Today we will introduce you to the Princess Locker ransomware so you can see how these infections behave to the end user, and be prepared if you become a victim of it.
For the story, the Princess Locker ransomware was discovered by Michael Gillespie. Encrypts victim data and then requires a huge amount of ransom from 3 bitcoins (about $ 1.800 dollars) to deliver to the victim a decryptor. If the payment is not made in the specified time, then the ransom payment is doubled to 6 bitcoins.
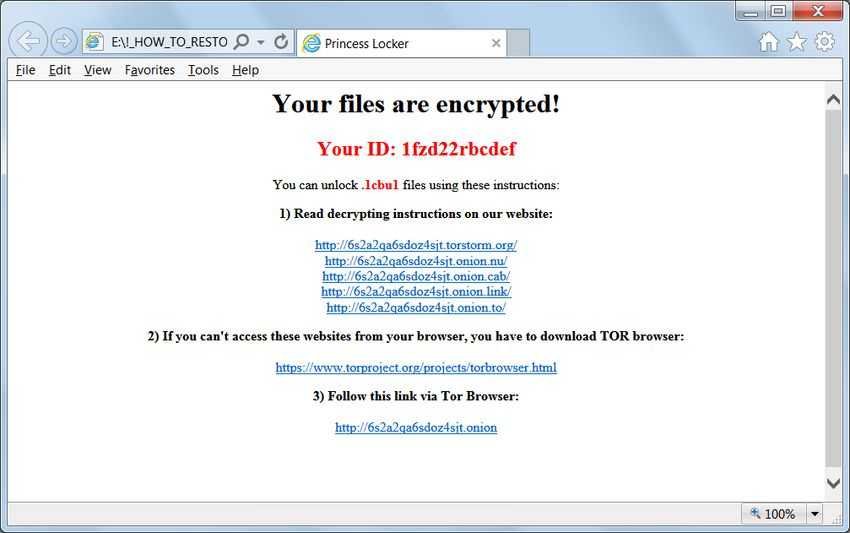
We don't know much about the structure of Princess Locker, except for some encrypted files and the messages for ransoms that have gone up to ID-Ransomware. From the data so far, when a person is infected, the ransomware will encrypt the victim's files, then append a random extension to the encrypted files and finally generate a unique identifier, different for each victim. The identifier, extension, and encryption likely sent to the ransomware server.
Ransomware messages contain the victim's ID and links to TOR payment areas where the victim should be logged in to see the payment information.
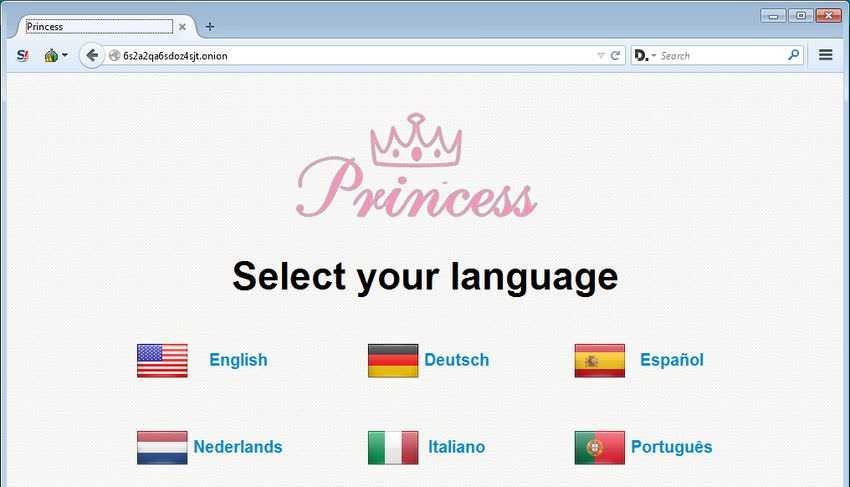
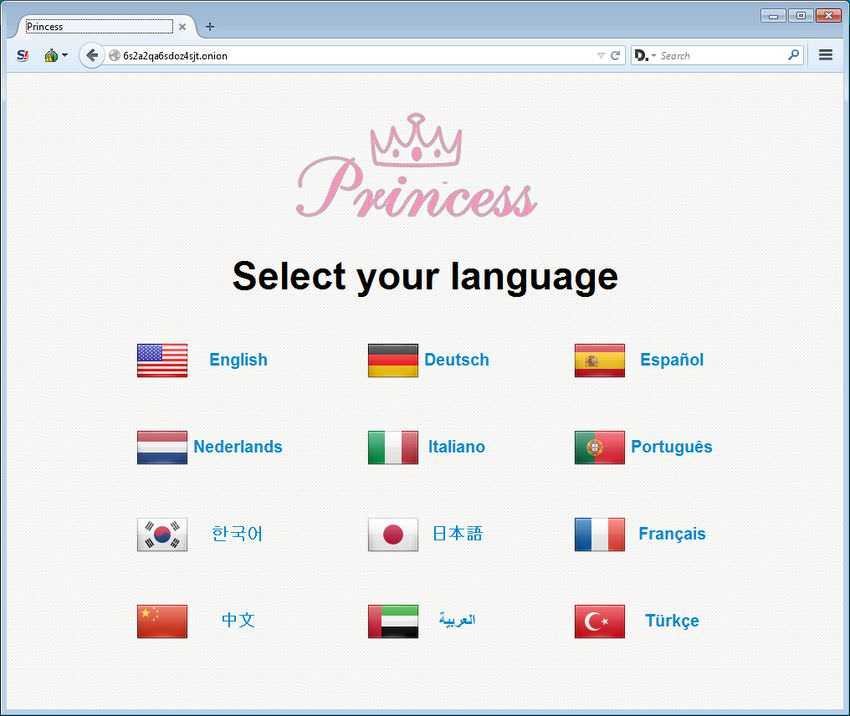
Princess Locker's payment website is a standard ransomware website, nothing special characteristics. When the victim enters this website, they will see the logo and the option to choose one of the 12 available languages.
