RSA 1024-bit – it is safe; Ερευνητές ασφαλείας ανακάλυψαν μια κρίσιμη ευπάθεια στο GnuPG cryptographic library που τους επέτρεψε να σπάσουν κρυπτογράφηση RSA 1024 bit και να εξαγάγουν το μυστικό κλειδί RSA για να αποκρυπτογραφήσουν δεδομένα.
The Gnu Privacy Guard (GnuPG or GPG) is a popular open source encryption software used by many operating systems (Linux, FreeBSD, Windows and macOS X).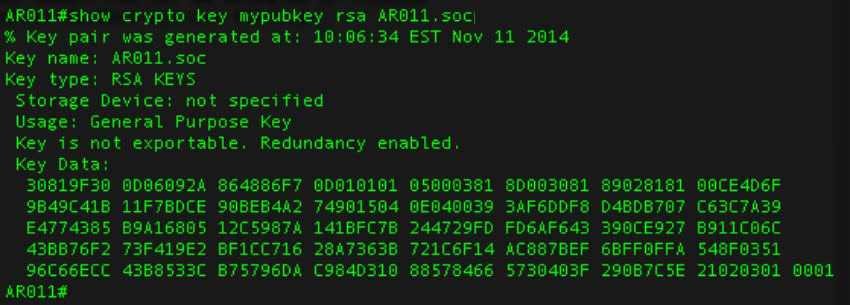
Vulnerability, under the name CVE-2017-7526, is located in the Libgcrypt encryption library used by GnuPG.
It's the same software that the former NSA employee used Edward Snowden to encrypt his communications.
Η research
A group of researchers from the Universities of Eindhoven, Illinois, Pennsylvania, Maryland, and Adelaide found that the "left-to-right sliding" method window” used by the libgcrypt library to perform the cryptography math leaks significantly more information than is needed, allowing the full recovery of the RSA key.
"In this work, we demonstrate a complete breakdown of RSA-1024 as applied to Libgcrypt. Our attack basically uses the fact that Libgcrypt uses the left-to-right method to calculate the sliding-window extension", Say the researchers in their paper.
The L3 Cache Side- AttackChannel requires an attacker to run a "compromised" software on the hardware used by the RSA private key.
For more information read 'Sliding right into disaster: Left-to-right sliding windows leak,' (PDF) by Daniel J. Bernstein, Joachim Breitner, Daniel Genkin, Leon Groot Bruinderink, Nadia Heninger, Christine van Vredendaal, Tanja Lange, and Yuval Yarom.





