H Perfect Dark is a peer-to-peer (P2P) application from Japan, which was released in 2006. It supports Japanese and English languages for easy downloading and sharing of files and documents.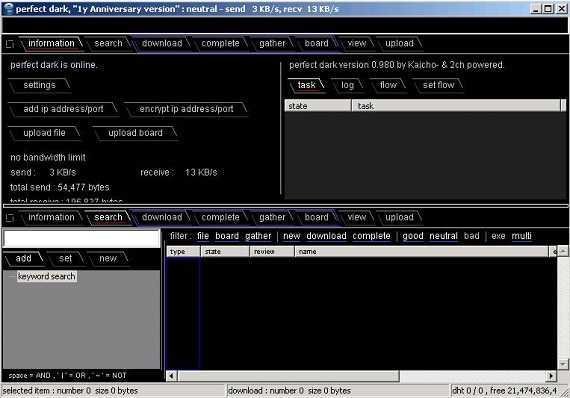
The Perfect Dark application came from its predecessors, Share (P2P) and Winny (P2P), which required less network bandwidth and hard disk space. The application has its own private network named “unity”, it has a powerful tool search engine for optimal file sharing and provides a bulletin board where users can discuss or exchange files. Additionally it offers Community Tech Support for advanced users and developers. Users can also share a size of uploaded files to further boost the download of other community users. Perfect Dark is still in development today.
| Other basics characteristics of the application Perfect Dark include the following: |
|---|
| Use of hash tables for maximum security on large P2P networks. |
| Protect users by changing the IP address, allowing users to share and download a large number of files without problems. |
| Key Table and Hash Tab distribution, which make up the entire application network and use a complex algorithm, ensure shots and shipment. |
| Users can use logical operators like AND, NOT and OR to help filter the files to be sent or received. |
DKT + DHT + DU
The creator applies an architecture called DKT + DHT + DU when designing the network. These three parts compose the entire network.
| DKT + DHT + DU |
|---|
| “DKT” Distributed Keyword Table. |
| “DHT” for Distributed Hash Table. |
| “DU” for distributed Unity. (Unity Distribution). |
"DKT" is primarily for efficient file search, while "DHT" and "DU" are used to effectively share files and enhance anonymity.
Network Bandwidth Requirements
The minimum shipping speed is 100 KB / sec. If the user does not configure the Perfect Dark application with the appropriate settings or if he is unable to support the necessary settings, download rates will be limited so that priority will be given to other users. This is intended to increase the Perfect Dark network retention rate.
Require disk space
It requires at least 40 GB hard disk space, where a huge Hash table is stored, which is used as storage and distribution of files.
File System Requirements
The application requires the NTFS file system instead of FAT32, because FAT32 is limited in file size to 4 GB, while the application supports downloading files up to 32 GB.
Specifications
Search files: Search treeυ
"Tree Search" offers a powerful search. In addition, the use of Boolean AND, OR and NOT operators helps to eliminate unwanted effects.
Stream text
The application includes a unique feature called "flow": It is a window where the text that one of the users wrote is scrolled vertically. Each user can write a small message (some rows and columns), and show it to other users using the feed feature.
Automatic update
From version 1.02 the application Perfect Dark has the ability to be updated automatically through its own network.
Message boards
Perfect Dark has a simple message board. These tables are distributed over the network. Their design is rudimentary. Japanese language must be used to search within the tables.
Safety
The overall structure of the Perfect Dark network is broadly similar to its recent versions freenet, only using a larger partition table. Anonymity is based on a mixnet where file traffic is transmitted according to specific probabilities, and is stored or transferred to encrypted blocks while the keys are distributed separately.
The application uses RSA (1024-bit) and AES (128-bit) to encrypt data transmitted between peers and the keys are temporarily stored for higher performance.
Published files and scoreboards (including automatic updates) are usually signed with 160-bit ECDSA signatures. Its Automatic Updates software they are also protected with 2048-bit RSA signatures.
Creators believe that because of the program's code, potential attacks on security and anonymity are likely, as "opportunists" and wasteful files that degrade the network. However, the authors have stated the idea of using open source in the future to solve the above problems.
2010, the Japanese security company NetAgent, claimed to have created software capable of decrypting encrypted information, such as the file name, the IP address of the original computer that uploaded the file, and other details.
filefacts.com/perfect-dark-info





