ESET unveils EmissarySoldier: The team campaign APT LuckyMouse attacks government networks and private companies (telecommunications, media and banks) in Central Asia and the Middle East
• The research included in the Report of the global cybersecurity company ESET on the Public Sector and which incorporates opinions of the European Commission, the CERN and Europol, was recently presented at a virtual conference for ESET Europe Cyber Security Day.
• The biggest challenge and a common enemy for all governments are advanced persistent threat groups (APTs).

The European Union's cybersecurity strategy, like the strategy of all governments internationally, is challenged not only by the adoption of the "digital by default" principle, but also by the COVID-19 pandemic, by the mass application of teleworking (from home), as well as threats such as cyber espionage, ransomware and supply-chain attacks. But the biggest challenge of all, and a common enemy for all governments, is the Advanced Persistence Threat (APT) teams.
APT teams utilize sophisticated tools
ESET's global Public Sector's report on public sector was recently presented at a virtual conference for ESET Europe Cyber Security Day. The report examines the potential threats posed by APT teams, highlights their complex nature, and focuses on the EmissarySoldier campaign, a malicious campaign launched by the APT LuckyMouse team using the SysUpdate toolkit to attack machines, some of which ran Microsoft SharePoint application.
This analysis της ομάδας LuckyMouse εξετάζει το σχετικά άγνωστο σετ εργαλείων SysUpdate – τα πρώτα δείγματα του οποίου ανακαλύφθηκαν το 2018. Από τότε, η εργαλειοθήκη έχει δει διάφορα στάδια ανάπτυξης. Η ομάδα LuckyMouse εγκαθιστά το malware by applying a three-component strategy: a legitimate DLL exploit, a custom DLL file that loads a malicious file, and a raw binary payload file encrypted with the Shikata Ga Nai algorithm.
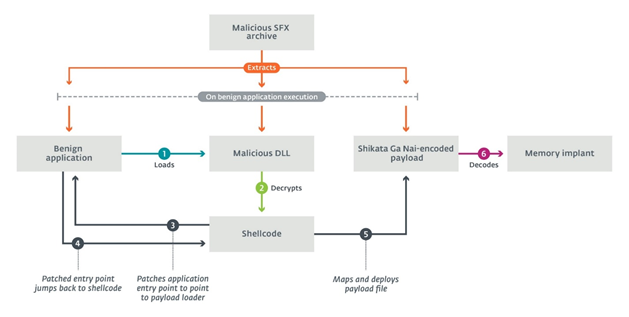
Overview of the three-element model
Since SysUpdate's modular architecture allows its operators to limit the exposure of malicious objects at will, ESET researchers were unable to recover any malicious fragment and believe that this will be an ongoing challenge in future investigations.solutions. However, the LuckyMouse team increased its activity in 2020, possibly going through a retrofit process where various features were gradually integrated into the SysUpdate toolset.
Monitoring the evolution of tools exploited by APT groups such as the LuckyMouse group is a key concern, as governments have a responsibility to ensure stability for citizens, the business environment, and cooperation with other nation-states. These duties bygovernmentare threatened as LuckyMouse and other APT groups, including government agencies and their partners, target broad collaboration platforms such as Microsoft SharePoint and digital service delivery.
The Public Sector in focus
In 2020 and 2021, several ESET research collaborations matured, including collaborations with the European Organization for Nuclear Research (CERN), the European Police Office (Europol) and the French Information Systems Security Agency (ANSSI). As highlighted in the virtual event and in the report, governments and their IT infrastructure are considered to be the default targets.
According to the report, technology experts must continue to support governments in closing security gaps and monitor the tactics, techniques and procedures of APT teams through the various Endpoint detection and protection technologies available to them.





