Η Check Point Research, published the latest World Threat List for June at 2019. The research team confirms that the Emotet (the largest network in operation bots at this time), is off, and most of June saw no new campaigns. That's it Emotet, during the first six months of 2019, it was in the top five malwares worldwide while distributed with major messaging campaigns spam (spam).
Check Point researchers believe Emotet may be out of service for maintenance and upgrades. In addition, they believe that once its servers are restored, they will be reactivated with new, improved features.

Maya Horowitz, Director of Check Point Information and Threat Research, said:
The Emotet appeared in the foreground as banking Trojan the 2014. However from 2018, we have seen it used as a botnet in large campaigns malspam, and used to share others malwares. Although its infrastructure was inactive for most of June, it remained in fifth place on the list of global threats, which proves how much it is being used - and is likely to reappear with new features.
and continued:
In the summer of 2017 and 2018 we noticed patterns of attacks they exploited banking Trojans. This demonstrates that cybercriminals are trying to exploit the tourist season and that users on holiday are less concerned with security practices, using online banking services from shared Appliances and from less secure connections.
Check Point: 3 most popular malware threats in June 2019:
* The arrows indicate the change in rank relative to the previous month.
-
↑ XMRig - XMRig is a software CPU mining open source code for the procedure partreatments of the Monero cryptocurrency that was first seen in circulation in May 2017.
-
↑ JSEcoin - JavaScript mining software that can be embedded into websites. With JSEcoin, you can run the mining software directly on program browsing in exchange for a browsing experience free of ads, game coins and other incentives.
-
↓ Cryptoloot - Encryption software that uses the power of the central processing unit (CPU) or graphics processor (GPU) and the victim's existing resources for cryptomining - adding transactions to the blockchain and generating new currencies. It competes with Coinhive, trying to oust it by demanding a lower percentage of revenue from the sites.
3 Most Popular Malware Threats in June 2019:
TLotoor continues to be at the top of the list of the most widespread malware threats on mobile devices. Here follows Triada and Ztorg, a new malware for the first time in the list.
-
↑ Lotoor Malware for Android, which adjusts legitimate applications and publishes them to third parties bedspread. Its main function is to display advertisements, however it is capable of accessing security information located in the operating system, allowing an attacker to obtain sensitive user data.
-
↓ Triada - Modular backdoor for Android that grants super user rights to downloaded malware, helping it integrate into system processes. Triada has also been observed to mislead URLs loaded into the browser.
-
↑ Ztorg - The Trojans belonging to the family Ztοrg, are gaining increasing privileges on devices Android and installed on directory of the system. The malware is able to install any other application on the device.
3 vulnerabilities 'most frequently exploited' for June 2019
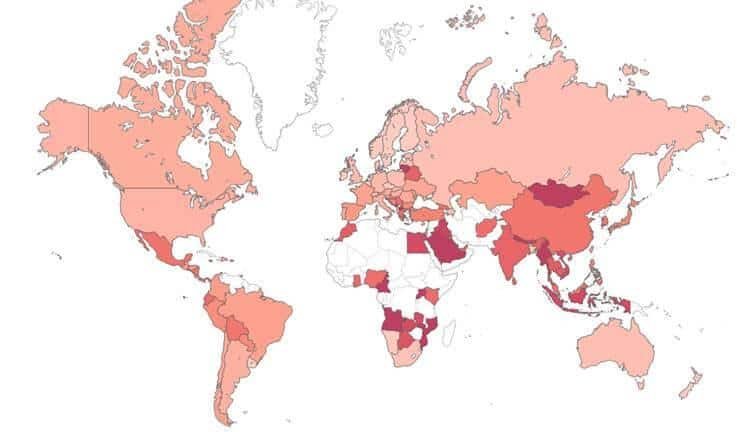
In June, SQL Injections techniques continued to be at the top of the list, affecting 52% of organizations worldwide. The vulnerability of OpenSSL TLS DTLS Heartbeat Information Disclosure came in second, affecting 43% of organizations worldwide, closely followed by CVE-2015-8562 with an impact on 41% of organizations worldwide.
-
- SQL Injection (various techniques) - This is the introduction of one SQL Query the data provided by client in an application, thereby exploiting a vulnerability that exists in the code of that application.
-
↑ OpenSSL TLS DTLS Heartbeat Information Disclosure (CVE-2014-0160; CVE-2014-0346) A vulnerability in disclosing information that exists in OpenSSL. The vulnerability is due to an error handling TLS / DTLS heartbeat packets. An attacker can exploit this vulnerability to disclose contents of the memory of a connected client or server.
-
↑ Joomla Object Injection Remote Command Execution (CVE-2015-8562)- A vulnerability related to remote platform command execution has been reported Joomla. The vulnerability exists due to a lack of validation on imported objects, which could lead to remote code execution. A remote attacker could exploit this vulnerability by sending a malicious request to the victim. Successful exploitation of this vulnerability could result in the execution of arbitrary code on the part of the target user.
* The complete list of the most common malware threats worldwide 10 can be found here.
_________________________
- Windows 10 Build 18950 ISO: Snip & Sketch with zoom!
- Facebook Like EU: everyone who uses it is responsible
- Comodo Antivirus is released with vulnerabilities





