Clever new phishing method: Hackers targeting energy companies, including nuclear and other critical infrastructure providers, are using a technique attacks.
Το ηλεκτρονικό “ψάρεμα” ή phishing είναι από τις πιο δοκιμασμένες και πιο επιτυχημένες μεθόδους επίθεσης. Οι κυβερνοεγκληματίες δημιουργούν μια κανονική διεύθυνση ηλεκτρονικού ταχυδρομείου και αρχίζουν την Mission messages that contain a malicious attachment. 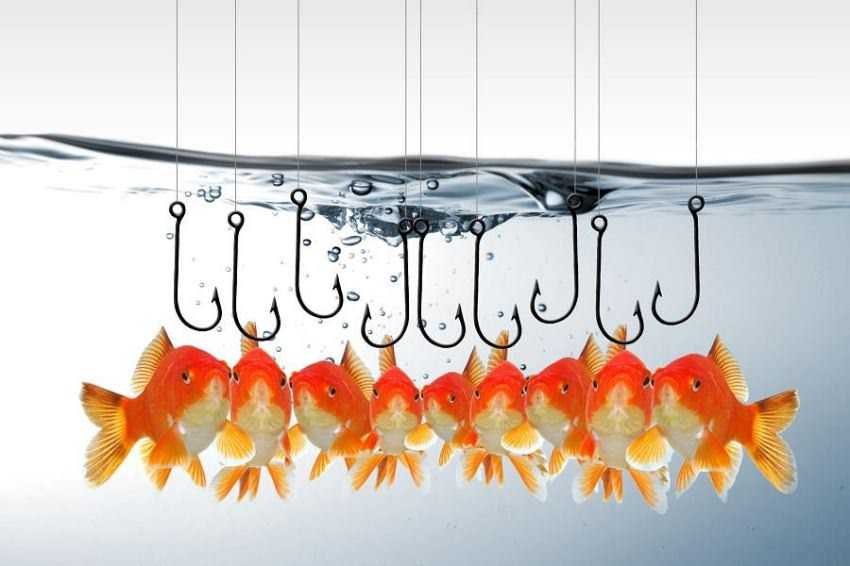
When the victim makes the mistake of opening or running the attachment, their computer will be full malware from some remote server. This is how most ransomware, data theft, or some other form of attack is carried out.
However, attackers are now able to carry out phishing attacks without having to attach to a malicious file. Instead, they allegedly download a template file injection via an SMB connection and obtain the victim's credentials without anyone understanding, her researchers said. Talos Intelligence.
The specific method of attack usesis currently only used to steal data, but researchers warn that it could also be used to deliver other malware.
The attack is the latest that has been discovered by a series of attacks exploiting malfunctions of the SMB, although in contrast to Petya or WannaCry, there is no relationship between him and him EternalBlue, the NSA that had been used for the global ransomware attacks we saw a while ago.
Attacks on critical infrastructure are not a new phenomenon, but since May of 2017 hackers have been using this new technique to target power companies around the world, mainly in Europe and the United States, to steal the credentials of those who work critical infrastructure.
At present it is not known who is behind these attacks or from where they start.
As with other phishing attacks, this attack uses target-related emails to entice them. They are often claimed to be messages that contain a CV in an attached Word document.
Researchers report that these documents did not initially contain malicious macros that we are accustomed to in this type of attack. However, the attachments seem to download a template file from a specific IP address. The researchers found instead of the code instructions for a template injection, which creates a connection to an external SMB server.





