An invisible threat vector, also known as StrongPity, spent the summer attracting users software κρυπτογράφησης σε «watering holes» και «μολυσμένα» προγράμματα εγκατάστασης, σύμφωνα με εργασία που παρουσιάστηκε στο Virus Bulletin, από τον ερευνητή ασφάλειας της Kaspersky Lab Kurt Baumgartner. Οι χρήστες στην Ιταλία και το Βέλγιο ήταν αυτοί που επλήγησαν περισσότερο, αλλά επηρεάστηκαν επίσης και χρήστες στην Turkey, North Africa and the Middle East.
StrongPity is a technically competent APT-style attack vector interested in cryptographically data and communications. Over the past few months, Kaspersky Lab has noticed a significant escalation of its attacks on users looking for two very important encryption tools: the WinRAR archiver and the TrueCrypt encryption system.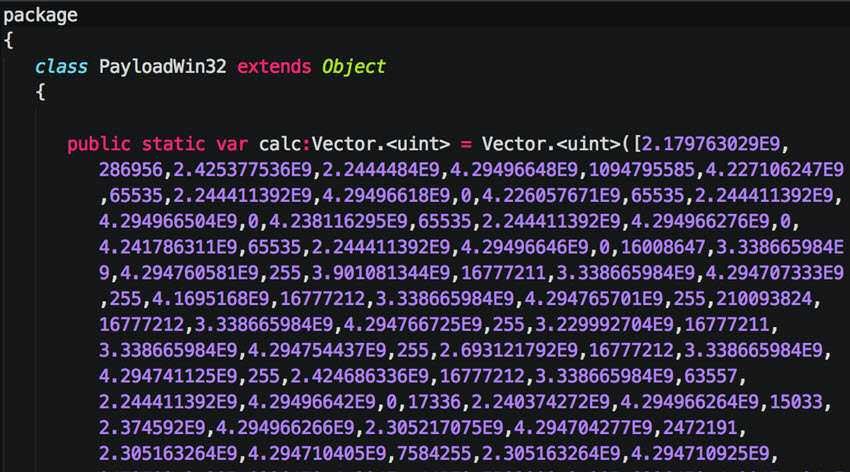
The StrongPity malware includes components that give attackers complete control over the victim's system. It essentially enables them to steal its content disk but also to "download" additional units to gather communications and contacts. Kaspersky Lab has so far detected visits to StrongPity websites and the presence of its tools on more than a thousand target systems.
«Watering holes "and" infected "installation programs
In order to trap their victims, the attackers made false websites. In one case, they carried two letters into one domain name to trick customers into thinking it was an official WinRAR software installation site. They then placed a prominent link on a WinRAR distribution site in Belgium, apparently replacing the "suggested" link on the site with that of the malicious domain. As visitors navigated this site, this led unsuspecting users to the "infected" StrongPity installer. The first successful redirection detection by Kaspersky Lab took place on May 28, 2016.
Almost simultaneously, on 24 May, Kaspersky Lab began to detect malicious activity on an Italian WinRAR distribution site. In this case, however, users were not redirected to a fraudulent website, but they accepted the malicious StrongPity installation program directly from the distributor's website.
StrongPity also redirected visitors to popular web pages with free software in TrueCrypt installation programs that were "infected" by Trojan. This activity was still in progress at the end of September.
Malicious links from the WinRAR distribution websites have now been removed, but by the end of September, the malicious TrueCrypt site was still operational.
Geography of the attacks
Kaspersky Lab data reveals that within a week the malware provided by Italy's distributor's website appeared in hundreds of systems across Europe and North Africa / the Middle East, with many more potential "infections". During the summer, Italy (87%), Belgium (5%) and Algeria (4%) were most affected. The geography of the victims from the 'infected' website in Belgium was similar, with users in Belgium accounting for half (54%), with over 60 successful attacks.
Attacks on users through the fraudulent TrueCrypt site reach up to May of 2016, with 95% of the victims being in Turkey.
«The techniques used by this threatening carrier are smart enough. They resemble the approach adopted at the beginning of 2014 by APT Crouching Yeti / Energy Bear, in which lawfully installed software programs for industrial control systems that were 'infected' by Trojan and compromised genuine software distribution websites. These tactics are an undesirable and dangerous trend the security industry has to deal with. The search for privacy and integrity of data should not expose the individual to harmful "waterholes". "Waterhole" attacks are inherently vague and we hope to stimulate debate about the need for easier and improved verification of the delivery of encryption tools», δήλωσε ο Kurt Baumgartner, , Principal Security Researcher of Kaspersky Lab.
Kaspersky Lab identifies all StrongPity components with the names: HEUR :. Trojan.Win32.Strong Pity.gen and Trojan.Win32.StrongPity * and other general scans.
For more information about StrongPity's "watering hole" attacks, you can visit the dedicated website Securelist.com.
For information on mitigating threats with "infectedo »encryption software, you can visit the blog Kaspersky Business.





