Operation Ghoul: Kaspersky Lab has discovered a new wave of targeted attacks against the industrial and mechanical industries in many countries around the world. Using Messages (e-mail) spear-Phishing and malware based on a commercial spyware Kit, criminals are trying to extract valuable business data stored on their victims' networks.
In total, more than 130 organizations from 30 countries, including Spain, Pakistan, the United Arab Emirates, India, Egypt, the United Kingdom, Germany, Saudi Arabia, etc., have been the victims of successful attacks by this group.
In June of 2016, Kaspersky Lab's researchers identified a spear of spear-phishing messages that included malicious attachments. These messages were mainly sent to top and middle executives of many companies.
The emails sent by the attackers seemed to come from a bank in the UAE, while they looked like bank payment advice and included a SWIFT attachment, but in fact the attached file contained malicious software.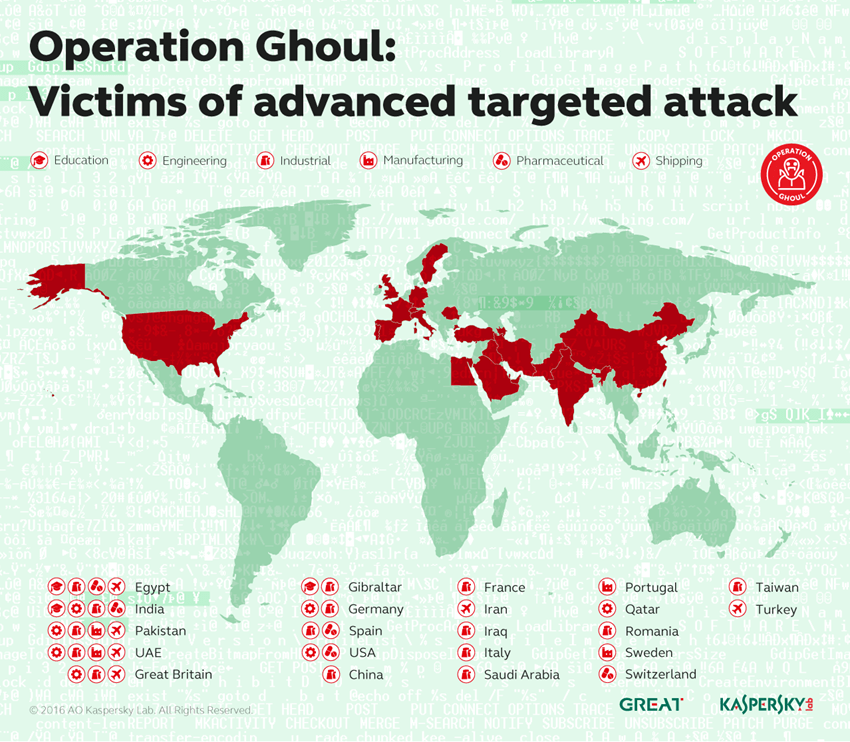
Further research by Kaspersky Lab researchers has shown that this spear-phishing campaign has probably been organized by a group of digital criminals, first identified by the company's researchers in March of 2015. The June attacks seem to be the most recent action of this group.
The malicious software found in the attached file is based on Hawkeye software, a commercially available spyware program that is sold overwhelmingly to Darkweb. This program provides a wide range of tools that attackers can use. After installation, it collects interesting data from the victim's computer, including:
- Keystrokes
- Copied data to clipboard
- Data from an FTP server
- Account details from browsers
- Account details from instant messaging platforms (e.g., Paltalk, GoogleTalk, AIM)
- Account details from e-mail client applications (eg Outlook, Windows Live Mail)
- Information about installed applications (eg Microsoft Office)
This data was then sent to Command & Control servers του απειλητικού φορέα. Με βάση τις information που προέκυψαν από κάποιες «τρύπες» σε ορισμένους Command & Control servers, η πλειοψηφία των θυμάτων είναι οργανισμοί που δραστηριοποιούνται στους τομείς της βιομηχανίας και της μηχανολογίας, καθώς και Companies from the shipping, pharmaceutical, manufacturing, commercial and educational industries, among others.
All these businesses have valuable information that could then be sold on the black market. The economic gain is the main motivation of the attackers behind Operation Ghoul.
Operation Ghoul, as it was named by Kaspersky Lab researchers, is just one of the many campaigns that are supposed to be controlled by the same digital crime group, which remains active.
"According to ancient Folklore, the Ghoul is a demon that is found in the myths of Mesopotamia, a bad spirit that devours human flesh and chases children. Today, this word is sometimes used to describe an avid or materialist man. This is a fairly accurate description of the team behind the "Surgery Ghoul". The main motivation of criminals is the financial gain from the sale of stolen intellectual property and business information or from attacks on the bank accounts of their victims. Unlike agents attacking government agencies that choose targets carefully, this group, like others, can potentially attack each company. Even if they use relatively simple malicious tools, they are very effective in attacking them. So companies that are not prepared to track down these attacks will unfortunately suffer, said Mohammad Amin Hasbini, an expert on issues Kaspersky Lab security.
To protect businesses from Operation Ghoul and other similar threats, Kaspersky Lab researchers are recommending the following steps:
- Particular emphasis should be placed on staff training so that business executives are able to recognize messages or links used as spear-phishing tools.
- A key element for business protection is the use of a proven corporate security solution, coupled with specialized solutions against targeted attacks that can prevent attacks by analyzing possible network anomalies.
- Executives responsible for digital business security should have access to the latest information and information on online threats, as they will be equipped with useful tools to prevent and detect targeted attacks, such as infringement indicators and YARA rules.
The products of Kaspersky Lab detect the malware used by the team behind 'Operation Ghoul' under the following codenames: 'Trojan.MSIL.ShopBot.ww', 'Trojan.Win32.Fsysna.dfah' and 'Trojan.Win32. Generic'.
More information on Operation Ghoul is available on the site Securelist.com. Those wishing to learn more about strategies to mitigate the impact of such attacks can visit the Kaspersky Lab's specialized business security blog.
The full report on Operation Ghoul is available to customers of the service Kaspersky APT Intelligence Reporting Service.





