The security company BitDefender he published information about a sideloading vulnerability in a OneDrive DLL that is currently being exploited, allowing cryptocurrency mining on vulnerable machines.

DLL hijacking is a common occurrence in Windows. Windows uses one system prioritys to determine from which location a DLL file is loaded if a full path is not specified by an application. DLL hijacking attacks abuse this system to install malicious files in a higher priority location. So the program will load the malicious DLL instead of the normal DLL file.
In the case of OneDrive, attackers use this idea by placing a malicious DLL file in the user's folder on the system. Specifically, a fake secure32.dll file is written to %LocalAppData%\Microsoft\OneDrive. This malicious dynamic link library is then loaded from two OneDrive processes: OneDrive.exe and OneDriveStandaloneUpdater.exe.
When the malicious DLL is loaded for the first time, it starts downloading cryptocurrency mining software onto the infected system.
“Once loaded into one of the OneDrive processes, the fake secure32.dll downloads open source cryptocurrency mining software and runs it in legitimate Windows processes.”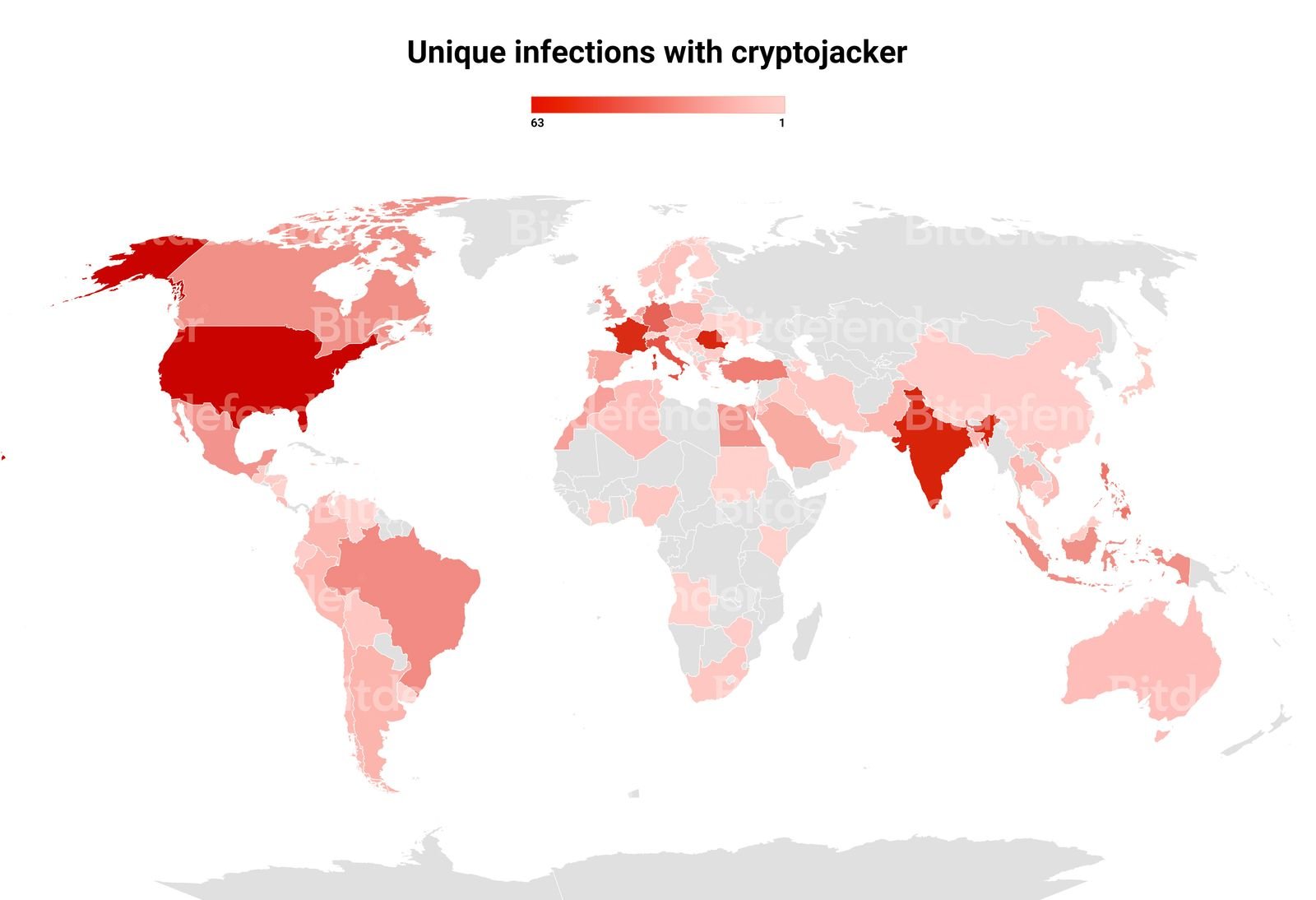
BitDefender reports that while the attack is currently limited to cryptocurrency mining, although attackers have options to carry out other malicious attacks, with ransomware or spyware.
The security company recommends that OneDrive be installed “per machine” and not “per user” on Windows computers to avoid the vulnerability.
Those who want to see if you are infected open the path %LocalAppData%\Microsoft\OneDrive\ in File Explorer and look for the file in the OneDrive directory.





