Passwords are used for thousands of years as a means of identification with others and in recent years have been used in computers. It's a simple idea. Information that is kept confidential between individuals and used to "prove" identity
Passwords in the IT environment appeared in the 1960s on mainframe computers (large servers with remote "terminals" for user access). Today they are used everywhere, from the PIN we enter at the ATM, to the connection to our computers and various websites.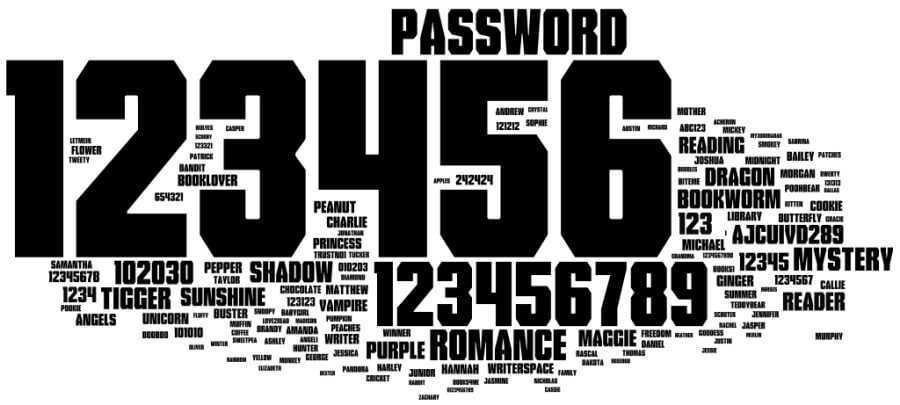
Until relatively recently, a good password could be a word or phrase consisting of six to eight characters. Today there are instructions of minimum length and this is due to the "entropy".
When we talk about passwords, entropy is the measure of predictability. The math behind this is not complicated, but let's look at it with a simpler measure: the number of possible passwords.
If a one-character password contains only one lowercase letter, there are only 26 possible passwords from "a" to "z". If we put the capital letters, we increase the number of possible passwords to 52 possible codes.
The number of possible passwords continues to grow as the length increases and other types of characters are added.
Making a password bigger or more complex significantly increases the number of possible passwords which means more secure passwords.
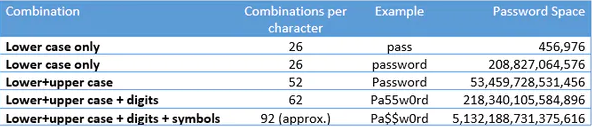
Looking at the figure above, it is easy to understand why we encourage the use of large passwords in uppercase and lowercase letters, numbers and symbols. The more complex the password, the more effort it takes to guess it.
However, the problem with password complexity is that computers are very efficient at repeating tasks, including guessing passwords.
Last year, we had a record of one computer. It achieved a rate faster than 100.000.000.000 guesses per second.
Utilizing this computing power, criminals can invade systems by bombarding them with as many password combinations as possible, in a process called Brute Force.
And with cloud-based technology, eight-character password cases can be achieved in just 12 minutes and cost just $ 25.
Also, because passwords are almost always used to access sensitive data or important systems, this motivates criminals to actively seek them out. Thus a lucrative password market has been created through it Internet, which has email addresses, passwords and even usernames.
How are site passwords stored?
Website passwords are usually stored securely using a mathematical algorithm called hashing. A hashed password is not recognizable and cannot be converted back to the password (irreversible process).
When you try to log in, the password you enter is encrypted and using the same procedure is compared to the version stored on the site. This process is repeated each time you log in.
For example, the password "iguru.gr" has the value "5DA1B35167D7A6583AE228B2AF769AEC6D7B24D7" with the hash algorithm SHA1. Try it for yourself.
So if there is a file full of fragmented passwords, a brute force attack can be used, trying every character combination. This has become so common that there are websites that list common passwords alongside the (calculated) hash value. You can simply search for the hashed value to reveal the corresponding password.
Is complexity the solution?
As the capabilities of computers increase, complexity does not seem to be a problem.
The good news is that there are tools. Most computers now support the storage of passwords in either the operating system or the browser.
There are tons of apps that add the ability to store very difficult passwords that we can't remember. One of these solutions is Password manager KeePass.
Password managers like KeePassXC can help users create long, complex passwords and store them in a safe location.
There are of course vulnerabilities in everything, but this is a story once again.
Posted in The Conversation by Paul Haskell-Dowland, Associate Dean (Computing and Security), Edith Cowan University and Brianna O'Shea, Lecturer, Ethical Hacking and Defense, Edith Cowan University with permission Creative Commons. read the original article.





