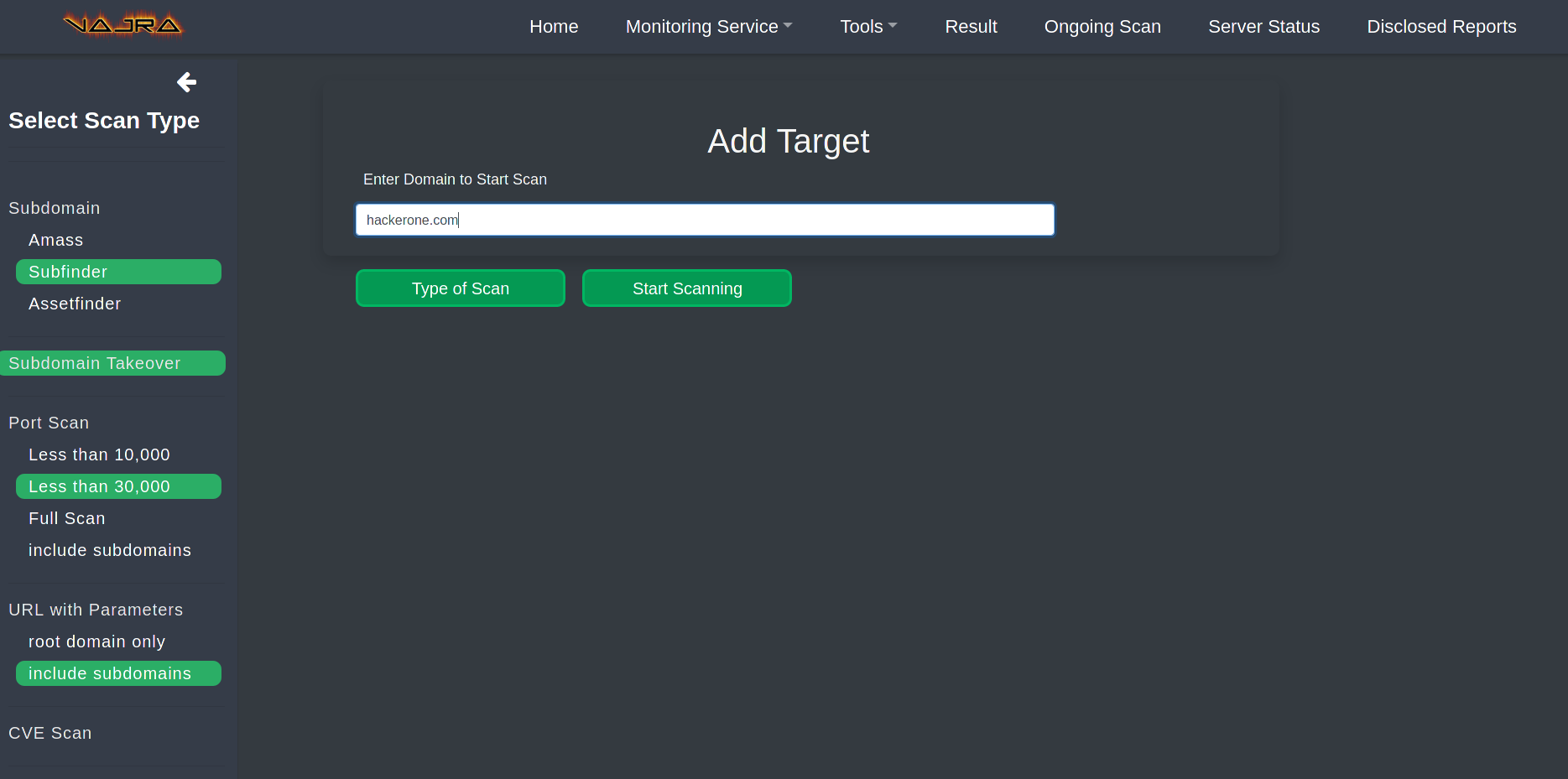
Vajra is an automated attack and penetration testing framework. It has a highly customizable scanning capability based on target range. Instead of performing the entire scan on the target, it performs only those scans you have selected, which will minimize unnecessary motion, and saves the Results in CouchDB.
