Η company Uber was hacked Thursday afternoon, and the hackers shared snapshots of the company's internal systems, email dashboard and Slack server.

What appears from the screenshots shared by the hackers is that they were able to gain full access to several critical Uber IT systems, including the company's security software and Windows domains.
They also managed to break into the company's Amazon Web Services console, VMware ESXi virtual machines, control panel managementς email του Google Workspace και τον διακομιστή Slack, στον οποίο ο χάκερ δημοσίευσε messages.
Uber confirmed attack, tweeting that is in consultation with police and will release additional information as it becomes available.
The New York Times, who first reported the breach, succeeded and spoke with the hacker, who said they breached Uber after carrying out an attack social engineering to an employee and stole his password.
The hacker(s) then gained access to the company's internal systems using the stolen credentials.
Social Engineering
Social engineering (Social engineering) is the act of verbally manipulating individuals in order to extract information.
Although similar to trickery or simple fraud, the term is primarily associated with deceiving individuals in order to extract confidential information necessary to gain access to a computer system.
Usually the one applying it never comes face to face with the person who is deceiving or misleading. Although the term may not be accurate or successful it is now established.
Social engineering has become a very popular tactic in recent attacks against well-known companies, including Twitter, MailChimp, Robinhood and Okta.
HackerOne Vulnerability Reports Exposed
While it's possible the hacker stole data and source code from Uber, it appears he also had access to what could be its most valuable asset.
According to Yuga Labs security engineer, Sam Curry, the hacker also had access to program company's HackerOne bug bounty, where he commented on all of these company's bug bounties.
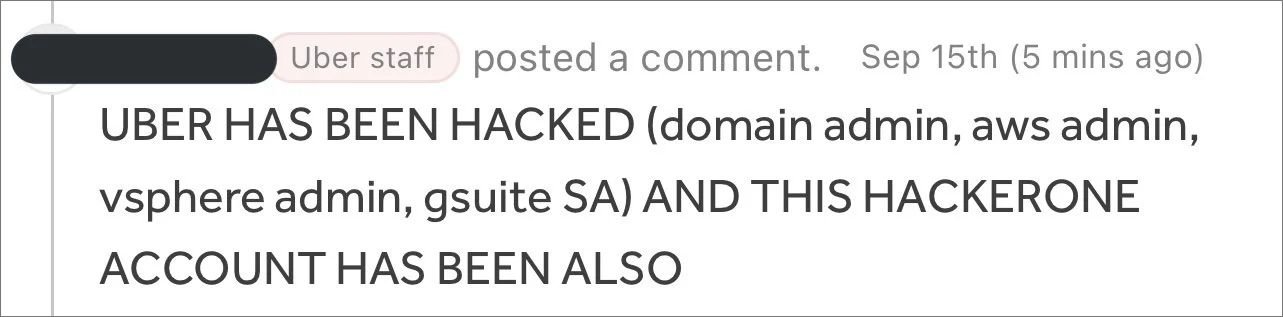
Curry said he first learned of the breach after the attacker left the above comment in a vulnerability report he submitted to Uber two years ago.
Uber runs a HackerOne bug bounty program where it allows security researchers to privately disclose vulnerabilities in its systems and applications in exchange for a bug bounty reward. These vulnerability reports are intended to be kept confidential until a patch is published to prevent attackers from exploiting them in attacks.
As you can see the attacker downloaded all the vulnerability reports before losing access to Uber's bug bounty program. This likely includes unpatched vulnerability reports, presenting a serious security risk for Uber in the future as well.





