Microsoft added a small change for them users των Windows 10. Αν χρησιμοποιείτε το αρχείο HOSTS για να αποκλείσετε την τηλεμετρία ή τις ενημερώσεις των Windows 10, έχουμε κακά νέα για εσάς.
Ο Microsoft Defender it will mark it as malicious and display “critical level” warnings.
It is known that Windows 10 does not use the HOSTS file to block addresses on specific Windows servers. So the Microsoft Defender behavior change was probably to be expected.
The Hosts file can be modified using any program processingof text, but the editing application should be started with administrator rights. The hosts file is located in a system folder, so applications without administrator rights will not be able to save it.
The Hosts file consists of lines of text. Each row must include an IP address in the first column followed by one or more hostnames. The text columns are separated by a space.
Lines starting with a # character are not read by the operating system system.
So if you put Microsoft servers in the HOSTS file and send them to the internal address 127.0.0.1, you will stop the operating system from accessing the actual servers.
So there comes Microsoft Defender which prevents you from saving this file and will show you the following dialog.
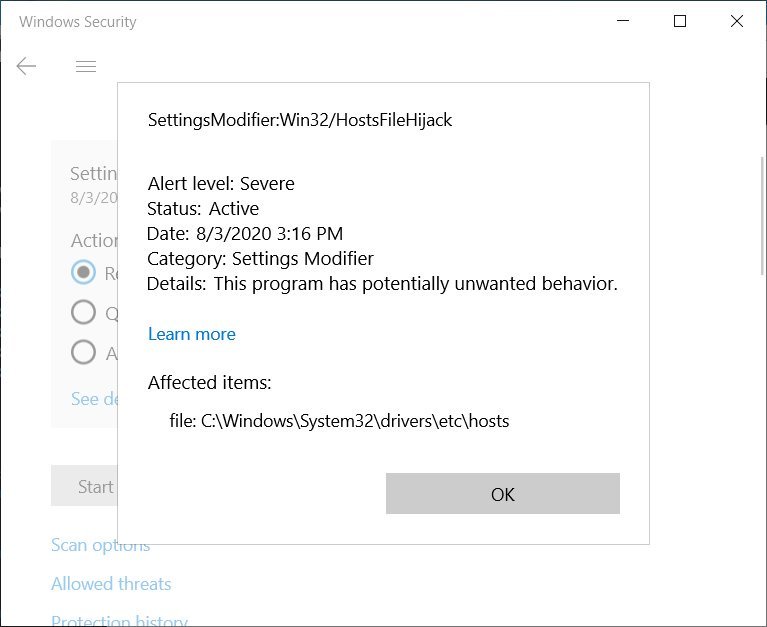
Note: SettingsModifier: Win32 / HostsFileHijack is a new, proprietary category for the modified file. It seems that Microsoft recently updated its Microsoft Defender definitions to track when their servers are added to the HOSTS file.
As BleepingComputer reports, the following HOSTS entries will enable it detection:
www.microsoft.com
microsoft.com
telemetry.microsoft.com
wns.notify.windows.com.akadns.net
v10-win.vortex.data.microsoft.com.akadns.net
us.vortex-win.data.microsoft.com
us-v10.events.data.microsoft.com
urs.microsoft.com.nsatc.net
watson.telemetry.microsoft.com
watson.ppe.telemetry.microsoft.com
vsgallery.com
watson.live.com
watson.microsoft.com
telemetry.remoteapp.windowsazure.com
telemetry.urs.microsoft.com
If you decide to clear this "threat" with Microsoft Defender, the company will restore the HOSTS file to its default contents.
Modifying the HOSTS file is not a good idea anyway, especially if it is done improperly or by malware.
However, for users who really know what they are doing, it is a great way to leave less control of their operating system in the hands of Microsoft, while protecting their privacy.






I wrote a comment 3, 4 times and before I pressed the "post" I deleted it as in the time needed to press the button, I was thinking more and more.
My thoughts were:
a) I the company MS so I want so I do, in my own merchandise.
b) then I thought: we will find a new way to exclude part of the core, namely the one that has to do with the "telemetry" of everything.
finally c) I thought “not @@@@@@@ re MS? I will return to my "butt" and jump and @@@@@@@.
In the end, however, I calmed down in the present: is everything "intentional and passive" since, using goods (software platform) that comes from everywhere and in fact, if it did not have the signature of a giant (MS) would be in " narrow ”for (almost) abuse of a monopoly product.
Υγ. I clarify that - still - I have not had a stroke and the time I need to press "publish" is minimal, but the thoughts are rapid. Especially when you read a text that describes "we will @@@@@@@ and you do what you want".
yes George personal responsibility and personal choices can not come second and thank you for the suggestion. But then we go to "how much truth can you stand" and what effect will this have on my health…
The first stage of change is denial, and I have pressure :) to read comments that consider the truth an insult.
Unfortunately, following the stereotypes established by others is the way of many; it has always been