Forget what we said before…. Hackers exploit a vulnerability that affects the Microsoft Defender application in Windows to learn sites that are not scanned to install malware there.
The vulnerability has been around for at least eight years, according to some users, and affects Windows 10 from version 21H1 to 21H2.
Like any protection application, Microsoft Defender allows users to add locations (local or in network) on their systems that want to be excluded from malware scans.
So there are many who add exceptions to antivirus that make it easier for other applications that are incorrectly detected as malware.
Of course the list of scan exceptions varies from user to user. This information is very useful for an attacker as he knows where the malware can be stored to avoid detection.
So security researchers discovered that the list of sites excluded from Microsoft Defender scanning is not protected and any local user can have access to her.
Local users can query the registry and find out which paths Microsoft Defender is not allowed to scan for malware or dangerous archives , and they don't even need administrator rights.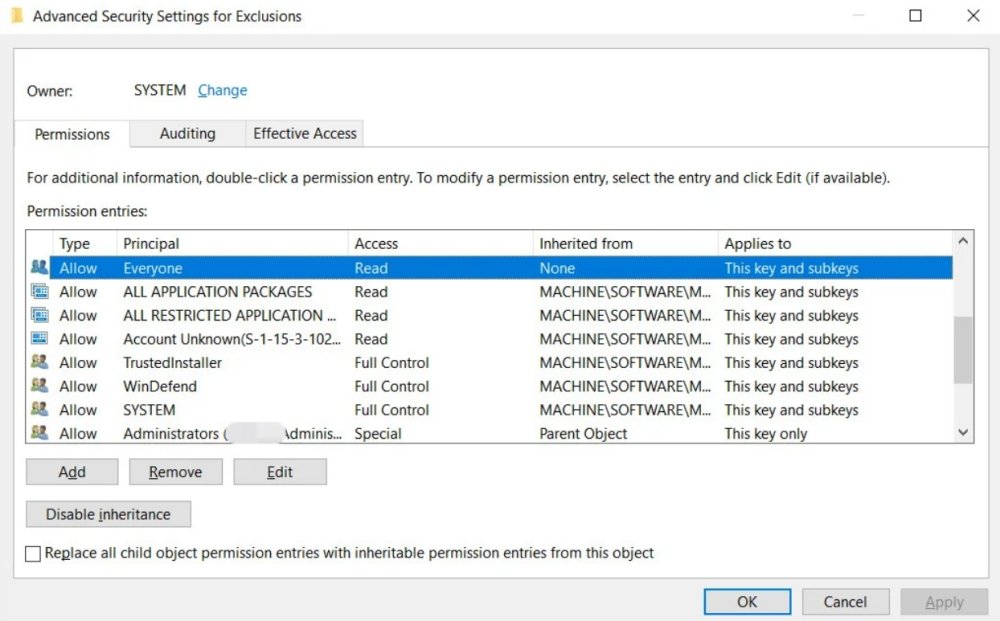
Antonio Cocomazzi, a security researcher at SentinelOne, reports on Bleepingcomputer. that there is no protection for this information, which should be considered sensitive, and that running the “reg query” command reveals all the instructions Microsoft Defender has received to scan files, folders, extensions or processes.
Windows Defender AV allows Everyone to read the configured exclusions on the system 🤦
reg query "HKLMSOFTWAREMicrosoftWindows DefenderExclusions" / s pic.twitter.com/dpTFwMVRje
- Antonio Cocomazzi (@splinter_code) January 12, 2022
Another researcher, Nathan McNulty, confirmed that the problem exists in versions 21H1 and 21H2 of Windows 10, but does not affect Windows 11.
Finally, for those configuring Defender AV on servers, be aware that there are automatic exclusions that get enabled when specific roles or features are installed
They do not cover non-default install locations, and you should review the list here:https://t.co/StYXMmfs8T
- Nathan McNulty (@NathanMcNulty) January 12, 2022
McNulty also confirmed that one can obtain the list of exceptions from the registry with entries that store political group settings. This information is very sensitive as it provides exceptions for many computers.





