No bad pure good
Security Tips: With the modern way of life and the dimensions that the evolution of technology and the exploitation of the use of the internet have taken, with more and more users using it worldwide on a daily basis, either for simple communication or for financial transactions, it has brought to the surface various digital threats, whose behavior we will analyze and see how we can deal with them, when and if our system is infected, completely inexpensively.
How can malicious code be contacted
Certainly all internet users, we have occasionally heard expressions like, "stuck virus / virus", or "my computer is crawling while it is new" and many more that refer to malware infection as malware.
This infection usually comes from the internet, e-mails and infected websites, and there are some exceptions that can come from infected media, such as optical discs (CDs, DVDs, etc.), or removable drives that have been previously infected. (USB and external hard drives). An example of an optical disk infection was the rootkit (which we will explain below) that Sony installed through its CDs on users' computers in 2005-2007 to protect its copyright from copying.
What is generally termed a digital threat
A digital threat is essentially a piece of executable malware. Executable because it runs on any operating system for which it is programmed, be it Windows, Linux and Mac. And malicious because, it is programmed against the rules, the specific program is set, either to extract data and send it to its creator (passwords, card numbers and much more), or to irreparably harm the user. An example is CryptoLocker (we will analyze what it is next).
Various types of digital threats (Malware)
As we said above, we are increasingly hearing from people around us style phrases, "stuck virus" and "my computer is slow". Of course the expression sticky virus is so general, as to tell a doctor, I got sick. The next logical question is, "what do you feel?" So depending on the behavior of each digital threat, there is a specific name as well as how to deal with it. So let's set them apart!
- Virus. Virus is characterized as a malicious program that has the ability to copy itself. Once executed, usually without the user's knowledge, he copies himself modifying its copies, depending on the files that are spreading. Viruses on computers are treated using anti-virus programs, known to all Antivirus.
- Ransomware. The known to all of us, a police virus. It is Malware, which slows down the system significantly and asks the ransom from the user to release his system. Another kind of Ransomware, is the well-known Cryptolocker, which encrypts system files and asks for ransom for decryption. Removing Cryptolocker is easy, but decrypting the files is virtually impossible. The average user may not miss something important, but small businesses? Therefore, for threats like these, good is the prognosis!
- Trojan Horse or just Trojan. From our name it refers to Homer's Iliad, the trick used by the Greeks to enter Troy. It was none other than the Trojan horse. In short, it is not what it seems. Trojan on computers can be a normal program, which while performing all normal functions, actually carries malicious code (Ransomware, Virus, etc.). Trojans do not act autonomously, but depend on the actions of the user. That is, you have to use a trick (eg via e-mail) to install the malicious program that spreads through the Trojan on your own computer. For example, it may seem that someone is sending you a photo (.jpeg). As soon as you click to see it, you automatically install a malicious program.
- Rootkits. Είναι λογισμικό το οποίο μπορεί να ανήκει πολύ εύκολα σε οποιαδήποτε από τις παραπάνω κατηγορίες. Αυτό το λογισμικό έχει την ιδιαιτερότητα να κρύβει κάποια κακόβουλα προγράμματα ώστε να μη γίνονται ορατά από το λογισμικό ασφαλείας. Η διαφορά με τα υπόλοιπα είναι πως, το Rootkit απο το “root” στο Unix που σημαίνει πρόσβαση σε επίπεδο διαχειριστή, μπορεί να εγκατασταθεί τόσο βαθιά στο σύστημα που να είναι αδύνατον να εντοπιστεί με τα κλασσικά προγράμματα Antivirus. Παραδείγματα απο μόλυνση rootkit είναι όπως είπαμε παραπάνω με τη Sony, επίσης η Sony με την αναβάθμιση του firmware του Playstation3 στην έκδοση 3.56, εισήγαγε στο λειτουργικό μέσω ενός rootkit, το μπλοκάρισμα όλων των MAC Address στο Playstation Network, όσων είχαν κρακαρισμένα συστήματα. Και απο την χώρα μας δεν έλειψαν τα χτυπήματα rootkit, το 2004 – 2005, το γνωστό Ελληνικό Watergate, ή ( Greek wiretapping case) Ελληνική υπόθεση υποκλοπών, με την παρακολούθηση συνομιλιών μέσω κινητών τηλεφώνων επιφανών Ελλήνων. Η λίστα είναι ατελείωτη, μπορούμε να κάνουμε ανάλυση 1000 σελίδων..
