Check Point Research, its research department Check Point Software Technologies Ltd.., published the Global Threat Index for March 2021.
The researchers report that trojan Trickbot has conquered the first place of the index, from the third where it was in January. Researchers report that banking trojan IcedID entered the Index for the first time, occupying the second place, while the established one trojan Dridex was the most common malware during March, up from seventh in February.

IcedID first appeared in 2017 and spread rapidly in March through various spam campaigns, affecting 11% of organizations worldwide. A widespread campaign used a COVID-19 theme to lure new victims into opening malicious email attachments. the majority of these attachments are Microsoft Word documents with a malicious macro used to insert a software installation for IcedID. Once installed, the trojan then attempts to steal account information, payment credentials, and other sensitive information from users' computers. IcedID also uses other malware to proliferate and has been used as the initial stage of infection in ransomware attacks.
"The IcedID "It has been around for a few years, but recently it has been widely used, showing that cybercriminals continue to adapt their techniques for attacking organisms, using the pandemic as a pretext." Maya Horowitz, CEO, Threat market & Research, Products at Check Point. “”IcedID is a particularly dangerous trojan that uses a range of techniques to steal financial data, so organizations must ensure they have strong security systems in place to prevent infringement of their networks and minimize risks. Comprehensive training of all employees is vital so that they are equipped with the skills needed to detect the types of malicious emails that spread IcedID and other malware.”
Η CPR also warns that theHTTP Headers Remote -- Execution (CVE-2020-13756) "is the most common vulnerability used, affecting 45% of organizations worldwide, follows the"MVPower DVR Remote -- Execution”Which affects 44% of organizations worldwide. While the "Dash GPON Router Authentication Bypass (CVE-2018-10561) ”is in the third place of the list with the most frequently exploited vulnerabilities, with an impact of 44% worldwide.
The 3 Most Common Malware Threats
* The arrows refer to the change of the ranking in relation to the previous month.
This month, the Dridex is the most popular malware with a global impact of 16% of organizations, follow the IcedID and Lokibot affecting 11% and 9% of organizations worldwide respectively.
-
↑ Dridex - The Dridex it is a Trojan targeting their platform Windows and reportedly downloads via an attachment spam in e-mail. The Dridex communicates with a remote server and sends information about the infected system. It can also download and execute arbitrary modules it receives from the remote server.
-
↑ IcedID - The IcedID is a banking Trojan spread through campaigns spam e-mail and uses avoidance techniques, such as process injection and sealing, to steal users' financial data.
-
↑ Lokibot - The Lokibot is a spyware that is distributed primarily through phishing emails and is used to steal various data, such as e-mail credentials, as well as passwords to cryptocurrency wallets and servers. FTP.
The most exploitable vulnerabilities
This month, the “ HTTP Headers Remote -- Execution (CVE-2020-13756) ” is the most commonly exploited vulnerability, affecting 45% of organizations worldwide, followed by "MVPower DVR Remote -- Execution"”Which affects 44% of organizations worldwide. THE " Dash GPON Router Authentication Bypass (CVE-2018-10561)Is in third place with an impact of 44% worldwide.
-
↑ HTTP Headers Remote -- Execution (CVE-2020-13756) Specific HTTP header fields allow the client and server to transfer additional information. A remote intruder can use a vulnerable HTTP field to execute arbitrary code on the victim machine.
-
↑ MVPower DVR Remote -- Execution - MVPower DVRs have a remote code execution vulnerability. A remote attacker can exploit this vulnerability and execute arbitrary code on the affected router via a crafted request.
-
↑ Dash GPON Router Authentication Bypass (CVE-2018-10561) – An audit bypass vulnerability ID cards that exists in Dasan GPON routers. Successful exploitation of this vulnerability allows remote attackers to obtain sensitive information and gain unauthorized access to the affected system.
The 3 Most Common Mobile Malware Threats
The Hiddad ranks 1st as the most prevalent mobile malware, followed by xHelper and FurBall.
-
Hiddad -The Hiddad it is a malware software Android which repackages legitimate applications and then releases them to a third-party store. Its main function is to display ads, but it can also gain access to key security details built into the operating system.
-
xHelper - The xHelper is a malicious application that has been in the forefront since March 2019 and is used to download other malicious applications and display ads. The application is able to "hide" from the user and be reinstalled automatically in case it is uninstalled.
-
FurBall - FurBall is an Android MRAT (Mobile Remote Access Trojan) developed by APT-C-50, an Iranian APT team affiliated with the Iranian government. This malware has been used in multiple campaigns dating back to 2017 and is still active today. Among the features of FurBall are: theft of SMS messages and mobile call logs, call logging and environment, multimedia file collection, location tracking and much more.
