Problems with Google Play: Researchers ESET discovered fake cryptocurrency apps, which use an unprecedented technique to bypass SMS-based 2FA authentication, thereby violating Google's recent SMS permission restrictions. In March 2019, Google restricted the use of SMS and Call Log permissions in Android apps to protect users from annoying apps with illegal purposes.
The applications, called "BTCTurk Pro Beta", "BtcTurk Pro Beta" and "BTCTURK PRO" imitate the Turkish cryptocurrency exchange BtcTurk and "fish" login credentials to the service. These malicious apps do not intercept SMS messages to bypass 2FA protection of user accounts and transactions, instead, they obtain the code one-time pass (OTP) from the notifications displayed on the screen of the compromised device.
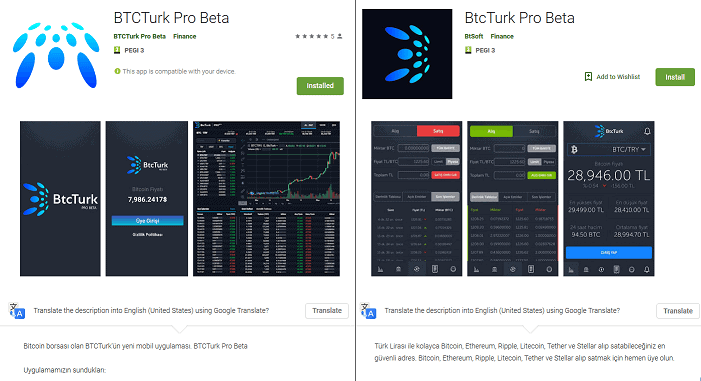
But in addition to the ability to "read" 2FA alerts, applications can also delete them, preventing victims from detecting illegal transactions. All three applications were uploaded to Google Play in June 2019 and were removed immediately after the ESET update.
Once installed and running, the fake applications request permission to access the notifications. They can then read notifications displayed by other applications installed on the device, reject them, or click buttons that contain them. According to ESET analysis, the cybercriminals behind these applications specifically target notifications from SMS and email applications.
"Thanks to the restrictions imposed by Google in March 2019, applications that stole login credentials had lost the ability to abuse the licenses they needed to bypass the mechanisms. 2FA based on SMS. However, by discovering these fake applications, we have for the first time seen malware bypass this restriction on SMS licenses, "said ESET researcher and author of the study, Lukáš ftefanko.
The right to access notifications appeared first on version Android Jelly Bean 4.3, which means that almost all active Android devices are vulnerable to this new technique. Fake BtcTurk apps can run on Android version 5.0 (KitKat) and above. This practically means that they affect about 90% of Android devices.
This technique has some limitations in terms of effectiveness in bypassing 2FA certification - intruders only have access to text that matches the text field of the alert, so it is not certain that the text will contain the OTP code. In SMS for 2FA, messages are generally short and OTP codes are likely to match the alert message. However, in 2FA emails, the length and format of the message is more varied, possibly affecting cybercrime access to the data.
ESET urges users who suspect they have used one of these malicious applications to uninstall them immediately by checking their account for suspicious transactions. To remain generally safe from any malware on Android, ESET provides the following advice:
- Trust cryptic and financial services applications only if they are linked to their official website.
- Enter the sensitive ones information online only if you are sure of their security and legality.
- Keep your device up to date.
- Use a reliable mobile security solution to block and remove threats.
- Prefer services generation of one-time-use codes (OTPs) based on software or a token device, rather than via SMS or email.
- Use only trusted applications, but even then, allow them to access notifications only if there is a good reason.
More details can be found in the relevant article by Lukáš ftefanko: «Malware sidesteps Google permissions policy with new 2FA bypass technique».