0Day on Twitter! Not in basements Forums, or on the Darkweb, but freely on Twitter and Github (now owned by Microsoft).
A big surprise awaited Microsoft when they announced that a zero-day vulnerability of theirs Windows, circulates freely on Twitter. The vulnerability allows an attacker to gain system privileges on computer of the victim. 
The tweet came from the account @SandboxEscaper. As you can see in the picture below, the researcher also published a link to Github that contained all the necessary for a successful PoC. 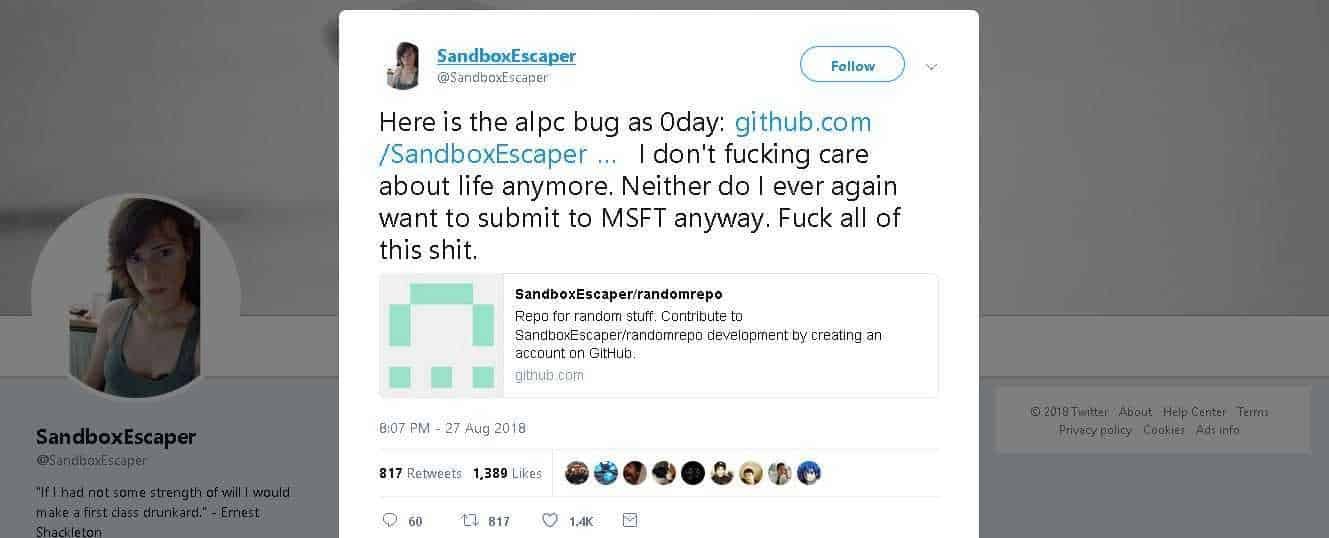
Of course, the Git link does not exist anymore, and it is a surprise that there is still a Twitter announcement.
CERT researcher Phil Dormann, confirmed the error on Twitter and explained that it worked on a "fully updated system with Windows 10 at 64bit."
A publication in CERT provides more details on vulnerability, but points out that there is still some information about the affected systems.
Microsoft, for its part, told The Registry that it is preparing a patch that is likely to be released on the next Patch Tuesday, 11 in September. The company is probably keeping the hours of its employees very tight and does not allow for overtime even if millions of systems are at risk.
Apparently all versions of Windows 10 are affected, regardless of whether they have been updated or not. Older versions of Windows, (Windows 7 and Windows 8.1), do not appear to be affected by this particular vulnerability.
Regarding the security of your system and until Microsoft decides to release the update to close the space of 0Day (by the book on the next Patch Tuesday), you should avoid downloading and running applications and files from unreliable sources.
_________________________________
- Keeper: Complaint about the publication of the vulnerability
- Modified NSA exploits also work on Windows 10
- Debian: A comprehensive guide to everything in English
- SUSE new custom kernel specifically for Microsoft Azure






Win 8.1 with start is back and full update. After the failed experiment to move from 7 to 10, it was the solution
:-)
another is the solution Lefteris…