After the first shock from WannaCry ransomware, one of the worst malware ever released, security researchers continue to analyze it. As we have seen so far, some different samples of ransomware have been detected by 400.
Security researchers from Trustlook today announced that 386 has been recorded so far with different samples of WannaCry malware.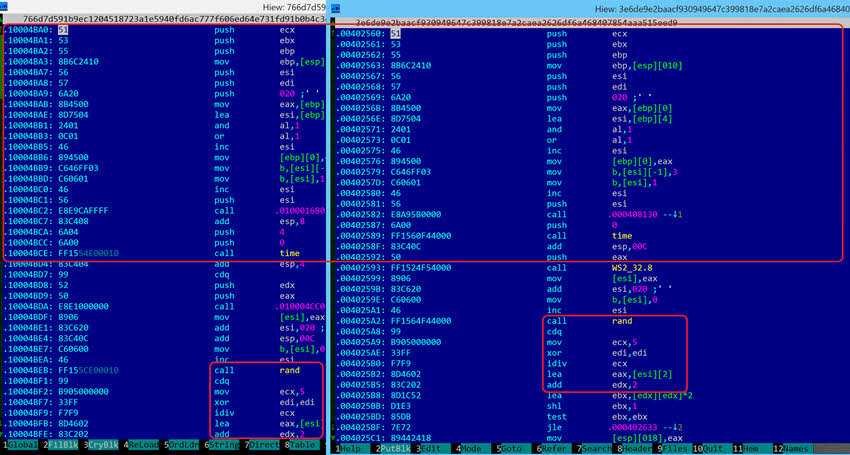
As you already know from previous publications, the WannaCry uses two tools hacking tools of the NSA leaked by Shadow Brokers hacking team. It EternalBlue is a tool that exploits a Windows vulnerability, while DoublePulsar helps spread the worm over networks.
The vulnerability in Windows is said to have been fixed by Microsoft, something that was needed to stop the attack, as it is believed that the original WannaCry infections did not come from a phishing campaign, but rather from the attackers who scanned for open ports.
As we mentioned in a previous post, Microsoft released another updated one version for Windows XP.
But although many of us thought that those who were infected by the evil software, they were using XP, a bit later the data showed that most of the devices that fell victim to WannaCry were running Windows 7.
The WannaCry was just the beginning, with its 386 samples. A new worm discovered by researchers, and called EternalRocks, uses seven hacking tools of the NSA, while WannaCry used only two. So far, EternalRocks has not been armed with any ransomware, trojans, etc., but this can happen at any time.