- Ad-ware, or advertising supported software. Advertising, meaning advertising! It is nothing more than the known pop-up μέσω του broswer, που όταν ενσωματωθούν στο σύστημά μας, παρακολουθούν τις συνήθειες αναζήτησης του χρήστη και προσαρμόζουν τη λειτουργία τους. To pop-up μπορεί πολλές φορές να έχει τη χρήση trojan, προσπαθώντας να παραπλανήσει τον χρήστη με τη γνωστή μέθοδο, “κερδίσατε κάτι κάντε κλίκ εδώ”, είτε “ο υπολογιστής σας μολύνθηκε κάντε κλικ για δωρεάν σκανάρισμα”, είτε το πιο πιασάρικο ” είμαι η Τσέσικα και βρίσκομαι 4 χιλιόμετρα μακριά”. Τα παραπάνω δεν είναι τίποτα άλλο, απο παραπλάνηση για εγκατάσταση κακόβουλων προγραμμάτων. Αυτό έχει σαν αποτέλεσμα, το “κόλλημα” του υπολογιστή και επίσης την μεγάλη αναμονή για connection on the Internet. The feeling that the broswer weighs something tons. It is due to the use of system resources by the infection.
- Zero - Day Malwares. They are unknown viruses computers, or other malicious threats, for which Antivirus does not yet have detection signatures available. Browsers are the usual recipients of these attacks, until companies release patches via update to fix the exploit.
- Rogue Applications. Apps that prompt the user to pay money to remove any Malware found in his system. It goes without saying that all this is virtual and is nothing but exploitation and intimidation, and the opposite is the case, by choosing to scan, you are a victim of Malware attack.
- Botnet. It is a network of infected computers, which are used by the perpetrators for malicious attacks, without the approval or knowledge of the owner. Each of our computers can be part of this network. 2014 saw the biggest Botnet dismantling, by the FBI in collaboration with the local authorities of each state, Zeus Botnet. The photo shows how much it had evolved.
The list is endless, these are some of the Malwares that the average user will encounter from daily use of the internet. Below we will see ways to deal with if we are infected, and also ways to predict it.
Ways to Tackle Tips
First of all, what should make us think that something is wrong?
- The computer is slow to perform specific actions that we are requesting to perform, eg open the broswer. We have unreasonable consumption of resources, and we do not have any "gluing" process.
- The mouse pointer moves on its own without touching the mouse (this may be a hardware failure if it is not).
- You perceive unauthorized connections to various accounts.
- Various windows open unexpectedly.
If you have any of these, this means that you have probably fallen victim to a Malware attack. What we should do when we have already been the victim of an attack. The only certainty is that we do not restore the computer to factory conditions (that is, format). With a fleece, we do not burn the quilt!
Fortunately there are many free programs for every occasion, which offer 100% cure and most importantly, inexpensive.
AdwCleaner
A great tool for removing broswer's toolbars and ad-wares, such as translation Babylon search, or ask.com toolbar etc., is AdwCleaner.
AdwCleaner is a tool for detecting and removing:
- Adware.
- PUP / LPI (potentially unwanted programs).
- Toolbars.
- Hijacker.
Note: Many free antivirus, use it ASK Toolbar as part of their free edition. If you remove the ASK using AdwCleaner, it will no longer work properly. Therefore, if you use these programs you can use the following instructions to access the options screen, where you should deselect the Ask Toolbar removal.
Instructions for use :
- Download AdwCleaner on your desktop.
- The program does not install, but it runs autonomously [portable].
- Open the program by double-clicking.
- Click [Search] and wait for the scan.
- When the scan is finished, a report appears.
- Click to delete the infected findings (after making sure that we do not use another program that requires the use of a tollbar).
