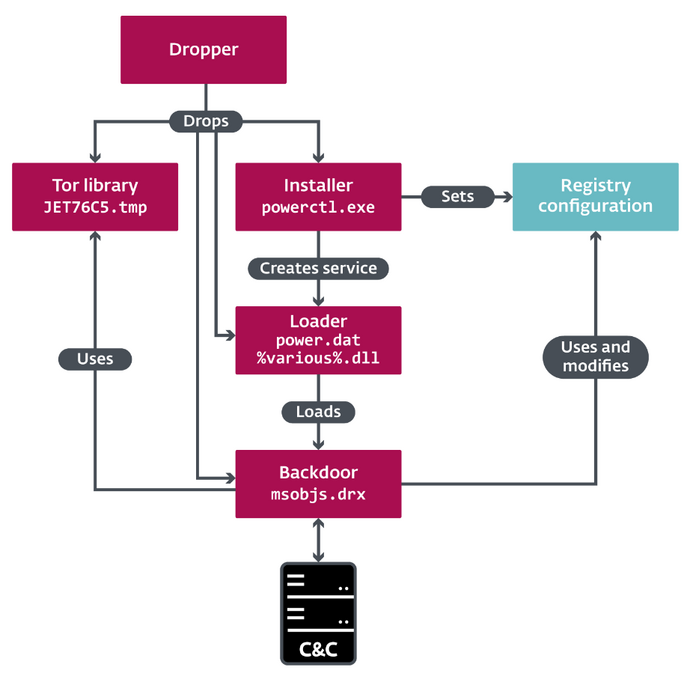
Vyveva uses the library Tor to communicate with a C&C server. Communicates with C&C at three-minute intervals, sending information about the infected computer and its drives before receiving orders.
"However, of particular interest are the watchdogs used to monitor recently connected and disconnected disks, and a Session watchdog that monitors the number of active sessions, such as logged in users. These elements can cause a connection to the C&C server outside of the predefined three-minute interval," explains Jurčacko.
You can read more technical details about Vyveva in the blog post “(Are you) afraid of the dark?"
Overview of the structure of Vyveva