At least 28 backdoors and many other vulnerabilities were discovered in the firmware of the popular FTTH ONT router, which is widely deployed throughout South America and Southeast Asia.
FTTH ONT stands for Fiber-to-the-Home Optical Network Terminal. These are special devices placed at the end of fiber optic cables. Their role is to convert optical signals sent through optical fibers into classic connections Ethernet or WiFi.
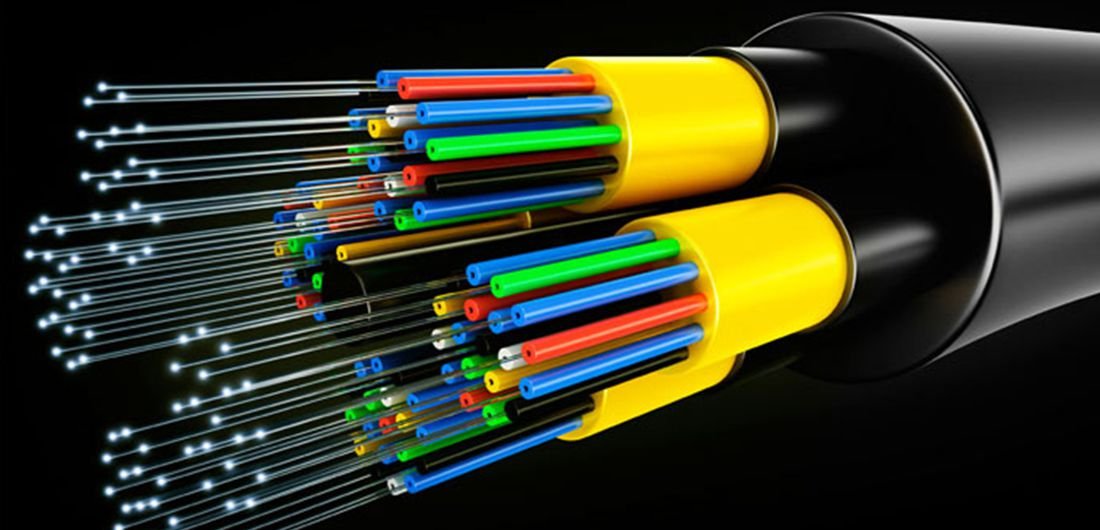
FTTH ONTs are usually installed in apartment buildings or inside homea or businesses that choose gigabit-type subscriptions.
In a report published last week, security researcher Pierre Kim reported that he found too many security holes with the FiberHome HG6245D and FiberHome RP2602, two models of FTTH ONT routers developed by the Chinese company Fiber Home Networks.
The report describes both the positive and the negative issues with both router models and their firmware.
For example, on the plus side, both devices do not expose the management panel through some external IPv4 interface, making it impossible to attack the web panel over the Internet. In addition, the ability to manage Telnet, which often usesfor abuse by botnets, it is disabled by default.
However, Kim says that FiberHome engineers apparently failed to activate, as the device firewall is only active on the IPv4 interface and not on IPv6, allowing direct access to all of the router's internal services, as long as one knows the IPv6 address. .
Kim described a long list of backdoors and vulnerabilities he discovered in the device, which he claims could be used by intruders to take over ISP infrastructure.
See the list of vulnerabilities





