In 2019, Kaspersky blocked attacks carried out by Shlayer, a malicious Trojan family, on at least 10% of devices using solutions Kaspersky for Mac protection, making this threat the most prevalent for MacOS users. A clever malware distribution system spreads through a network of affiliates, entertainment websites and even Wikipedia, proving that even users who only visit legitimate sites still need extra protection when online.
Despite the fact that macOS is traditionally considered a much safer system, there are still digital criminals who attempt to take advantage of users of this software. Based on Kaspersky's statistics, Shlayer is a good example. Specializes in installation adware - programs that intimidate users by distributing illegal ads, spying and collecting searches from users' browsers, modifying search results to distribute even more advertising messages. The percentage of Shlayer in the total attacks on macOS devices recorded by Kaspersky products in the period January-November 2019 amounted to almost 1/3 (29,28%).
The process "contaminations” often consists of two phases – first the user installs Shlayer and then the malware installs a selected type of adware. However, device “infection” starts with an unsuspecting user downloading the malware. To achieve installations, the threat actor behind Shlayer has created a malware distribution system with a number of channels that lead users to "download" the malware.
shlayer is offered as a way to monetize websites through various affiliate advertising programs, with a relatively high payment for every malware installation made by US users, with more than 1.000 "partner sites" distributing shlayer.
This scheme works as follows: a user searches for a TV series episode or a football match and the ad pages redirect them to fake Flash Player update pages. From here the victim will "download" the malware. Thus, the partner who distributes links to the malware receives payment for each installation.
Other systems lead to a fake Adobe Flash update page that redirects users from various major online services visited by millions of users, including YouTube, where links redirected to the malicious site were included in the video descriptions, and Wikipedia, where such links were hidden in the article references.
Users clicking on these links were also redirected to the main Shlayer download pages. Kaspersky's researchers found 700 malicious domains, links to which were found on various legitimate websites.
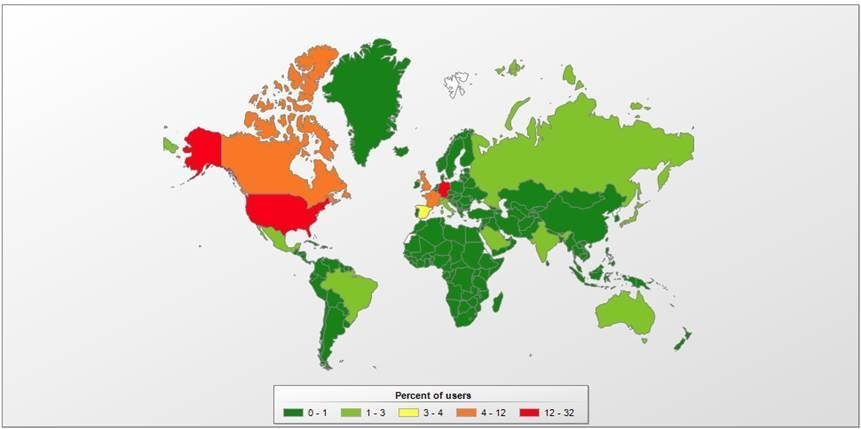
Almost all websites that lead to a fake Flash Player had content in English, with the USA (31%), Germany (14%), France (10%) and the United Kingdom (10%) being the countries that received the most attacks.
"The macOS platform is a good source of revenue for cybercriminals, who are constantly looking for new ways to mislead users, and are making extensive use of social engineering techniques to spread their malware. This case demonstrates that such threats can be found even on legitimate websites. Fortunately for macOS users, the most common threats currently targeting macOS revolve around distributing illegal ads rather than something more dangerous, such as stealing financial data. "A good cybersecurity solution can protect users from threats like these, making the web browsing experience safe and enjoyable," said Anton Ivanov, a security analyst at Kaspersky.
To reduce the risk of "infection" with Trojans such as Shlayer, Kaspersky recommends:
- Install programs and updates only from trusted sources.
- For more information on the entertainment site you plan to visit:
- Scan his name online and try to find comments about that.
- Use a reliable security solution that provides advanced protection for Macs as well as PCs and laptops.
More information can be found at special website Securelist.com.