It uses common open source tools that every Bug Hunter runs during their testing on a target. It performs the scanning process through the program tours with a very simple user interface, which makes it very friendly for beginners.
Basic features
- Targeted special scan
- Perform multiple scans simultaneously
- Extremely customizable scan based on each user's requirements
- Friendly Web UI for novice users
- Extremely fast
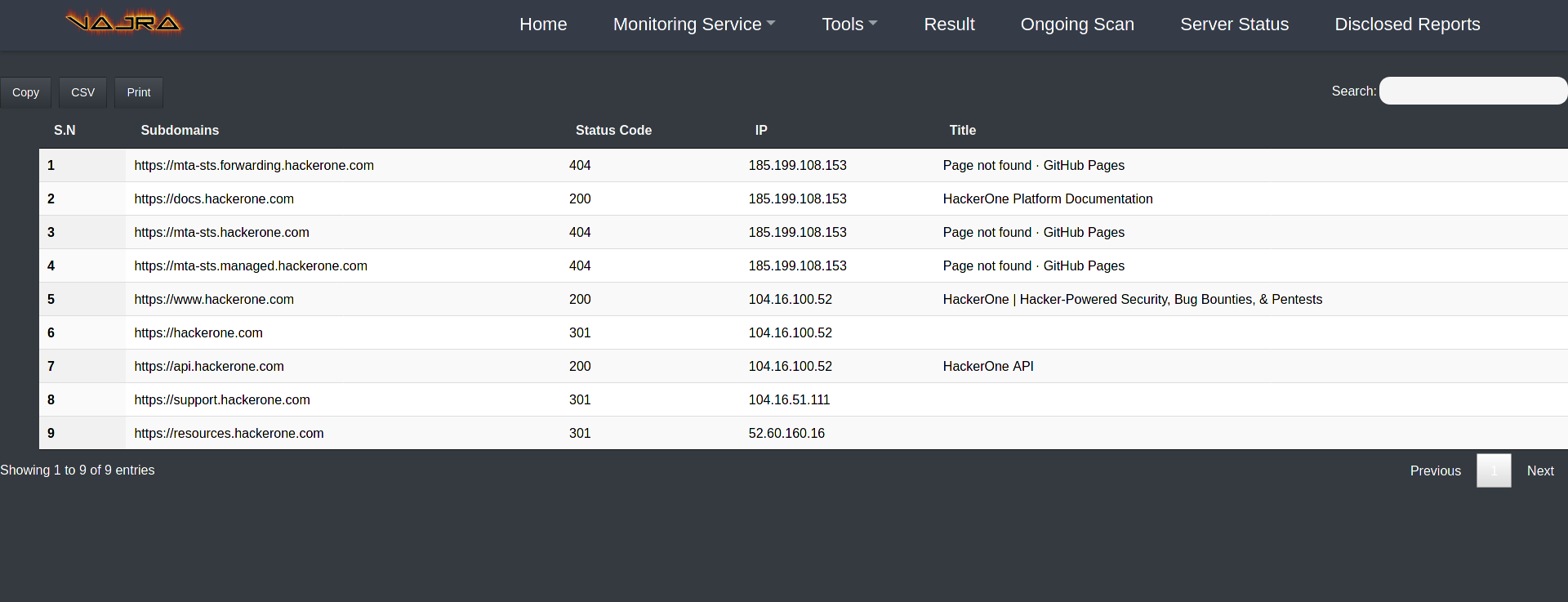
- Export result to CSV or copy directly to clipboard
additional characteristics
- Subdomain Scan with IP, Status Code and Title.
- Subdomain Takeover Scan
- Port Scan
- Endpoint Discovery
- Endpoints with Parameter Discovery
- 24/7 Monitor Subdomains
- 24/7 JavaScript Monitor
- Templates Scan using Nuclei
- Fuzz endpoints to find hidden endpoints or critical files (eg .env)
- Extract JavaScripts
- Fuzz with Custom Generated wordlist
- Extracts Secrets (eg api keys, hidden javascripts endpoints)
- Checks for Broken Links
- Filter Endpoints based on extensions
- Favicon Hash
- Github Dorks
- CORS Scan
- CRLF Scan
- 403 Bypasser
- Find Hidden Parameters
- Google Hacking
- Shodan Search Queries
- Extract Hidden Endpoints from JavaScript
- Create target based Custom Wordlist
- Vulnerability Scan
- CVE Scan
- CouchDB to store all scan output
Installation
Information about installing the program, you will find here.