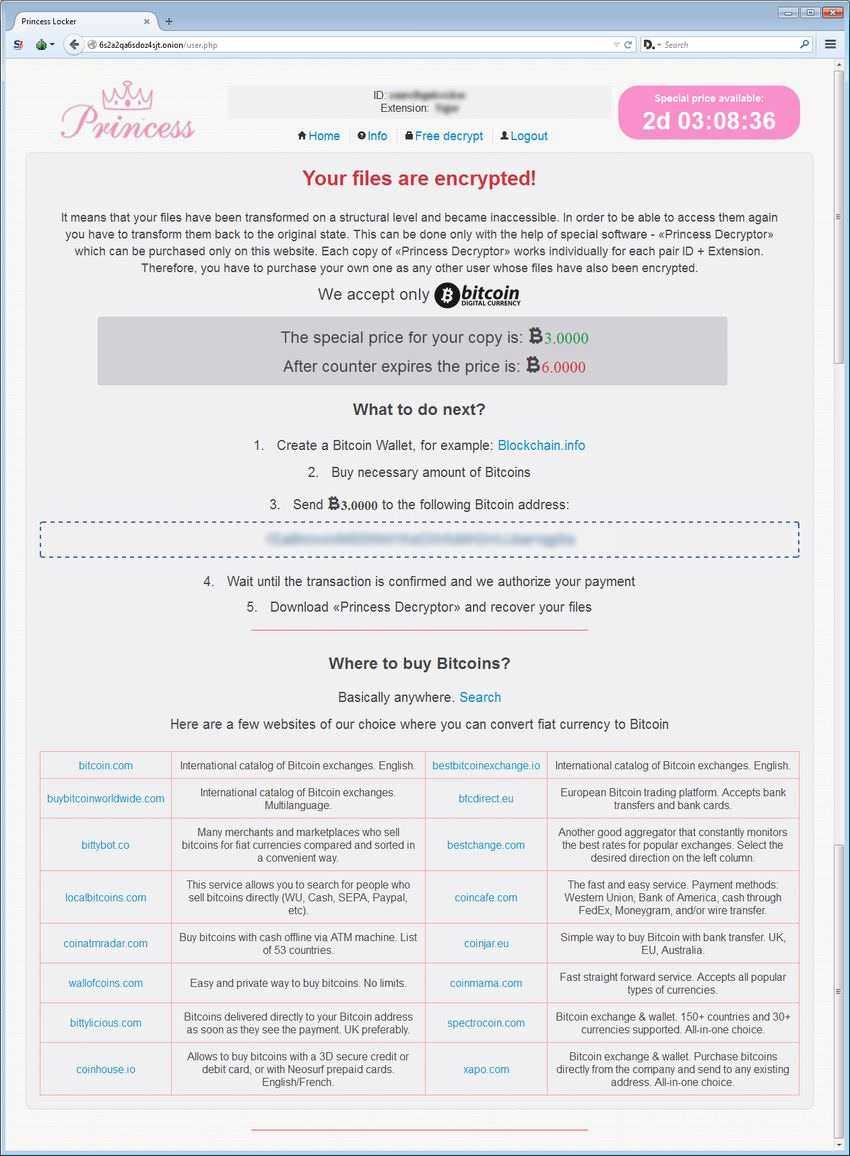
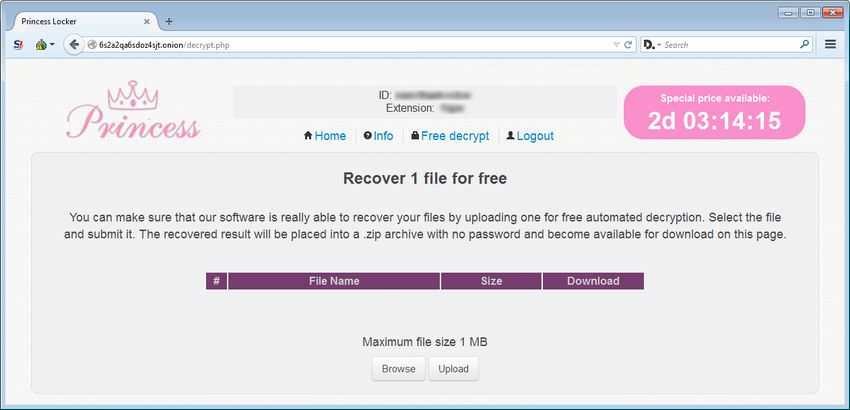
After selecting the language a login prompt will appear where he must enter the ID that was communicated to him in the ransom note. Once logged in, he will see the main payment page, which contains information such as the ransom amount, the bitcoin address to send the payment to, and ready answers to frequently asked questions.
The payment site also provides the ability to decipher 1 file for free. Unfortunately, since we do not have a sample of ransomware, and we do not have a computer that we could deliberately pollute, we do not know whether this feature works or not.
The whole construction looks quite professional. The only thing that might be missing from the payment page is a support page where victims can contact the developers of the malware software!!!. But if the ransomware in question infects enough people, we shouldn't be surprised to see this feature as well.