Today I decided to share my take on basic networking knowledge to make sure all iguru readers have the basic skills I consider fundamental to hacking.

In fact, without basic networking and Linux skills, becoming a hacking ace will definitely remain out of your reach.
In this first part of the Network Basics guide series, I'll cover some of the basics of IP addresses, NAT, DHCP, and ports.
IP Addresses
Internet protocol addresses (IP addresses) make the world go round. Or, at least, they allow us to send emails, use Skype and surf the web. They are almost as important as the world spinning!
On any digital device (computer, laptop, phone, tablets etc) is assigned an IP address and this is what allows us to communicate and connect to it. Think of an IP address as something similar to your home address. Without this address, no one would be able to find you and send you postal mail.
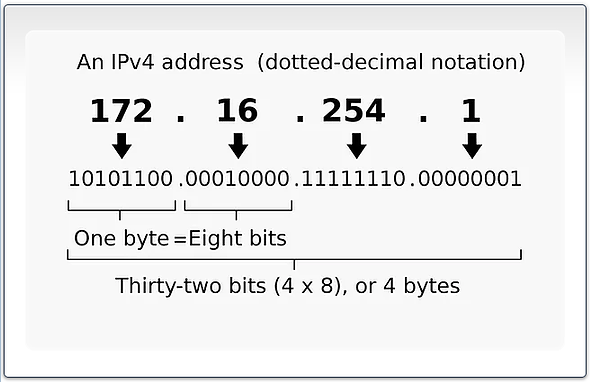
The IP addressing system we currently use is known as IP version 4 or IPv4 (we'll cover the upcoming IPv6 in a later tutorial). It consists of 32 bits of four octets, or four groups of 8 bits (on/off switches).
For example, 192.168.1.101. Each of the numbers between the periods (.) is the decimal equivalent of 8 bits. This means we take the base 2 number that computers use which is represented by 8 bits and convert it to the decimal numbers that people are more used to working with (see the diagram below). Each of the octets (8 bits) is capable of representing numbers in the range from 0 to 255 (2 to the 8th power).
IP address classes
IP addresses are generally classified into three categories and the ranges are as follows:
- Class A: 0.0.0.0 – 127.255.255.255
- Class B: 128.0.0.0 – 191.255.255.255
- Class C: 192.0.0.0 – 223.255.255.255
In a future tutorial, we'll cover subnetting and the subnet masks that differ with these different IP classes.
Public vs. Private IP Addresses
It is important to note that the IP addressing system has its limitations. The biggest limitation is that there are not enough IP addresses to cover all the devices that need to connect to the internet. The IPv4 system we are working with now has only 4,3 billion IP addresses. With 7,3 billion people on the planet and many more devices, this is definitely not enough.
As a result, a system was developed to reuse a pool of IP addresses that are used within a local network and cannot be used on the internet. These addresses can be used again and again within each local network, but not over the internet, thus maintaining the number of IP addresses needed to keep the world turning.
These private addresses include:
-
192.168.0.0 – 192.168.255.255
-
10.0.0.0 – 10.255.255.255
-
172.16.0.0 – 172.16.255.255
You may have seen private IP addresses starting with 192.168.xxx.xxx or 10.xxx.xxx.xxx.xxx in Kali when you type ifconfig.
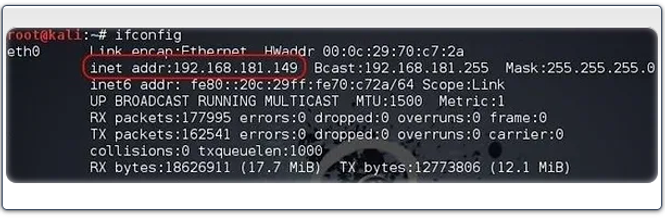
This is your private IP that can only be used on the local network. To communicate over the Internet, it must be translated to a public IP by a NAT device (see NAT below).
DHCP
Dynamic Host Configuration Protocol (DHCP) dynamically assigns IP addresses. This means that you do not always have the same IP address. Most of the time, these IP address assignments are made on a local network. Remember that on local networks we use private IP addresses.
When each device connects to the local network, it must request an IP address. This device sends this request to the DHCP server, which then assigns an IP address to that system for a fixed period of time, known as a “lease”.
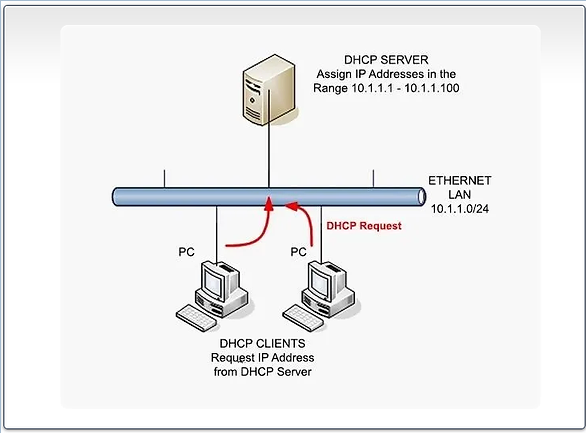
Each time you connect to the local network, you are likely to receive a different (dynamic) IP address, but usually in the same range. For example, 192.168.0.0 – 192.168.255.255.
