The "Cyber Attack Trends: 2022 Security ReportReveals the main cyber trends from 2021, including the "frenzy" of supply chain attacks and the increased disruption in daily life. Education and Research have emerged as the most targeted industry.
-
Cyber-attacks against organizations worldwide increased by an average of 50% in 2021, compared to 2020.
-
Education and research were the most targeted areas, with organizations facing an average of 1.605 attacks per week.
-
The suppliers software showed the largest year-over-year growth, up 146%.
Η Check Point Research (CPR), This makes it a perfect choice for people with diabetes and for those who want to lose weight or follow a balanced diet. Threat Intelligence part of Check Point Software Technologies Ltd., a provider of cybersecurity solutions worldwide, published the Security Report of for 2022. From attack on Solarwinds at the beginning of last year, which presented a whole new level of complexity and spread, by December and inflow of his vulnerabilities Apache log4j, 2022 Security Report reveals the key players attackand the techniques observed by CPR in 2021.
In total in 2021, the organizations suffered 50% more weekly cyber attacks than in 2020. Out of the total, 1.605 weekly attacks were related to the Education / Research sector that led (75% increase). It was followed by the Government / Armed Forces sector with 1.136 weekly attacks (47% increase) and the Communications sector with 1.079 weekly attacks (51% increase). Software vendors showed the largest growth year on year (146%), which is in line with the ever-increasing trend of attacks on the software supply chain observed in 2021. Also in 2021, there were evolving attacks on mobile devices, an increase in significant vulnerabilities in services cloud and the return of the infamous botnet emote.
The main points from 2022 security report include:
-
Supply chain attacks: her infamous attack Solarwinds laid the groundwork for a supply chain frenzy. In 2021 there were numerous sophisticated attacks, such as those in codecov in April and in Cashier in July, completed with vulnerability log4j unveiled in December. The striking impact of this vulnerability on an open source library demonstrates the enormous risk inherent in software supply chains.
-
Cyber-attacks that disrupt daily life: In 2021 there was a large number of attacks targeting critical infrastructure that led to a huge disruption of citizens' daily lives and in some cases even threatened their sense of physical security.
-
Attack on Services Cloud: The vulnerabilities of providers cloud created much more concern in 2021 than in the past. Vulnerabilities exposed throughout the year allowed attackers, for different time frames, to execute arbitrary code, escalate to root, gain access to massive amounts of private content, and even intersect between different environments.
-
Developments in the mobile landscape: Throughout the year, threat actors increasingly use the smishing (SMS phishing) for distributing malware and have invested heavily in breaking into Social Media accounts to gain access to mobile devices. The continuous digitization of the banking sector in 2021 led to the introduction of various applications designed to limit physical interaction, which in turn led to the distribution of new threats.
-
Cracks in the ecosystem ransomware: Governments and law enforcement agencies have changed their attitude towards organized groups ransomware in 2021 and turned from prevention and reaction, to proactive offensive businesses against operators ransomware, their funds and support infrastructure. The big change happened after her incident Colonial pipeline in May that made the Biden government realize that it needed to step up its efforts to combat the threat ransomware.
-
His return Emotet: One of the most dangerous and infamous botnets in history, returns. From his return Emotet in November, the CPR found that the malware activity was at least 50% of that observed in January 2021, shortly before its initial removal. This upward trend continued throughout December with several campaigns at the end of the year and is expected to continue in 2022, at least until the next abolition effort.
"In a year that began with the aftermath of one of the most devastating supply chain attacks in history, we have seen increased confidence and complexity in the movements of threat agents," she said. Maya Horowitz, VP Research in Check Point Software. "The climax was achieved by exploiting the vulnerability log4j, which, once again, has captured the security community and brought to the fore the enormous level of risk inherent in software supply chains. In the intervening months, we saw services cloud to be attacked, threatening agents to focus on mobile devices, the pipeline Colonial to be held hostage for ransom and the revival of one of the most dangerous botnets in history ”.
Continuing on Maya Horowitz he said:
"But not everything is so catastrophic. The ecosystem ransomware suffered cracks in 2021 as governments and law enforcement agencies around the world decided to take a tougher line specifically on these groups. Instead of reacting with corrective action, some shocking events have awakened governments to the need to take a more proactive approach to cyberbullying. The same philosophy extends to businesses, which can no longer afford to take an unrelated approach to responding to holiday threats. "They need to have 360-degree access to real-time threat information and a security infrastructure that can be mobilized in an effective, coordinated manner."
Categories of cyber attacks by area in 2021: 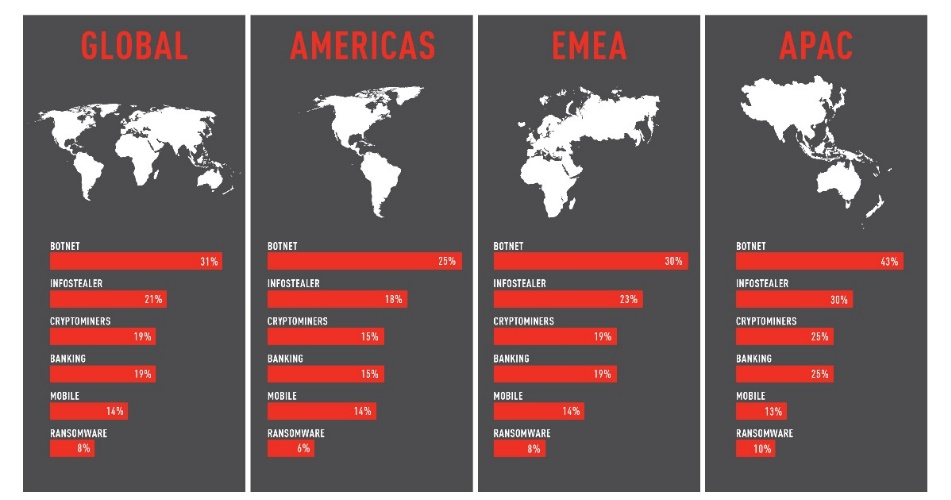
Average weekly attacks per organization, per sector 2021, compared to 2020: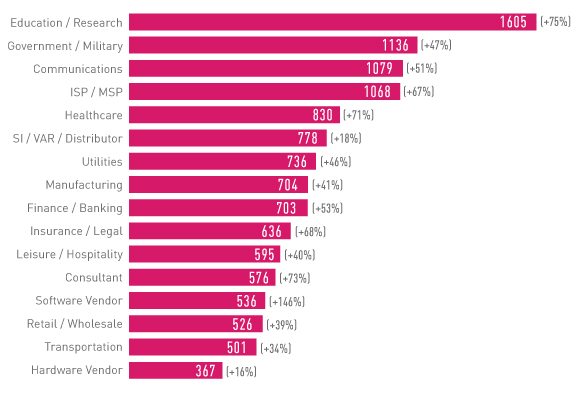
The 'Cyber Attack Trends: 2022 Security Report' provides a detailed overview of the cyber threat landscape. These findings are based on data from Check Point Software's ThreatCloud Intelligence between January and December 2021, highlighting the key tactics cybercriminals use to attack businesses.





