Four new vulnerabilities have been identified in Intel processors and can be exploited via side-channel attacks. The vulnerabilities have been named RIDL, Fallout and ZombieLoad.
These vulnerabilities allow attackers to steal passwords access, encryption keys, or any other type of data that is loaded or stored in the CPU's buffer memory.
The vulnerabilities are categorized as Microarchitectural Data Sampling (MDS) and are identified by the following four CVEs:
- CVE-2018-12126 - Microarchitectural Store Buffer Data Sampling (MSBDS)
- CVE-2018-12130 - Microarchitectural Fill Buffer Data Sampling (MFBDS)
- CVE-2018-12127 - Microarchitectural Load Port Data Sampling (MLPDS)
- CVE-2019-11091 - Microarchitectural Data Sampling Uncacheable Memory (MDSUM)
The researchers who announced the vulnerabilities, in addition to naming them (sic) also created two different websites, where you can read more:
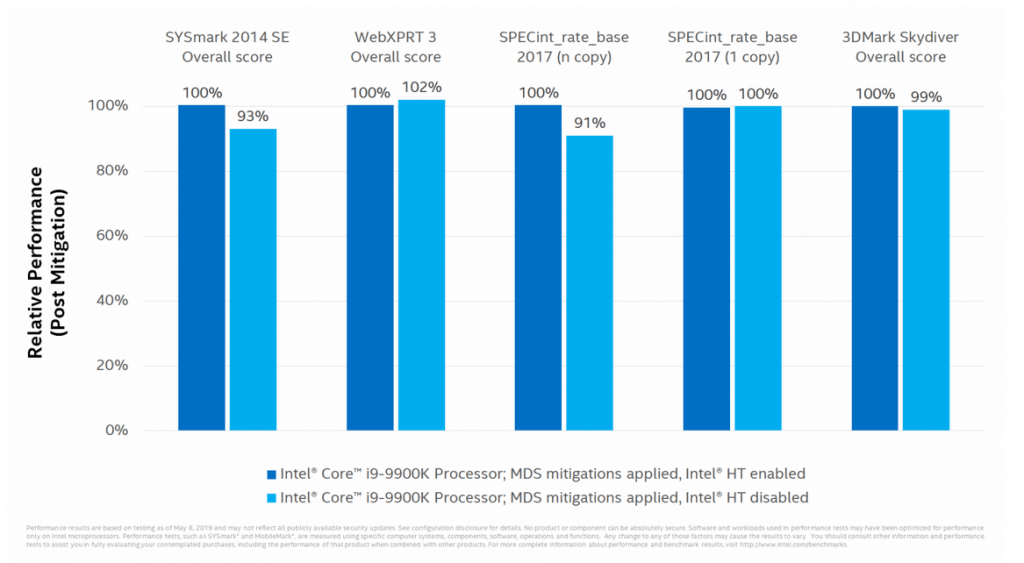
You should be aware that all repair solutions currently available are only mitigations and do not completely fix vulnerabilities. To fully resolve these vulnerabilities, all vendors state that you should disable hyper-threading, which will affect your computer.
Official MDS Advisories, Patches, or Updates:
- Amazon AWS
- Apple Lossless Audio CODEC (ALAC), advisory and security updates
- Citrix
- Chromium
- Intel
- Lenovo BIOS updates
Microsoft
- ADV190013 | Microsoft Guidance to Mitigate Microarchitectural Data Sampling vulnerabilities
- Windows guidance to protect against speculative execution side-channel vulnerabilities
Unfortunately no microcode updates are available for the following versions of Windows (and for Windows 10 version 1809, which will be released later):
- Windows 10 Version 1803 for x64-based Systems
- Windows Server, 1803 (Server Core Installation)
- Windows 10 Version 1809 for x64-based Systems
- Windows Server 2019
- Windows Server 2019 (Server Core Installation)
________________
_________________________
- Patch Tuesday May KB4494441, KB4499167, KB4499179 & KB4499181
- Kaspersky antivirus; Be careful, update immediately
- Zuckerberg: splitting Facebook will not help
- Android with digital identity is being prepared by Google





