In a previous article we wrote about the use of Shodan, the most dangerous search engine in the world, for vulnerable web-cams.
As you know, Shodan just scans the IP addresses around the world and then shows us the banners. We can then query through Shodan the parameters revealed in these banners to find IP addresses of a specific type of device.

In this guide, we will look for SCADA devices. SCADA or Supervisory Control and Data Acquisition are systems used for things like systems transportpower plants, nuclear plants, chemical plants, water treatment plants, HVAC systems, home heating, etc. All of these systems have digital controls, all of which are vulnerable to attack.
SCADA systems are a huge concern for national defense agencies, as a nation that has had its SCADA systems hacked will be left behind in the event of war. This is why organizations like US Homeland Security are so concerned about SCADA security. Most cyber warfare experts expect that all future wars will have a SCADA cyber attack component.
SCADA Communication Protocols
There are multiple communication protocols used in SCADA or industrial control systems (ICS). Unlike Ethernet or Internet Protocol (IP), the industrial control industry uses multiple protocols, often unique to the manufacturer of the programmable logic controller (PLC). Although there are many protocols, some of the most popular communication protocols in these systems are as follows
modbus port 502
dnp port 19999
dnp3 port 20000
fieldbus port 1089-91
ethernet/IP port 2222
etherCAT port 34980
profilenet port 34962-64
Knowing the ports these systems are running on can help us identify vulnerable SCADA systems.
Modbus
Although we'll look at other protocols in future guides, here we'll focus on finding modbus-enabled SCADA systems that have Internet access. Modbus is one of the most common protocols in ICS and SCADA systems. Since we know that modbus uses port 502, it shouldn't be hard to find.
Modbus is a serial communication protocol originally published by Modicon (now Schneider Electric) in 1979 for use with its programmable logic controllers (PLCs). Modbus has become a de facto standard communication protocol in SCADA/ICS systems. Modbus has become the standard because:
-
developed with industrial applications in mind
-
open source and royalty free
-
easy to deploy and maintain
-
moves raw bits or words without placing many restrictions on vendors
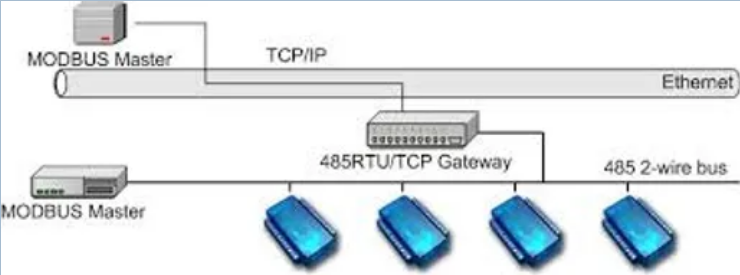
Modbus allows communication between several devices connected to the same network, for example a system that measures the temperaturewineα and humidity and transmits the results to a computer.
Modbus is often used to connect a supervisory computer to a remote terminal unit (RTU) in supervisory control and data acquisition (SCADA) systems. Many of the data types are named after their use in driving relays: a physical one-bit output is called a coil, and a physical one-bit input is called a discrete input or contact.
Without going into additional technical details of the modbus protocol, suffice it to say that many SCADA systems still use this popular protocol.
Shodan
Shodan enables us to search for banners and the information or parameters that reveal it. Since we know that modbus works over port 502, we could simply search Shodan for any IP that has that port open on the Internet. If they do, they are likely running modbus and part of some company's SCADA infrastructure.
Let's open Shodan and search for IPs with port 502 open. In Shodan's search window:
port: 502
Note that in Shodan, we first type the parameter we are looking for (port), followed by the colon (:) and finally the value (502). When we do this, we find over 13.000 results! While there is no guarantee that all of these IPs are running modbus, it is likely that most of them are, as port 502 is not a popular port.
We can see the first page of results from our Shodan search below.
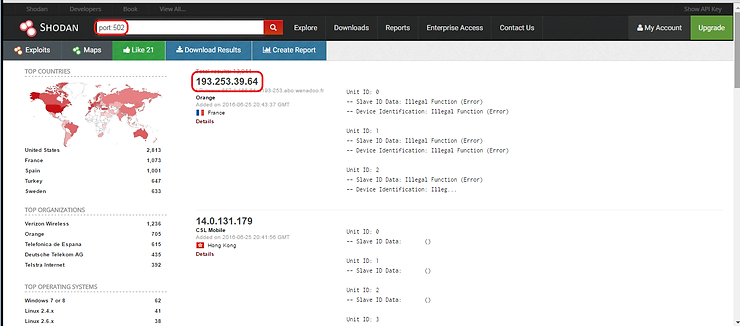
Note that the first result has an IP address of 192.253.39.64. Under the IP we see that it is based in France and is connected through the Orange (formerly France Telecom) telecommunications system. When we do click to IP, it takes us directly to the management interface of this device that uses modbus.
