Chinese company UNISOC, founded as Spreadtrum, is one of the largest chipmakers in the world and the largest in China for the past 20 years. The company produces low-cost chipsets for 2-5G compatible Android devices, smart TVs and other products.
Because the researchers had not tried their products before, her team CheckPoint decided to analyze part of the protocol messages used, known as NAS, and found a vulnerability (CVE-2022-20210) that can cause the device to stop radio communication through a malformed packet causing a DoS condition. This vulnerability allows attackers to intercept communications at a specific location.

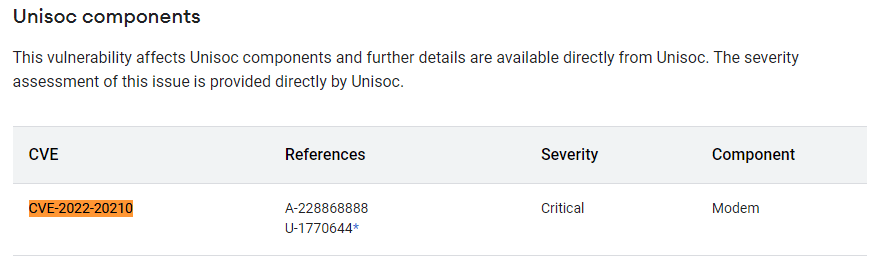
About the vulnerability (CVE-2022-20210)
The LTE network should be carefully examined to understand the basic concepts and how to exploit this vulnerability. The Long Term Evolution (LTE) network includes a number of protocols and components. The 3GPP team created the Evolving Packet System (EPS), an LTE technology that consists of three parts:
- The user equipment (UE)
- Evolved UMTS terrestrial radio access network (E-UTRAN)
- Evolved packet core (EPC)
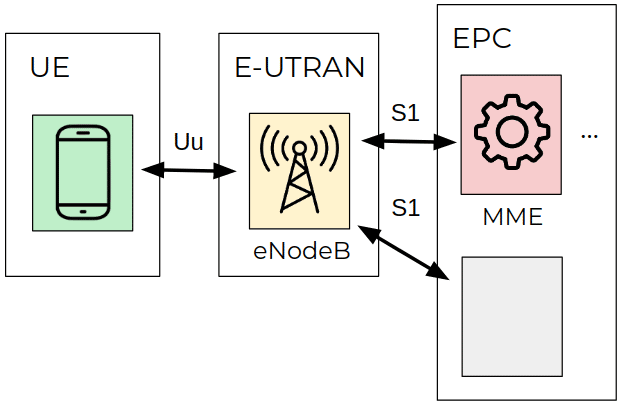
Figure 1: High-level diagram of LTE network EPS architecture
More specifically, the E-UTRAN component consists of a single stack called an “eNodeB” station. This station is responsible for controlling the radio communications between the UE and the EPC elements. Note that a UE can only communicate with a single eNodeB in a single communication.
The ECC is divided into four parts, one of which is the Mobility Management Entity (MME). This component is responsible for sending control-related signaling messages better safetys, the management of localization areas and the maintenance of mobility.
The research was performed using a UNISOC modem and communications between the MME component and the UE stack (Android device). Figure 2 shows the protocol stack of the modem—the non-access layer (NAS) layer hosts messages EPS and EMM signaling.
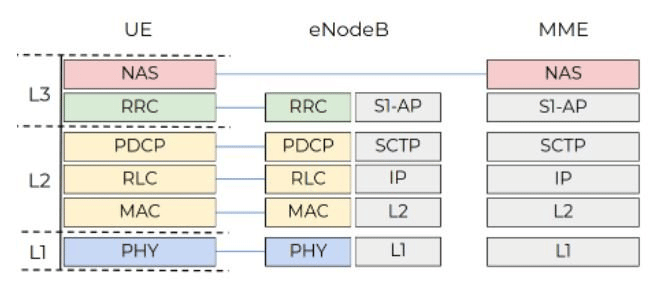
Figure 2: High-level diagram illustrating the LTE protocol stacks
Some messages between the UE and the MME are shown below.
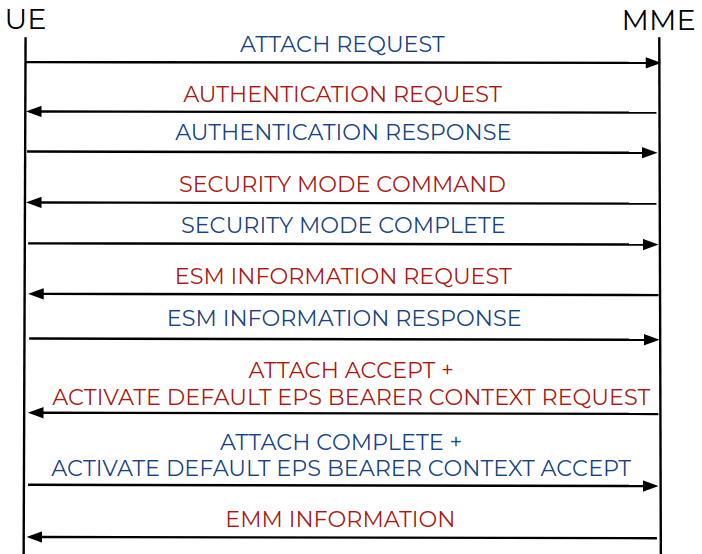
Figure 3: Messaging diagram
The NAS protocol should be highlighted (see Figure 3) because it operates on top of high-level structures. A hacker can craft specially crafted packets and send them to the target device to crash or remotely execute code.
Examining the details of the vulnerability
In this sense, the vulnerability identified as CVE-2022-20210 is based on the exploitation of NAS arguments, namely:
- Output filter
- NAS message bundle
- Shift offset
By fuzzing the implementation of the NAS function through the AFL and QUEMU approaches, the team identified some interesting functions such as srsRAN's liblte_mme_unpack_mobile_id_ie which is used to extract the mobile ID from the NAS message. This ID starts with a number and the value consists of a 2-byte length to represent the International Mobile Subscriber Identity (IMSI).
The crash occurs when this value is copied to the output buffer as an IMSI number. If the length of the value is zero, 0-2 = 0xFFFFFFFFFE bytes are moved to the heap memory and a DoS condition is caused.
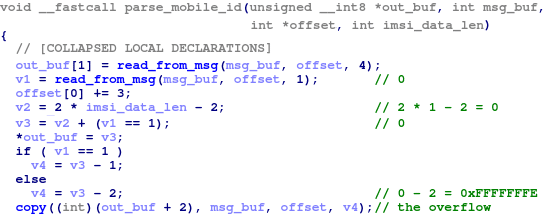
Figure 4: Block of code responsible for crashing the device
As a result, a malformed NAS message is generated. As noted below and described by CheckPoint, “the highlighted value 0x23 indicates that the following data is the message identity block, where the first 0x01 is the length and the second 0x01 is the IMSI type”.
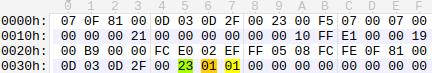
Figure 5: Malformed NAS message
This message causes the device to crash and opens doors to more sophisticated payloads that can lead to remote code execution scripts.
In conclusion
In this article, we observed how the LTE protocol and malformed NAS messages could affect the operation of smart devices, even leading to outage or neutralization of the devices.
Google has tackled all of them errorto protect millions of devices around the world. The fix came with the security update in June 2022 and users can now protect their smart devices from this vulnerability.