SARENKA is an Open Source tool market ( OSINT ) that helps you acquire and understand the Attack Surface.

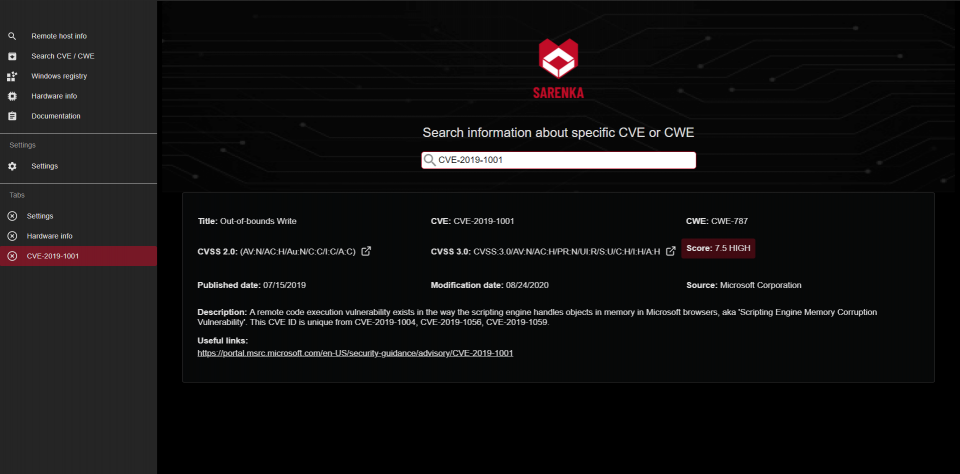
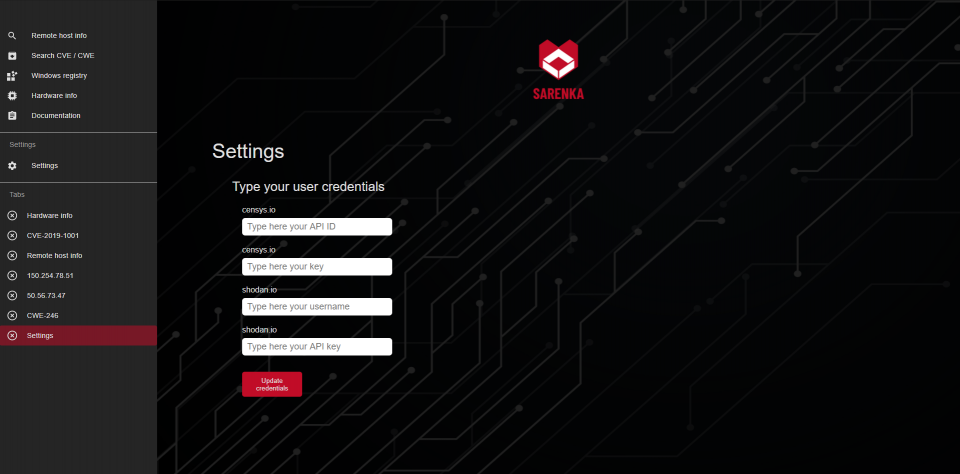
The main goal is collection information from machines searchs for devices connected to the Internet ( https://censys.io/ , https://www.shodan.io/). Displays data on Common Vulnerabilities and Exposures (CVE), Common Weakness (CWE) and also has a database where CVEs are assigned to CWE.
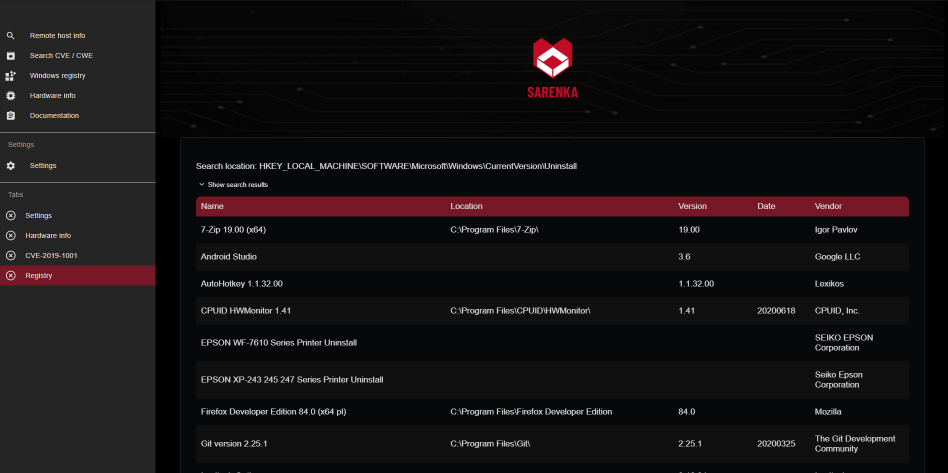
Returns data about the local machine – locally installed software (from register of Windows), local network information (python libraries, popular cmd commands).
Currently the app also has simple tools like numbermachine hash, shannon entropy calculator and very simple port scanner. More cryptography-math tools and identification scripts will be added.
Specifications
- receives data from https://censys.io/ via ip
- data from https://www.shodan.io/ via ip
- download data DNS
- download data WHOIS
- banner grabbing
- find CVEs from C.W.E.
- pdf for reports
You can also:
- calculate hashes string base
- calculate the shannon entropy based on the user string
Installation
SARENKA requires:
Download from repository
$ git clone https://github.com/pawlaczyk/sarenka.git
Go to the source list
$ cd sarenka / sarenka
We run sarenka.py
$ python sarenka.py
Getting started
#### Create accounts for the following services:
Running a backend application - default http://localhost:8000 /
# go to sarenka / sarenka $ python backend / manage.py runserver
Run frontent application - default http://localhost:3000/
# go to sarenka / sarenka / frontend folder $ npm start
Application snapshots
You can download the program from here.





