Edward Snowden may be the most notorious NSA agent for the leak of secret government records, but Harold Martin's partner is the one who has been the largest stealing of classified information in US history.
Martin, 51, was arrested during an FBI raid on his home in late August. He is accused of stealing dozens of computers and thousands of documents. The NSA partner managed to collect more than 50 terabytes (50.000 gigabytes) of data from government computers over two decades. So although his charges were initially misdemeanors they were quickly changed to charges for espionage – partly because of the sheer amount of data he stole.
At the moment no one knows how the authorities got to Martin, and of course the biggest question is how he was able to steal so much data - and go unnoticed - for so long.
Former NSA employees who spoke anonymously said Martin is likely to steal the files just by going through the front door.
"The security service is carrying out random checks on bags and wallets of people leaving the service, but no one is checking the contents of the pockets," said a former official who spent almost 30 years in the service before leaving the post. decade.
"Anything that could fit in a pocket and go unnoticed," the former NSA official continued.
A second employee, who left the office at about the same time, agreed.
"Practically, it is not possible to check all employees. Give some thought to Ft. Meade, the former employee said, hinting at how bad the system is security. About 30.000 employees work at the NSA headquarters in Ft. Meade of Maryland. It would take hours to check every person leaving the building.
A second former employee reported that the vast majority of employees go through extensive interviews before being hired, so there is an inherent loyalty to service personnel. James Clapper, director of the National Intelligence Service, said in 2014 that there were no "mousetraps" to catch another Snowden because the agency's security "is based on personal confidence. "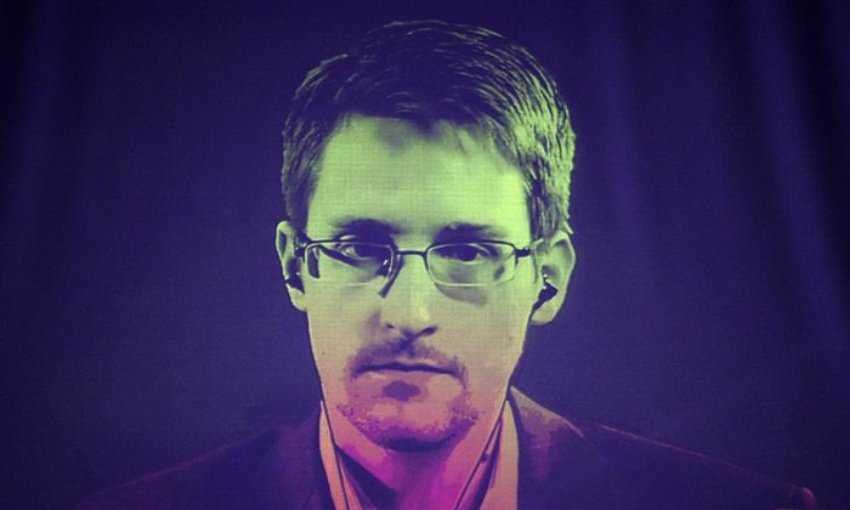
The indictment does not say exactly how Martin stole the data from NSA computers and servers, as these systems (work) are a seven-secret secret to national security.
When asked, the former employees reported:
"Based on what he got, it looks like [Martin] should have used USB drives," said the first official. USB storage has grown in size over the past two decades, and Martin theft has reportedly been a painfully slow process.
The second official said it would not be difficult to steal the data, noting that the NSA has "some of the best hackers on earth."
There are many parallels with the Snowden case, mainly because it has not yet been known how he managed to extract the data from the NSA systems.
But, according to a report, Snowden needed “a few drives and the willingness to take advantage of one black hole to an antiquated security system.” One source said at the time that the NSA in 2013 was "stuck on 2003 technology."
"I'm pretty sure he could find a way to do it without being detected," the former employee said, without elaborating, adding that the systems would most likely not be able to stop the leak of "specialized confidential information."
In the indictment, Martin appears to have boasted in a letter found by the FBI that he had "seen more or less all the tech secrets of COMPUSEC [the NSA]."
He said the NSA systems were not as safe as it is believed to be.
However, little is known about Martin. According to page at LinkedIn, spent many years as a partner and consultant, and worked as a consultant for technical studies at the Department of Defense.





