ThePhish is an automated tool analysisphishing based on TheHive, Cortex and MISP.
It is a web application written in Python 3 and based on Flask that automates the whole procedure of analysis, starting from the extraction of the data from the header and body of an email to the processing and final reporting at the end of the process.
In addition, it allows the analyst to intervene in the analysis process and obtain further details about the email being analyzed if necessary.
To properly use the program with TheHive and Cortex, uses TheHive4py and Cortex4py , which are the client Python APIs, which allow using the REST APIs provided by TheHive and Cortex respectively.

Installation
$ git clone https://github.com/emalderson/ThePhish.git $ cd ThePhish / app $ sudo apt install python3-venv $ python3 -m venv venv $ source venv / bin / activate $ pip install -r requirements.txt
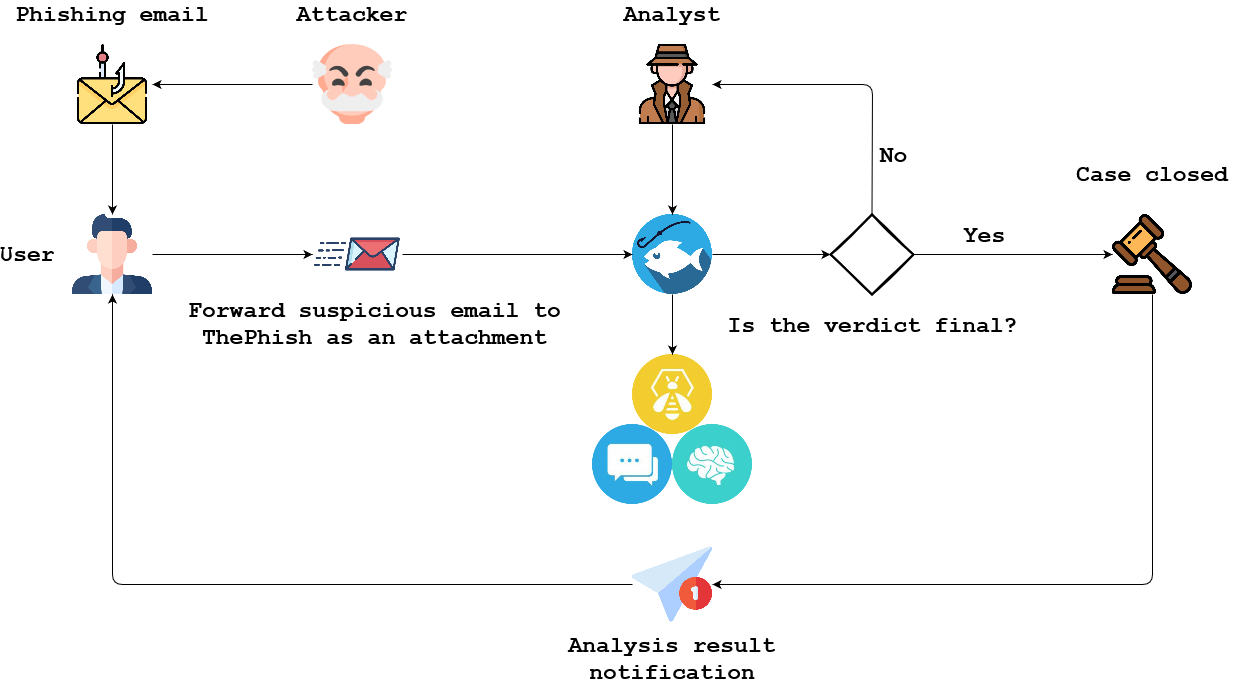
Operating procedure
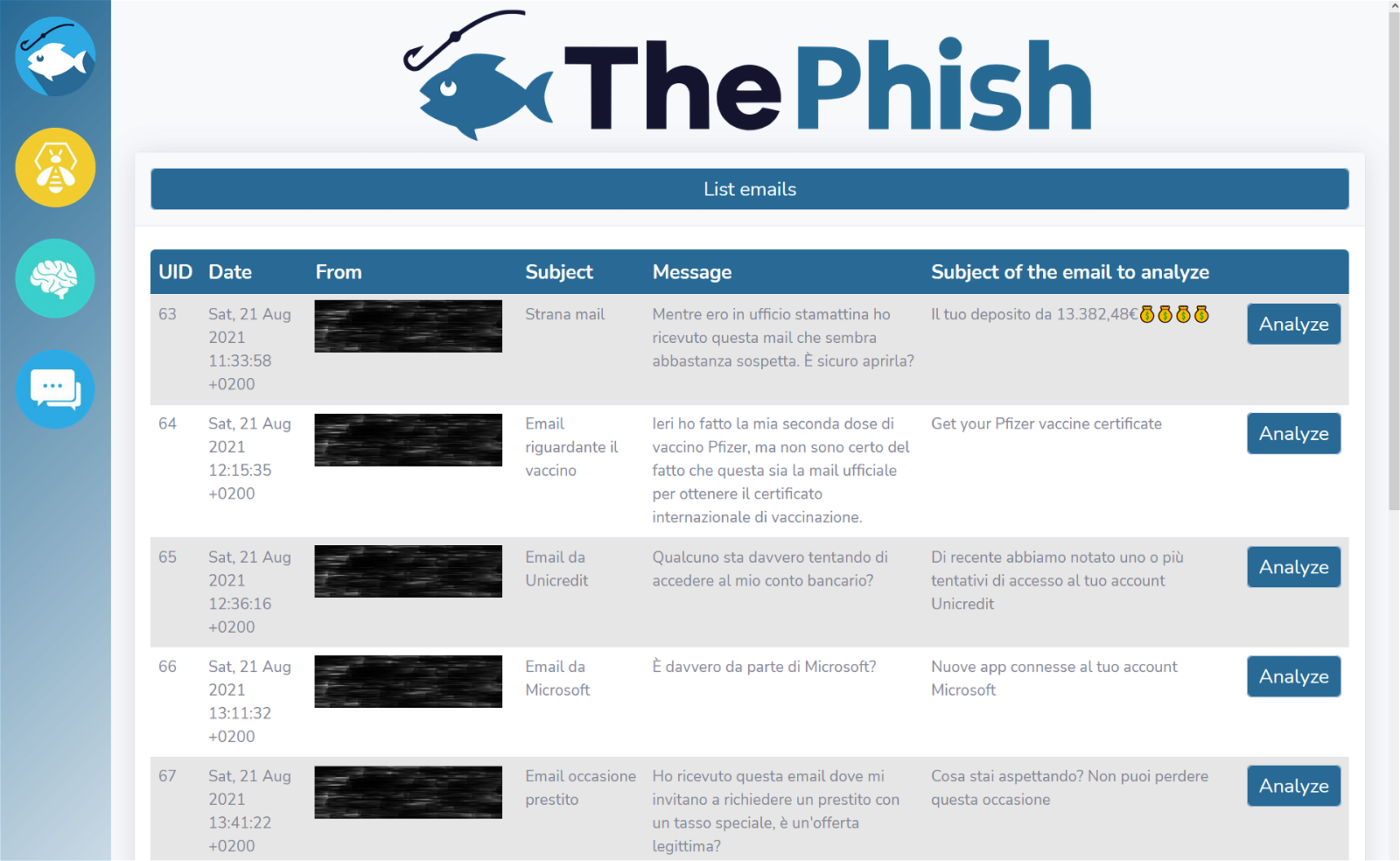
Application snapshots

Program analysts
- AbuseIPDB_1_0
- AnyRun_Sandbox_Analysis_1_0
