Some Intel and AMD microprocessors are vulnerable to a newly discovered speculative execution attack. With the attack, hidden code data can be leaked access and other sensitive information.
So are the two κατασκευαστές θα πρέπει να προσπαθήσουν για άλλη μια φορά να περιορίσουν μια πεισματικά επίμονη vulnerability.
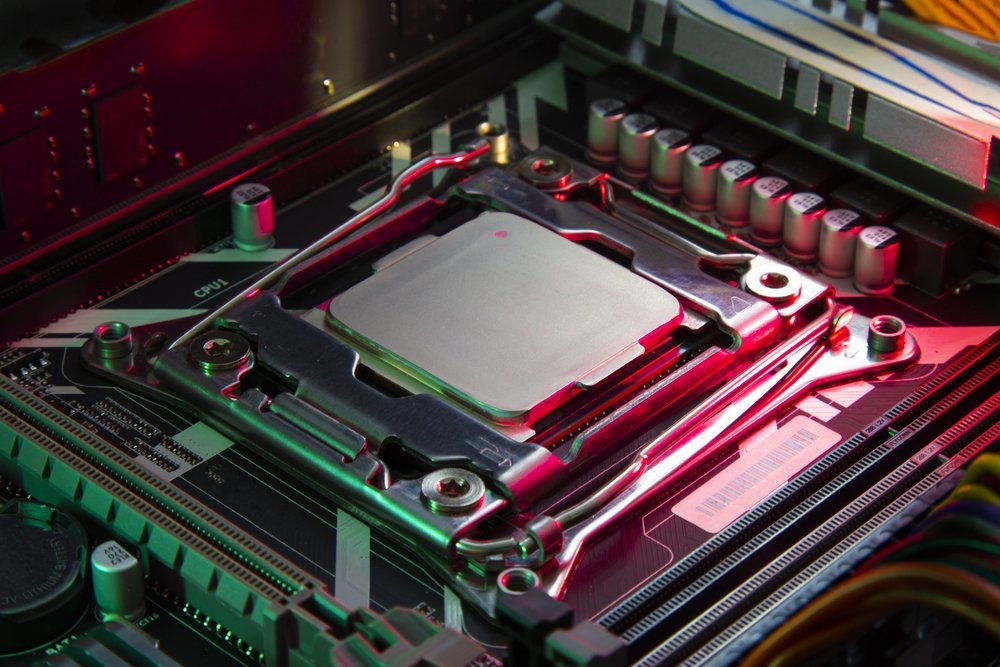
The researchers from ETH Zurich named their attack Retbleed (CVE-2022-29900 and CVE-2022-29901) because it exploits a software defense also known as retpoline, The specific mode added in 2018 to mitigate the harmful effects of speculative execution attacks. The specific attacks, also known as Spectre, take advantage of that: when modern CPUs encounter a direct or indirect instruction, they predict the address for the next instruction they are about to receive and automatically execute it before the prediction is confirmed.
See the attack
Specter vulnerabilities work by tricking the CPU into running an instruction that accesses sensitive data in memory. Retbleed then extracts the data. ETH Zurich researchers proved that Retbleed proof-of-concept that they created works on Intel processors with Kaby Lake and Coffee Lake microarchitectures and AMD Zen 1, Zen 1+ and Zen 2 microarchitectures.
In response to the investigation, both Intel and AMD advised their customers to adopt new updates, but the researchers reported that they would add up to 28 percent more overhead to their operations.
Read more about the attack
https://comsec.ethz.ch/research/microarch/retbleed/