- A Log File is saved in C: \ AdwCleaner [R1] .txt
Notes:
- The [logfile] report report is stored in C: \. AdwCleaner [R1] txt
- By pressing the "Unistall" button the program will simply copy itself with the logFile it created.
Author: Xplode
License: Free
Operating System: Windows XP / Vista / 7 / 8
32-Bit and 64-Bit
4.1.1.1
File Size: 2.03 MBs
Downloads: 23,757,968
Last Updated: 02 / 18 / 15 02: 20: 02 PM EST
Malwarebytes
The free version of Malwarebytes does not protect your computer in real time, but at any time, whenever the user decides, to check, always updating the latest update program for free.
It is more specialized than the classic antivirus in threats such as Spywares and Rootkits and Zero - Day Malwares, worms, trojans, rootkits, dialers, spyware, & rogue applications, ransomwares. So it's good to regularly check the system with Malwarebyte, a k does not run alongside the existing antivirus, but runs whenever we decide.
System requirements:
- Microsoft® Windows Vista, Windows 7, Windows 8 (32 bit and 64 bit).
- Microsoft® Windows XP Service Pack 2 or later.
- Microsoft® Internet Explorer 6 or newer.
Hardware Requirements:
- 800MHZ CPU or faster.
- 256MB of RAM (512MB or more recommended).
- 20MB free hard disk space.
- 800 × 600 or greater screen resolution.
- Active internet connection to update the program.
Author: MALWAREBYTES CORPORATION
License: Free
Operating System: Windows XP / Vista / 7 / 8
32-Bit and 64-Bit
2.0.4.1
File Size: 19.4 MBs
Comodo Internet Security
Comodo offers for free a complete internet security platform that would be envied by many companies that offer their materials for rent! The Comodo platform includes the following features:
- Antivirus
- Anti-Spyware
- Anti-Rootkit
- Bot Protection
- Defense +: Protects critical system files and blocks real-time Malware before they are installed.
- Auto Sandbox Technology ™
- Memory Firewall
- Anti-Malware
System requirements:
- Windows 7 / Vista / XP SP2 32-bit
152 MB RAM / 400 MB hard disk space - Windows 7 / Vista / XP SP2 64-bit
152 MB RAM / 400 MB hard disk space
Note: As you know, free versions always come with some add-ons, Comodo add-ons are GeekBuddy, it is an application through which you can contact the manufacturer for any problem, it is understood that the tips will be paid if the free version is used . It is the Comodo browser, which is a variant of Google Chrome and is the PrivDog which has been described as "problematic". There is no problem, because it is easily removed from the add and remove programs.
Shielding the broswer
It is a good solution to calm down from ads and add-ons on websites, they are two extensions of the browser, which block anything add-on (ads etc), making surfing much calmer and reducing the loading time of a website significantly.
- Ghostery. It's an extension, which detects companies that watch surfing for their own statistics and showing ads. At Ghostery Knowledge Library, there are more than 1900 trackers. Ghostery detects trackers and lets the user decide who wants to isolate and who does not. It works completely anonymously and collects the following:
- Trackers recognized by Ghostery.
- The sites where Trackers were detected.
- The protocol on the page where Tracker was found.
- Information showing if the Tracker was blocked.
- The URL (URL) of the Tracker itself
- The time it took to load the page and the Tracker.
- The position of the Tracker on the page.
- The broswer you use.
- Which country you are in.
- Information about which version of Ghostery you use.
- Typical IP address information and server information (Please note that we do not keep an IP address history).
2. Adblock. Another extension of the browser that does the exact same job as the previous one. The only difference is that Adblock does not inform the user what it is blocking but, it supports blocking for Malware Domains. In other words, it blocks domains that were found to be spreading Malware.
- Adblock Privacy Policy avoids the collection of personal data, rather than what is required for the proper functioning of AdblockPlus.org. The data collected is anonymous and is deleted when it is no longer needed.
