The native Windows RDP program helps you remotely manage your computer from anywhere in the world. But it is much safer to immediately change to the default communication port to avoid compromising your systems.
Remotely connecting to your Windows computer is possible thanks to Microsoft's free proprietary network communication protocol known as Remote Desktop Protocol (or Remote Desktop Protocol – RDP).
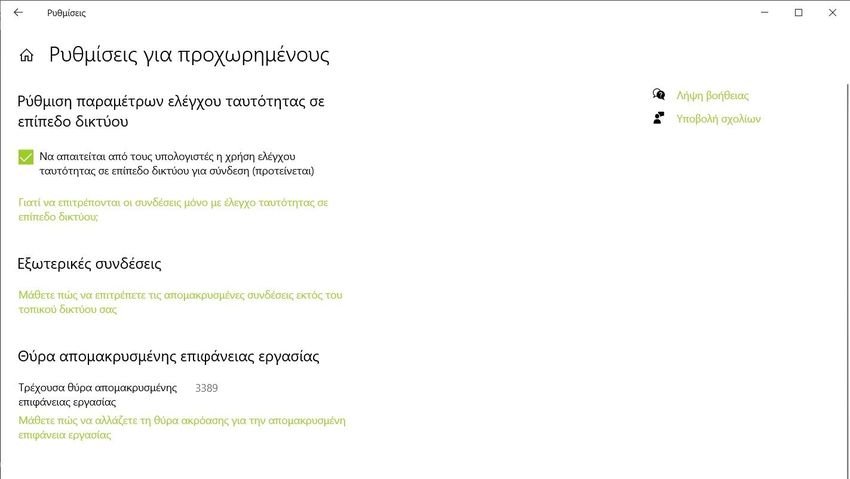
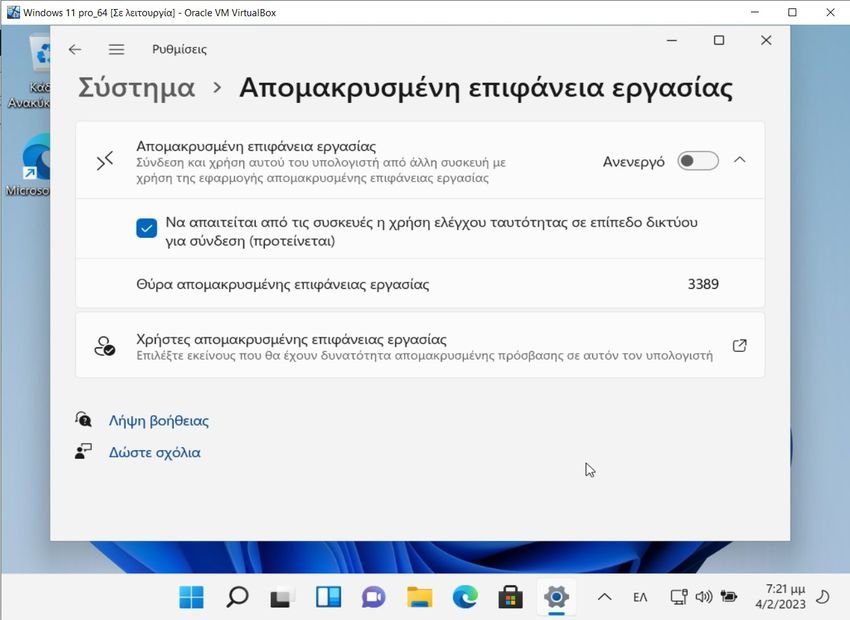
3389 is the default port assigned for RDP on your computer. But if you want to be as much as possible safeyou have to change it. And after changing it you will need to configure the Windows firewall rules to adapt to the new RDP port.
Why you need to change the RDP port
TCP 3389, as the default RDP port for all remote connections, is on the hackers' radar. They use brute force attacks and other methods to guess login credentials to access TCP 3389.
Once in, they can steal or encrypt sensitive data, install malware, and do whatever they want on the remote computer.
When you change the default RDP port number from 3389 to any other port, it becomes difficult for hackers to guess which RDP port you are using. But even if they scan you and see that you have an "irrelevant" port open, say 51255, it's hard for them to guess why you have it open. And changing the RDP port is especially useful when you've disabled network-level authentication (NLA).