- CyberCrime-Tracker_1_0
- Cyberprotect_ThreatScore_3_0
- DomainMailSPFDMARC_Analyzer_1_1
- DShield_lookup_1_0
- EmailRep_1_0
- FileInfo_8_0
- Fortiguard_URLCategory_2_1
- IPinfo_Details_1_0
- IPVoid_1_0
- Maltiverse_Report_1_0
- Malwares_GetReport_1_0
- Malwares_Scan_1_0
- MaxMind_GeoIP_4_0
- MetaDefenderCloud_GetReport_1_0
- MISP_2_1
- Onyphe_Summary_1_0
- OTXQuery_2_0
- PassiveTotal_Enrichment_2_0
- PassiveTotal_Malware_2_0
- PassiveTotal_Osint_2_0
- PassiveTotal_Ssl_Certificate_Details_2_0
- PassiveTotal_Ssl_Certificate_History_2_0
- PassiveTotal_Unique_Resolutions_2_0
- PassiveTotal_Whois_Details_2_0
- PhishTank_CheckURL_2_1
- Pulsedive_GetIndicator_1_0
- Robtex_Forward_PDNS_Query_1_0
- Robtex_IP_Query_1_0
- Robtex_Reverse_PDNS_Query_1_0
- Shodan_DNSResolve_1_0
- Shodan_Host_1_0
- Shodan_Host_History_1_0
- Shodan_InfoDomain_1_0
- SpamhausDBL_1_0
- StopForumSpam_1_0
- Threatcrowd_1_0
- UnshortenedLink_1_2
- URLhaus_2_0
- Urlscan_io_Scan_0_1_0
- Urlscan_io_Search_0_1_1
- VirusTotal_GetReport_3_0
- VirusTotal_Scan_3_0
- Yara_2_0
You can download the program from here.