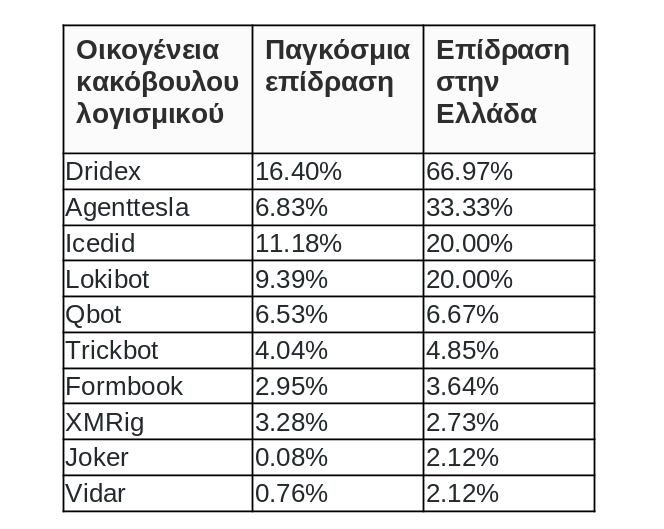
The full list of the most common malware threats in Greece for January is:
Dridex Dridex is a Banking Trojan that targets the Windows platform via spam and Exploit Kits, which relies on WebInjects to monitor and redirect bank credentials to an intruder-controlled server. Dridex communicates with a remote server, sends information about the infected system, and can also download and run additional operating systems for remote control.
Agentesla - AgentTesla is an advanced RAT (Remote Access Trojan) that extracts passwords and data when typing. Active since 2014, AgentTesla can monitor and collect data from the victim as he or she types, it can also capture screenshots and authentication credentials that have been inserted for many software programs installed on your machine (including Google Chrome, Mozilla Firefox and Microsoft Outlook). AgentTesla sells openly as a legal RAT with customers paying $ 15 - $ 69 for licenses.
IcedID- That's it IcedID is a banking Trojan that first appeared in September 2017. It typically uses other known banking Trojans, including Emotet, Ursnif and Trickbot, to help spread the word. IcedID steals users' financial data both through redirect attacks (installs a local proxy server to redirect users to fake clone sites) and through web injection attacks (introduces a browser process to display fake overlapping content Home).
LokiBot- That's it LokiBot was first detected in February 2016 and is an information spy with versions for both Windows and Android. It collects credentials from various applications, web browsers, e-mail programs, IT management tools such as PuTTY and more. LokiBot is sold in hacking forums and it is believed that its source code was leaked, thus allowing the appearance of numerous variations. As of late 2017, some versions of LokiBot for Android include ransomware functionality in addition to information theft capabilities.
Qbot AKA Qakbot is a banking Trojan that first appeared in 2008, with the aim of stealing bank credentials and data entered by users. It is often distributed via spam email. Qbot uses many anti-VM, anti-debugging and anti-sandbox techniques to block analysis and avoid detection.
Trickbot - Trickbot is a dominant banking trojan that targets Windows platforms and is mainly transmitted via spam or other malware families such as Emotet. Trickbot sends information about the infected system and can also download and execute modules arbitrarily from a wide range of available, such as a VNC module for remote use or an SMB module for distribution within an affected network. Once a machine is infected, the threat agents behind the Trickbot malware use this wide range of modules not only to steal bank credentials from the target computer, but also for lateral movement and recognition within the organization itself, before a targeted attack. ransomware throughout the company.
FormBook - FormBook is an InfoStealer that targets the Windows operating system and was first detected in 2016. It is advertised in hacking forums as a tool that has powerful avoidance techniques and relatively low prices. FormBook collects credentials from various web browsers and screenshots, monitors and records keyboards, and can download and execute files according to C & C instructions given to it.
XMRig - XMRig is an open source CPU mining software used for the Monero cryptocurrency production process and was first released in May 2017.
Joker- The Joker An android Spyware on Google Play, designed to steal SMS messages, contact lists and device information. In addition, the malware secretly subscribes to the victim for premium services on advertising sites.
Vidar– Vidar is an infolstealer that targets Windows operating systems. First detected in late 2018, it is designed to steal passwords, credit card data and other sensitive information from various web browsers and digital wallets. Vidar has been sold on various online forums and a malware dropper has been used to download GandCrab ransomware as its secondary load.
The World Threat Impact List and the Map ThreatCloud of Check Point, based on ThreatCloud intelligence of Check Point, on the largest network cooperation to combat it cybercrime, which provides data on threats and trends in attacks, utilizing a global network of threat detectors. The database ThreatCloud includes over 3 billion websites and 600 million files daily and tracks more than 250 million activities malware every day.
The full list of the most common malware threats worldwide for February is available at Check Point Blog