How to see which port you are using
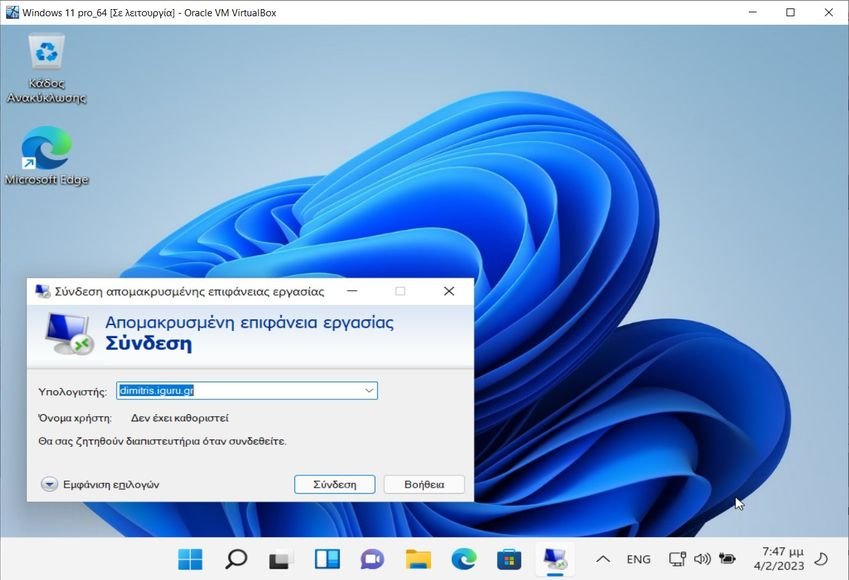
In Windows 10 go to Settings > System > Remote Desktop.
There enable remote desktop (if it is not enabled) and press “Advanced settings”. See the “Current Remote Desktop Port” field at the bottom of the window.
In Windows 11, follow the same path, except that on the activation button press the down arrow.
How to change RDP port
You can change your computer's default RDP TCP port to a new one by making a few modifications in the Registry Editor. The process is simple.
However, we strongly recommend that you back up your Windows registry so that you can quickly restore it if something goes wrong. Here's how to do it.
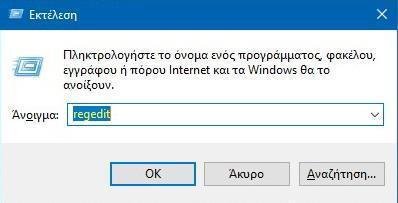
Press the Win + R keys simultaneously to open the Run window and type “regedit” in the search box. Click OK to open the Registry Editor.
For this example, we chose port 51255 to make it the port for Remote Desktop Service.
In the Windows Registry Editor window paste the following command in the search bar and press Enter.
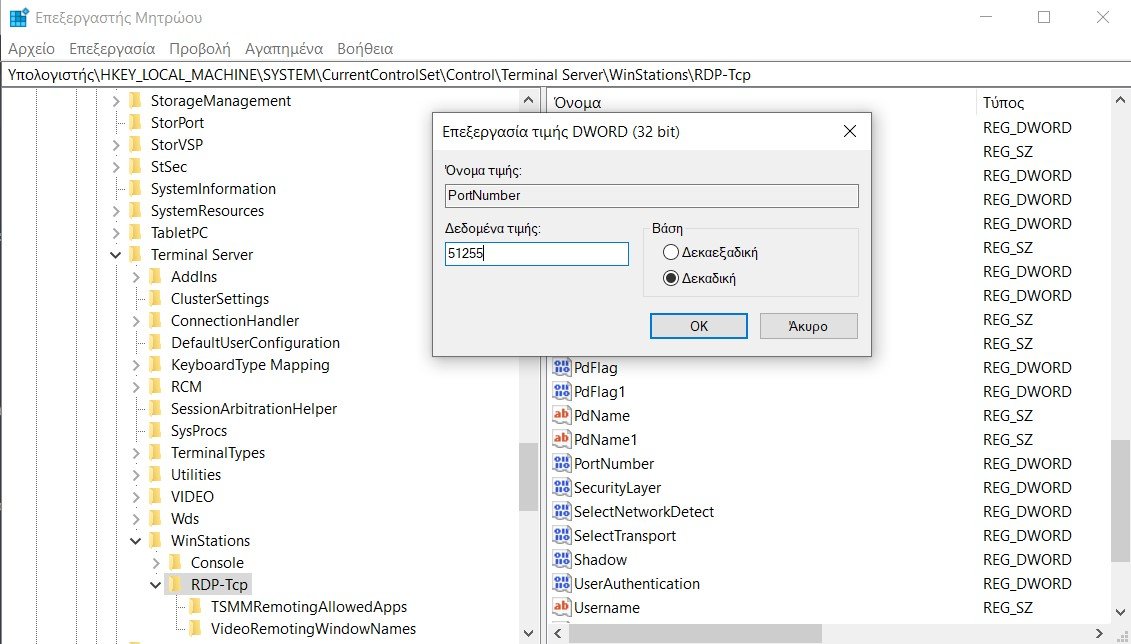
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Terminal Server\WinStations\RDP-TcpScroll down on the right sidebar until you reach the PortNumber. Double click on it to edit. Select the Decimal option in the edit window and enter the desired port number (51255) in the Value data field. Click OK to continue.
