Security researchers have discovered a way of hacking in Android and iOS apps. In a nutshell, researchers could connect remotely to applications that violate them without the victim knowing it.
A team of three researchers from Hong Kong Chinese University (Ronghai Yang, Wing Cheong Lau and Tianyu Liu) discovered a vulnerability that affects most of the popular mobiles that support single sign-on (SSO) by applying OAuth 2.0 .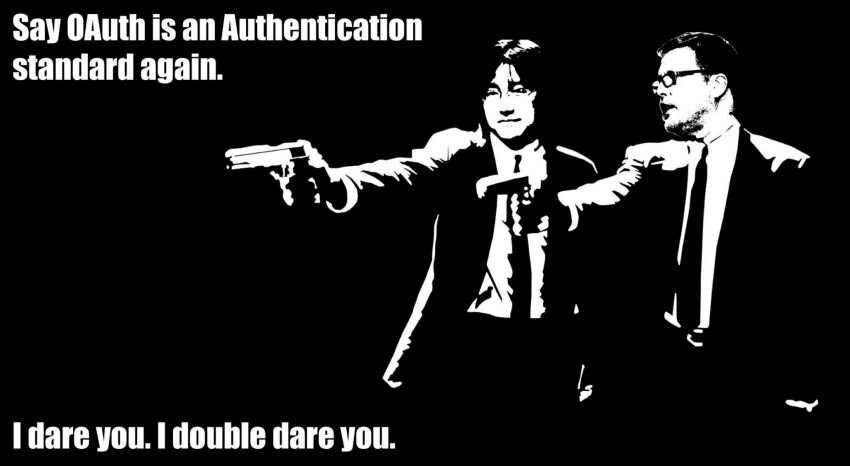
OAuth 2.0 is an open standard for authorization that allows users to connect to third-party services without performing any enrollment. They simply verify their identity with accounts of Google, Facebook, or other major companies.
Let's see how:
When one user connects to a third-party app using the OAuth standard, the app will need to check with the ID provider, say Facebook. The application will try to find out if the data ID cards is correct. After doing so, OAuth grants access to Facebook's 'Access Token' which is then delivered to the mobile app server.
Once the access token is issued, the application server requests user authentication information from Facebook, checks them, and then grants a login to the user with the credentials it uses on Facebook.
Where is the error?
Researchers have found that Android app developers do not properly check the validity of information sent by identity providers such as Facebook or Google.
Instead of verifying OAuth (Access Token) information if the user and the identity provider are logged in, the application server only checks for the username used by the authentication provider.
Because of this malfunction, a remote hacker can download the vulnerable application, connect with its own data, and then change the user name to the person who wants to attack by setting up a server to modify the data sent from Facebook , Google or some other identity provider.
Once this is done, the hacker has complete control over the data that exists within the application according to Forbes. Imagine being a banking application…
"The OAuth protocol is quite complex," Lau told Forbes.
"Many application developers do not have the ability. "Most of the time they use Google and Facebook credentials, but if they don't do it right, their apps are wide open."
Researchers have discovered hundreds of popular Android apps that are vulnerable as they support SSO with a total of more than 2,4 billion downloads.
Taking into account the number of users choosing OAuth links, researchers estimate that over one billion different application bills are at risk.
The researchers did not test the exploits on iPhones, but believe that the attack them could work on any vulnerable app on Apple's iOS.
Yang and Lau presented their research work entitled Signing into One Billion Mobile App Accounts Effortlessly with OAuth2.0 at the conference Black Hat Europe on Friday.