NAT
Network address translation (NAT) is a protocol by which internal private IP addresses are "translated" to an external public IP address that can be routed over the Internet to its destination.
Remember that the private IP addresses of systems inside the LAN cannot use their IP addresses on the internet because they are not unique (each LAN uses essentially the same IP addresses inside its network).
The NAT device accepts requests to traverse the internet from an internal machine. It then records the IP address of that machine in a table and converts the IP address to the external IP address of the router.
When the packet returns from its destination, the NAT device examines the stored table of the original request and forwards the packet to the internal IP address of the system that made the original request within the local network. When it works properly, individual systems and users are not even aware that this translation is taking place.
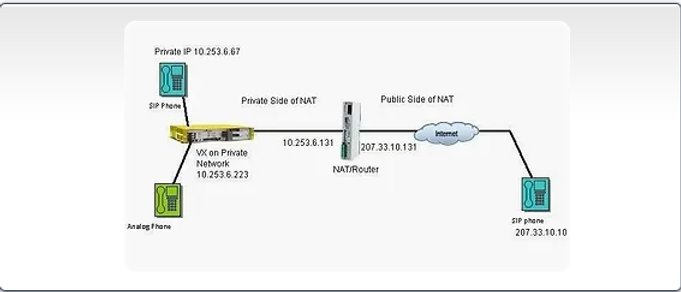
For example, the diagram above shows two phones with private IP addresses behind a device that acts as both a NAT device and a router. Devices use their private IP addresses within the local network, but when they want to communicate over the Internet, the NAT device translates them to one of the public IP addresses that are unique to the Internet. That way, routers along the path know exactly where to send the packets.
Ports
Ports are a type of sub-address. The IP address is the primary address and the door is the subaddress. Using a difficult but effective metaphor, think of the IP address as the street address of a building and the port as the apartment number.
I need the street address to get to the right building, but I need the apartment address to find the one I'm looking for. The same goes for ports. The IP address points us to the correct machine, but the port points us to the correct service, say HTTP on port 80.
There are 65.536 (2 raised to the 16th power) ports. The first 1.024 are generally referred to as “shared ports”. People apparently don't remember all 65.536 ports (unless they're geeks) or even the 1.024 most common ports. As a hacker, security engineer, and/or network engineer, there are a few ports you should know inside out:
-
20 FTP
-
21 FTP
-
22 SSH
-
23 Telnet
-
25 SMTP
-
53 DNS
-
69 TFTP
-
80HTTP
-
88 Kerberos
-
110 POP3
-
123 NTPs
-
135 Microsoft's RPC
-
137-139 Microsoft's NetBIOS
-
143 IMAP
-
161 SNMP
-
389 LDAP
-
443 HTTPS or HTTP over SSL
-
445 SMBs
-
500 IKEs
-
514 syslogs
-
3389 RDP
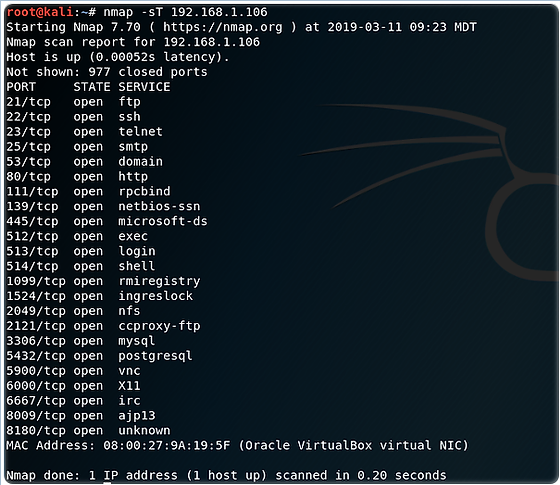
We can use a tool like the Nmap to see what ports are open on a system. This way, the security engineer or hacker can see what ports are open and what services are running on the target system.
Part two of the networking guide series (with themethose related to subnetting, IPv6, TCP/IP, and more) in the near future, so stay tuned!






Indeed, the range must be corrected in Private because
report “172.16.0.0 – 172.16.255.255” where it is wrong,
while the correct one is 172.16.0.0 – 172.31.255.255.
Otherwise very nice article! :)
the range for private networks 172.16.x is not correct.
In the local networks, we give the spectrum we want.