Microsoft seems to have fixed a loophole security in Windows Defender that was circulating exploits online.
Vulnerability implementationof remote code in Microsoft Defender (CVE-2021-1647) turned the Windows security application into an attacker, triggering its execution maliciousy software when scanning the malware, instead of isolation and the deletionhis.
This means that if a file is sent via email or a USB drive, the automatic scan will download to your computer, instead of isolating the malware, it will activate it immediately.
Exploit has been fixed in Patch Tuesday of the 12th and was one of 80 defects encountered by Microsoft developers.
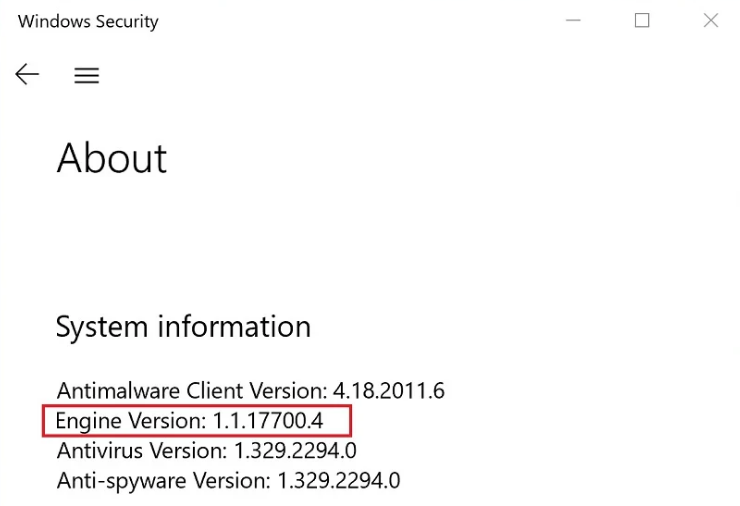
To check if you are currently protected, simply check the scan engine version number in Windows Security. Open the application and check in Settings - About.
From the release 1.1.17700.4 and above the application is secure.
At least until the next 0day.