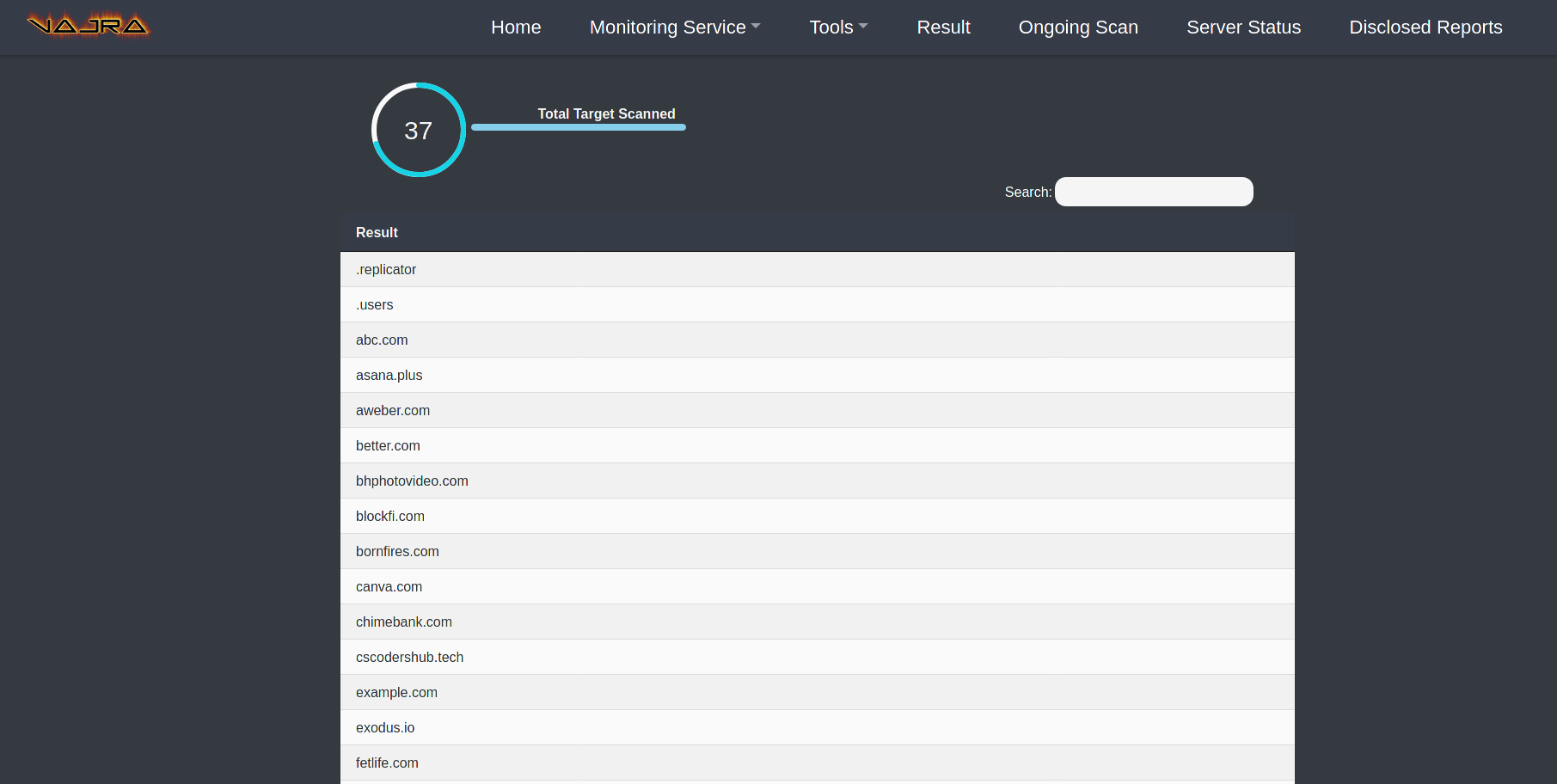
Application snapshots
Video guide
https://www.youtube.com/watch?v=WLurj5Lg8cI
You can download the program from here.






