Monero mining ή Bitcoin mining: Due to the price of Bitcoin and other cryptocurrencies, mining has become a common target for hackers trying to turn every stolen computing resource into cash.
The makers of anti-virus and anti-adware programs have responded immediately by trying to stop any code that allows CPU mining, especially through browsers.
For those interested in breaking the law, sorry to do a little research on it better safetyof computers, a Spanish programmer with the alias Arnau, published a PoC which describes how to use public Wi-Fi networks for mining.
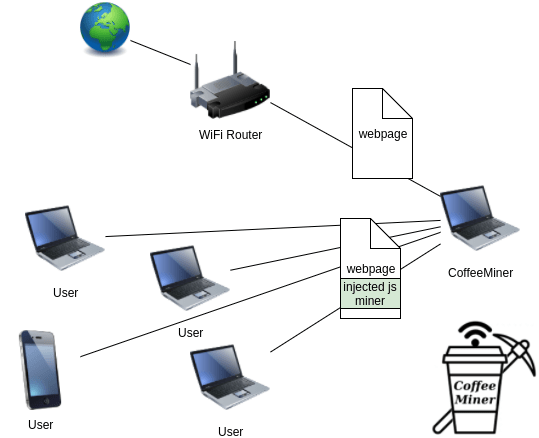
His project is called CoffeeMiner, and allows a kind of man-in-the-middle that is used by hackers usually in cafes that have free Wi-Fi.
The CoffeeMiner script is designed to spoof Address Resolution Protocol (ARP) messages on a local network, in order to intercept encrypted traffic from other devices on the network.
The attack is carried out by man-in-the-middle using a software called mitmproxy to inject the following line of HTML code into non-HTTPS or non-encrypted web pages browsed by network visitors:
![]() When loaded, these web pages run JavaScript and build Monero on the computer CPU using CoinHive encryption software.
When loaded, these web pages run JavaScript and build Monero on the computer CPU using CoinHive encryption software.
As Arnau explained, the attack can be automated. The published version does not work with requests for HTTPS websites, although adding sslstrip could solve the problem.
The code is mostly Python, and it is available at GitHub.