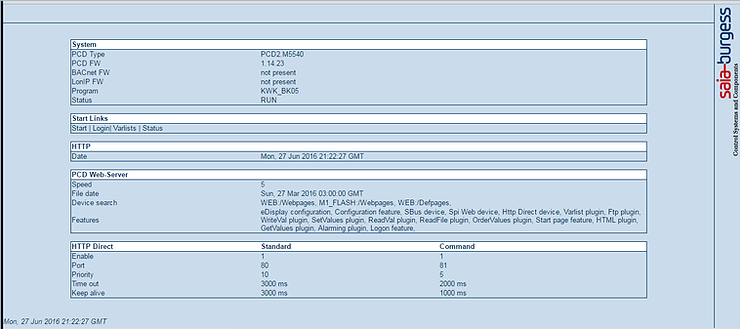
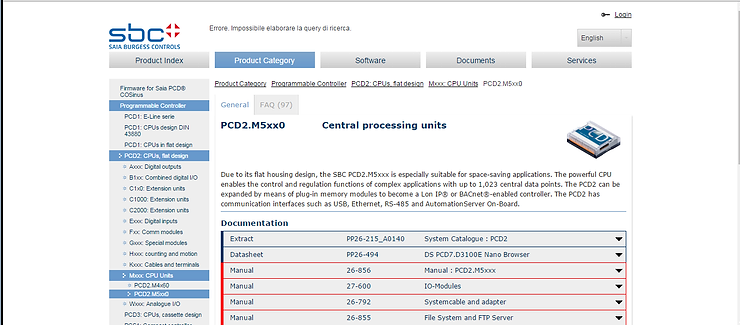
With a little internet research, we can find that this PLC is manufactured by SAIA-Burgess, a company based in Switzerland. They mainly manufacture programmable heating and cooling PLCs.
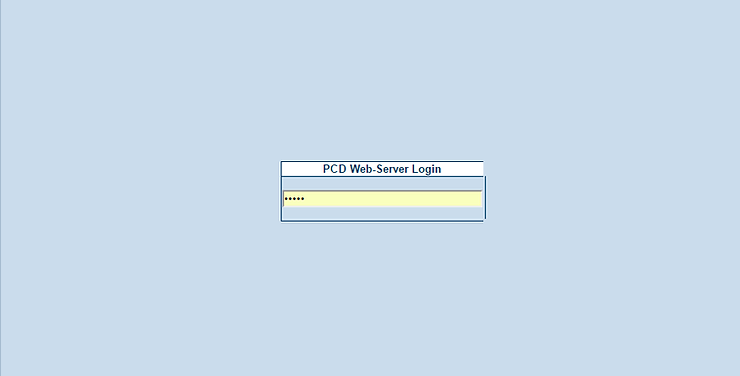
When we click on login, we come to PCD Web-Server Login. If we can connect here, we will be able to access the controls of this PLC and control the temperature and energy efficiency of this facility. While the consequences of such a breach may seem trivial, Elliot Alderson (the main character of the TV series Mr. Robot) and f/society would love this access when trying to render E Corp's backup tapes at the facility useless of Steel Mountain.
After several login attempts, I kept getting this login page indicating that there is no lock on this page, making it vulnerable to brute force attempts on its password.
Additionally, since we know this device uses port 502 for modbus communication, it is likely to be vulnerable to modbus attacks spoofing and/or DoS on this port.
This is a good example of how SCADA systems can be recognized by Shodan. Often their defenses are weak and limited and simple attacks such as brute force password cracking and DoS attacks are easily performed against them. Although this system was simple and relatively trivial, I have identified through Shodan the GUI management interface of nuclear and hydroelectric plants. Security engineers had better be informed before they fall victim to the next cyber attack.
You should be able to find other SCADA devices by searching ports 19999, 20000, 1089-1091, 2222, 34980, and 34962-34964.
Find SCADA systems by PLC name
Sometimes, you can find SCADA systems with base the manufacturer or PLC name and version number. Remember, with Shodan we search the web banner content of the systems. In most cases, these systems also display a banner detailing the manufacturer's name, PLC and version. Let's see an example.
Schneider Electric of Paris is now the parent of the company that first developed the modbus protocol, Modicon. They produce a wide variety of ICS systems most of which use the modbus protocol.
Let's start looking for these systems by simply entering the company name “Schneider Electric” into Shodan's search engine in double quotes. This should find all systems that have this name in their banner.
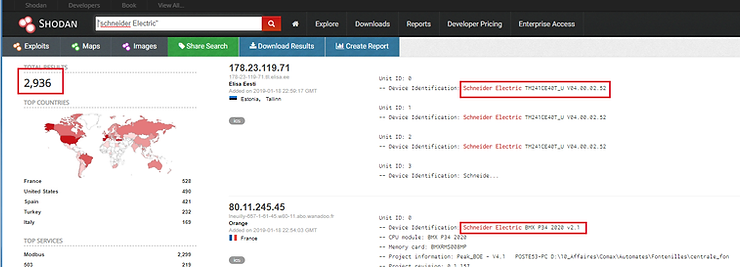
As you can see, Shodan has identified nearly 3000 systems worldwide with the name “Schneider Electric” on their logo. This strongly suggests that the system belongs to the family of Schneider Electric products.
We may want to be even more specific. Schneider Electric makes an automated building system it calls SAS, or Schneider Automated Server. It is used to automate the heating, cooling and security of high-tech buildings. If we include this additional term in Shodan's search, we will get a subset of our original search
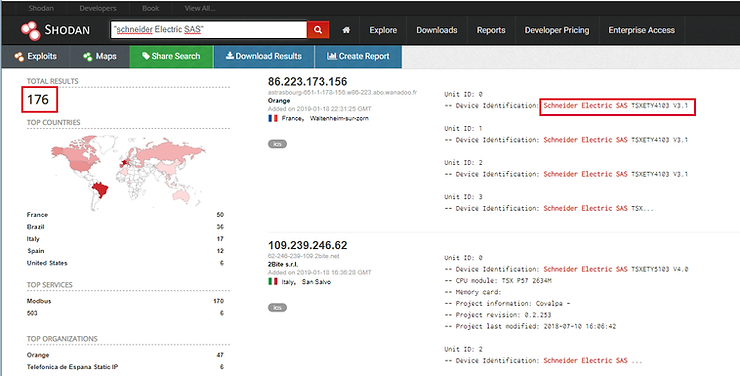
As you can see above, our search was limited to just 176 IP addresses on the planet.






Can I have a pdf of this article?