Close the Windows Registry Editor and restart your computer. You have now successfully changed your computer's default RDP port to 51255.
Alternatively you can also change the default RDP port with the help of Windows PowerShell command.
Run a Windows PowerShell window with administrator privileges and paste the following command. Then press Enter.
Set-ItemProperty -Path "HKLM:\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\" -Name PortNumber -Value 51255
The default RDP port on your Windows computer has been changed to a non-standard RDP port: 51255 (of course you can put any port you want). Your computer will now use port 51255 for remote desktop connection.
How to choose the right number for a custom RDP port

There are 65.535 port numbers. Common TCP/IP applications use port numbers from 0 to 1023, which are called well-known ports. For example, port number 443 is used for certificate-based authentication (HTTPS).
Therefore, it is recommended not to change the RDP port in Windows to any number from 0 to 1023.
Ports 49152 to 65535 are known as dynamic ports and are typically used by clients to establish a connection to a server. As a result, many people prefer to choose a port number between 49152 and 65535 to avoid conflict with well-known or custom services.
Configure Windows Firewall for a custom RDP port

Now that you have changed the default RDP port number on your computer, you need to create rules in Windows Firewall for the custom RDP port number.
If you don't do this, your Windows firewall might prevent you from using Remote Desktop Services using the custom RDP port.
Open a PowerShell window with administrative privileges (or Windows Terminal on Windows 11) and type the following. Then press Enter.
New-NetFirewallRule -DisplayName 'RDPPORT_TCP' -Profile 'Public' -Direction Inbound -Action Allow -Protocol TCP -LocalPort 51289Of course change the port according to your preference.
Now, paste the following command and press Enter.
New-NetFirewallRule -DisplayName 'RDPPORT_UDP' -Profile 'Public' -Direction Inbound -Action Allow -Protocol UDP -LocalPort 51289again make sure the port number is correct.
Restart your computer and enable Remote Desktop on your computer. You will now be able to use the custom RDP port.
How to improve RDP security
Hackers are constantly trying to exploit RDP vulnerabilities. Changing the default RDP port is just one way to strengthen the security of the RDP service.
Here are some tips RDP security to avoid attack:
-
Any account that accesses Remote Desktop must use strong passwords access and multi-factor authentication.
-
Microsoft offers patches for known vulnerabilities, so you should make sure your operating system is always up to date.
-
Use one RDP gateway to add a layer of security to remote desktop sessions.
-
Keep Network Layer Authentication (NLA) enabled.
-
Limit the users who can connect using Remote Desktop.
You should also provide remote users with the least level of access to data and resources (also known as the principle of least privilege). As a result, you can limit the damage that cybercriminals can do if they gain unauthorized access to a corporate network.
Change the RDP port to stay protected
As more and more companies adopt the remote work model, the number of remote connections has grown exponentially. Consequently, hackers target the default port of each remote desktop to access corporate networks. Whether that's RDP it's TeamViewer or the Anydesk.
Changing the RDP port is a great strategy to keep your RDP port hidden from hackers, as hackers use scripts that usually target the default remote desktop port.





