LoLBins are Microsoft-signed executables (pre-installed or downloaded) that can evade detection when downloaded, installation or executing malicious code.
They can also be used by attackers in their attempts to bypass Windows User Account Control (UAC) or Windows Defender Application Control (WDAC) and obtain access on already compromised systems.
WSUS / Windows Update client (wuauclt) is a utility located in % windir% \\ system32 \\ which gives users some control over some of the functions of the Windows Update Agent from the command line.
Allows you to check for new updates and install them without having to use the Windows user interface, but instead enable them from a command prompt window.
The use of choice ResetAuthorization Allows you to start a manual update check either on the locally configured WSUS server or through the Microsoft Update service according to Microsoft.
However, MDSec researcher David Middlehurst has discovered that wuauclt can also be used by attackers to execute malicious code on systems Windows 10 loading it from a specially designed malicious DLL with the following command line options:
wuauclt.exe / UpdateDeploymentProvider [path_to_dll] / RunHandlerComServer
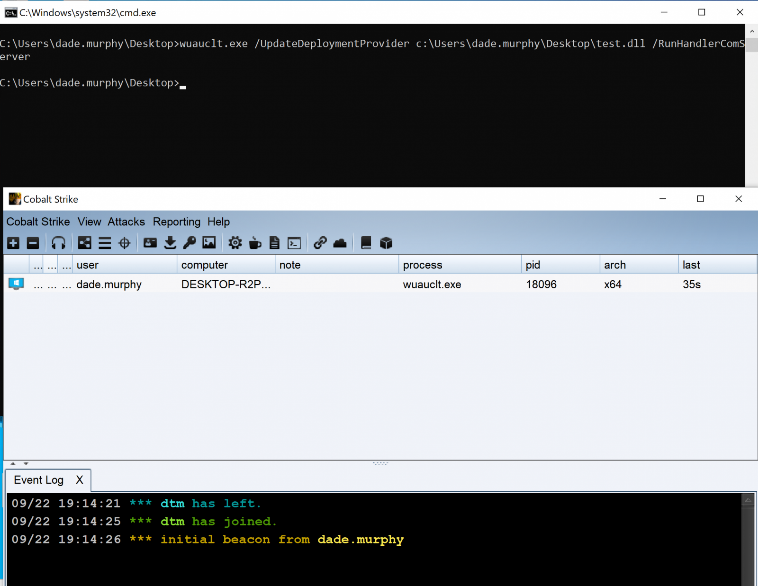
As shown in the screenshot above, Full_Path_To_DLL is the absolute path to the specially constructed DLL file of the attacker that would execute code in the attachment.
This technique is categorized by MITER ATT \ CK as running a binary proxy through Rundll32 and allows intruders to bypass the antivirus program, scan applications, and validate digital certificates.
In this case, it does this by running malicious code from a DLL that was loaded using a Microsoft-signed binary, Windows Update (wuauclt).
After discovering that wuauclt could also be used as LoLBin, Middlehurst also found a sample that used it for online attacks.
Microsoft recently updated its Microsoft 10 Defender antivirus solution to Windows XNUMX by quietly adding a (potentially malicious) way to download files to Windows devices.
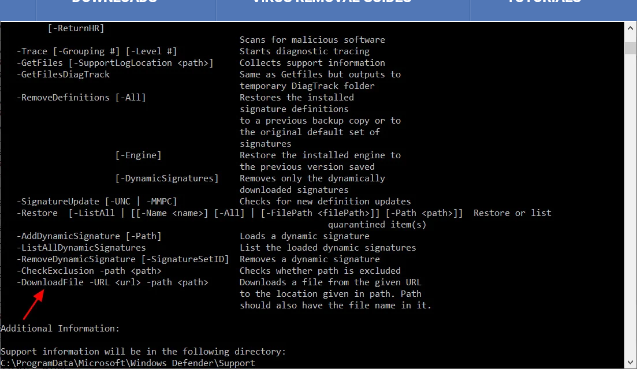
Microsoft later removed this feature from MpCmdRun.exe (the Microsoft Antimalware Service Line Utility).