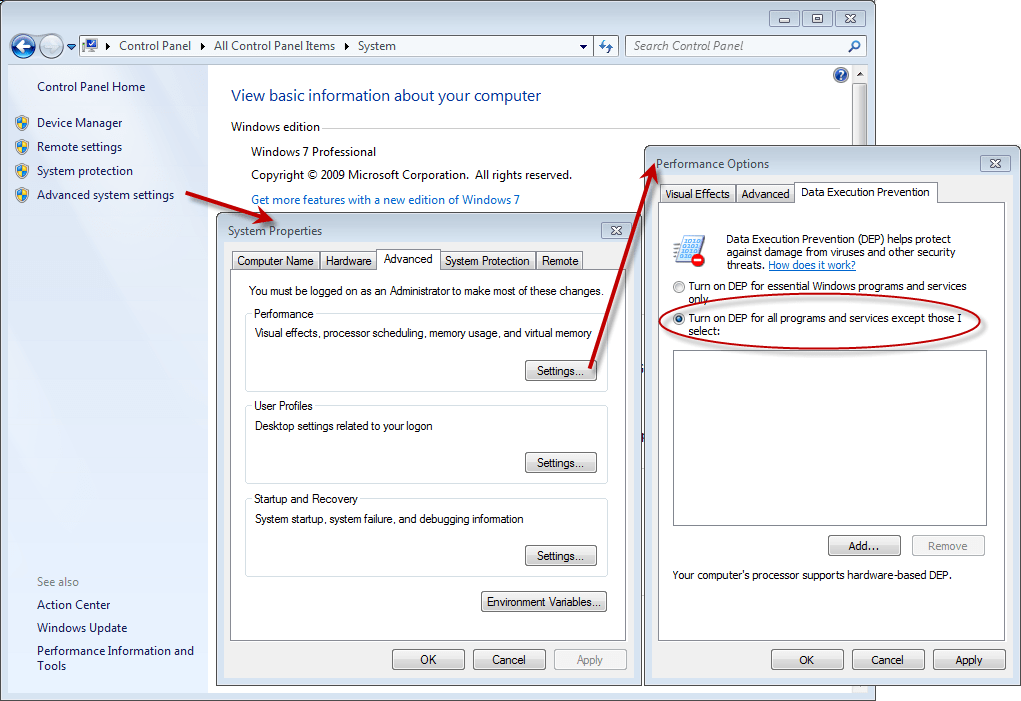
Enable Windows DEP.
Data Execution Prevention, or in abbreviations DEP. DEP is a security feature that can help prevent your computer from damaging viruses and other security threats. It helps protect your computer by monitoring programs to verify that the memory is used properly. If a program attempts (still executable) to execute code from the memory in the wrong way, DEP automatically shuts down the program. DEP is not enabled by default in Windows for all programs, must be enabled by the user, in the picture we see how.
Sandboxie.
Sandboxie which we have mentioned in another publication.
Some programs for checking & removing Rootkit.
- Sophos Rootkit Removal.
- Comodo Cleaning Essentials.
- Malwarebyte Anti-Rootkit (Beta).
- McAfee RootkitRemover.
- Kaspersky TDSSKiller.
In conclusion.
No antivirus program and no firewall will ever guarantee us, 100% Coverage and Protection, All we can do is reduce the chances of becoming a target. And how will this happen; Only by constantly updating and knowing the problem. The best antivirus and the best tip, we are ourselves. For this:
- We always keep it updated the antivirus programs we use.
- Doing often scans or set the program itself to make a shutdown when we do not use the computer.
- We always keep an eye on what we are entering and what we open up on the Internet.
- That it shows up on our own websites, we always have in mind that it is probably a trap.
- We use official copies of the operating system (anyone can embed a rootkit in a cracked version of Windows and distribute it through a torrent. CAUTION).
- When we install any free application on the computer, we never click "next" without reading what it says. Many toolbars are being installed in this way, because as we said above, they are add-ons to free apps.
- And generally, Surf with suspicion, in all areas.
Hy: It's my first official article on iGuru.gr, except for some other interference on topics. Thanks to the managers who gave me a step for publications, I hope that what I write will be significant and constructive. George!








me if they ask me anything to download and install to see a video or so I can never see it !!!!! BE CAREFUL PUT IT ON YOUR PC NOT TO RUN
Why don't you mention spybot?